

Media access control. Functions performed in the MAC sublayer[edit] According to IEEE Std 802-2001 section 6.2.3 "MAC sublayer", the primary functions performed by the MAC layer are:[1] Frame delimiting and recognitionAddressing of destination stations (both as individual stations and as groups of stations)Conveyance of source-station addressing informationTransparent data transfer of LLC PDUs, or of equivalent information in the Ethernet sublayerProtection against errors, generally by means of generating and checking frame check sequencesControl of access to the physical transmission medium In the case of Ethernet, according to 802.3-2002 section 4.1.4, the functions required of a MAC are:[2] receive/transmit normal frameshalf-duplex retransmission and backoff functionsappend/check FCS (frame check sequence)interframe gap enforcementdiscard malformed framesappend(tx)/remove(rx) preamble, SFD (start frame delimiter), and paddinghalf-duplex compatibility: append(tx)/remove(rx) MAC address See also[edit]

Church of Wifi. Base64 Online - base64 decode and encode. This online sample demonstrates functionality of a base64 property, ByteArray class and Huge asp file upload.
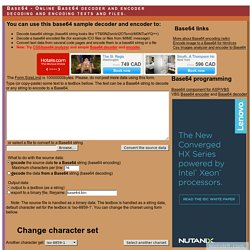
You can convert texts using several code pages (using CharSet property) from Unicode string to byte array and then convert the binary data to a Base64 string. The sample uses a special Base64 algorithm written for the ByteArray class. The Base64 conversion algorithm is written in C++ and works with binary (VT_ARRAY | VT_UI1) and String (BSTR) OLE data. It contains hi-speed and low-memory consumption BSTR->BSTR, BSTR->BINARY, BINARY->BSTR and BSTR->BSTR algorithms.
Source code of the coding algorithm is available within distribution license of a ScriptUtilities library. Another online samples (utilities, converting, upload) On-line base64 decoder and encoder - let's you convert text data and files from/to a Base64 string. Wild Packets. Cain & Abel. Cain & Abel is a password recovery tool for Microsoft Operating Systems.

It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks, recording VoIP conversations, decoding scrambled passwords, recovering wireless network keys, revealing password boxes, uncovering cached passwords and analyzing routing protocols. The program does not exploit any software vulnerabilities or bugs that could not be fixed with little effort. It covers some security aspects/weakness present in protocol's standards, authentication methods and caching mechanisms; its main purpose is the simplified recovery of passwords and credentials from various sources, however it also ships some "non standard" utilities for Microsoft Windows users.
Getting_started. Version: 1.01 September 25, 2009 By: darkAudax Many people ask “How do I get started?”. This tutorial is intended to answer that question. It is not intended to be a detailed “How To” tutorial, rather it is a road map to get you from where you are to the desired destination of using aircrack-ng.
Once you get going, there is an abundance of materials on the wiki describing the tools in great detail and tutorials for various tasks. Do-It-Yourself Wi-Fi Antennas Update and Wi ... How to crack WEP with Intel PRO/Wireless 3945ABG. How to crack WEP with Intel PRO/Wireless 3945ABG is a task that can employ you for a long time. The Intel PRO/Wireless 3945ABG network adapter driver that comes from the manufacturer does not provide packet injection and network monitoring capabilities which are needed to crack WEP, and therefore before you attempt WEP cracking efforts, you have to update your driver first which can be a daunting task.
What is WEP crack? First, let's explain some background to WEP cracking. WEP is short for Wired Equivalent Privacy or Wireless Encryption Protocol, and it is one of the measures in wireless security that were at the inception of wireless networking. WEP has been flawed since its inception, but because nothing better was available in the beginning of the Wi-Fi era, it was publicly implemented as "better to have flawed WEP than nothing at all. " Is WEP crack OK? Second, we have to talk about the legality of WEP cracking. My Wireless Cracking Tool. I’ve become a semi-expert on wireless networking and their security features.. and how to get around them. Before I continue I want to emphasize: The act of cracking encryption is not illegal just like picking a lock is not illegal. It is the unauthorized access of that network which is illegal, just like breaking and entering is illegal.
So. To sum it up, there are two types of encryption. The actual process or hacking into a network like this requires a suite of tools called the aircrack-ng suite. But, once you understand what you are doing, you will appreciate the tool I have written. [caption id=”attachment_137” align=”aligncenter” width=”500” caption=”Here is a screen shot of my tool cracking wep”] [/caption] Remember! Here is the download link to Kyle’s Wireless Cracking Tool.