


12 Tips For Students To Manage Their Digital Footprints 12 Tips For Students To Manage Their Digital Footprints contributed by Justin Boyle If you’ve scratched your head over suggestions to manage your ‘digital footprint,’ you aren’t the only one. A surprisingly large percentage of people have never even heard the phrase, let alone thought about how to manage theirs responsibly. The Definition Of A Digital Footprint Simply put, a digital footprint is the record or trail left by the things you do online. Luckily for us all, most of the major sources of personal information can be tweaked so we share only certain things with the general public. For students having grown up in a social/digital environment, helping them see where and how they’re vulnerable may be the most critical step. But after a little Google searching and social media dots connecting, just seeing the breadth of info about us that exists online is enough to spur them to action. What To Tell Your Students About Monitoring Their Digital Footprints: 11 Tips 1. 2. 3. 4. 5. 6. 7. 8.
3 Step plan for a digital makeover Who controls your online identity? Google or you? If your answer is Google, it's time to take control with this three step plan. Step 1) Analyze your digital footprint. Know what the internet says about you. Step 2) Determine a headline. i.e. Who do you want to be known as on the internet? Step 3) Update your digital image. Create your digital resume, profiles, images, and clean up anything you don't want out there using the sites below. Once you've updated your image, be patient.
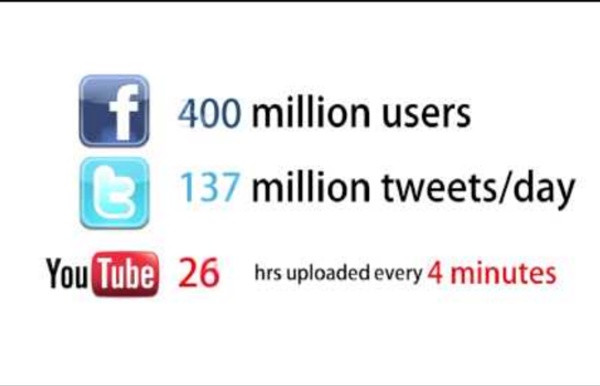
Fleas in a Bottle?: Will Social Networking Stymie Personal Development of Youth? | jhengstler's blog Recently I was giving a workshop on digital footprints at the CUEBC Conference Saturday at Simon Frazer University, Vancouver, BC. A digital footprint is the collection of all the traces you leave in electronic environments as you use or move through them. Some is content you actively volunteer—like your Facebook profile. We are living in an unprecedented era with regard to digital footprints. For those of us in our 30’s & 40’s, our digital footprints began at just about the same time we were entering mature adulthood. What will be the effects? When we were talking in the session, I likened it to growing up in a small town where everyone knows your business. Will the 3T’s (tweens, teens & twenty-somethings) of our time forever be constrained by the behavior they published on MySpace, Tagged, Bebo & Facebook—or that others have posted about them? One of the attendees looked at it from a different perspective: What will the impact of the perfect storm be on youth development? Like this:
Digital Birth: Welcome to the Online World AMSTERDAM--(BUSINESS WIRE)--Uploading prenatal sonogram photographs, tweeting pregnancy experiences, making online photo albums of children from birth, and even creating email addresses for babies - today’s parents are increasingly building digital footprints for their children prior to and from the moment they are born. “Our research shows that the trend is increasing for a child’s digital birth to coincide with and in many cases pre-date their real birth date. A quarter of babies have sonogram photos posted online before they have even physically entered into the world. ”Tweet this Internet security company AVG surveyed mothers in North America (USA and Canada), the EU5 (UK, France, Germany, Italy and Spain), Australia/New Zealand and Japan, and found that 81 percent of children under the age of two currently have some kind of digital profile or footprint, with images of them posted online. Key results USA - 92%Canada - 84% Australia - 84%New Zealand - 91%Japan - 43% USA - 33%Canada - 37%
Netiquette Module / Assessment - Group 5 Just as you are expected to exercise good etiquette/manners in the f2f classroom (raise your hand, listen to others, comment respectfully), you should do the same as an online learner. As defined by Ross of NetEtiquette, "'Netiquette' is network etiquette, the do's and don'ts of online communication. Netiquette covers both common courtesy online and the informal "rules of the road" of cyberspace." As your work through this assignment, you will discover the "Rules of Netiquette" which should be followed while in the online classroom - Discussion Board, Email and Chats. Assignment: 1) Read/view at least two of the following links: Classroom Netiquette – This is a Breeze presentation for middle/high school and college students which reinforces the correct Netiquette for learning to communicate online. 3) Assessment Activity: Based on your individual learning style, complete one of the following activities incorporating at least 5 rules of good netiquette. (Each activity is worth 10 pts.)
Muntatge i manteniment d'equips Quan els equips informàtics es troben en el període d’explotació del seu cicle de vida, la tasca més comuna d’un tècnic de manteniment de sistemes informàtics és la reparació de les avaries i l’assistència als usuaris en problemes de maquinari i de programari. Un equip informàtic és un dispositiu capaç d’acceptar dades per un mitjà d’entrada, processar-les sota el control d’un programa prèviament emmagatzemat en la memòria i retornar la informació obtinguda per un mitjà de sortida. Encara que l’administrador dels sistemes dugui a terme la seva tasca amb molta cura, en faci un repàs freqüent, els equips siguin fiables i els usuaris vagin amb compte amb l’ús del programari, pot passar que, en un moment determinat, algun equip tingui un funcionament incorrecte. Procés de resolució d'avaries El procés de resolució d'avaries Quan un sistema deixa de funcionar, s’ha d’actuar al més ràpidament possible. Memòria.
Guide to Computer Troubleshooting and Repair - PC Troubleshooting Manual There are six interactive troubleshooting flowcharts for PC hardware performance issues on this website, along with the related chapter text from the 2013 update of my book, "Computer Repair with Diagnostic Flowcharts Third Edition." The links below the miniature flowcharts take you to the full size interactive flowcharts. The diamond symbols on the full size flowcharts are linked to the text that expands on the decision and offers diagnostic tips and solutions. When I started working on PCs back in the mid-80's, there were thirty-six individual memory chips to be inserted in motherboard sockets. Guide to Computer Troubleshooting | If It Jams Home | Contact
troubleshooting flowchart How To Create Your Own Flowchart For Troubleshooting And Repairing Purposes Introduction So, what is a flowchart? According to the explanation from the Wikipedia- A flowchart is a common type of diagram, which represents an algorithm or process, showing the steps as boxes of various kinds, and their order by connecting these with arrows. In order for you to easily understand what is a flowchart, just look at the sample below: A typical example of a flowchart Is it necessary to have a flowchart for troubleshooting? If you are just starting out in this electronic repair field, then YES it is necessary to have this flowchart to help you out in troubleshooting purposes. Let’s take this for example, would you check on the power primary section when you already got all the good output voltages at the secondary side of the power supply? Any ideas where I can get the troubleshooting flowchart? 1) Service manuals 2) Troubleshooting and repairing books 3) Internet An example of a more specific flowchart
The Pros and Cons of Online Shopping Online shopping is more popular today than ever before. A report from the U.S. Census Bureau found that in the second quarter of 2021, an estimated $222.5 billion was spent in retail e-commerce sales. In 2011, for comparison, the estimated total for retail e-commerce sales was $47.5 billion. Due in part to new and growing technology, online shopping has become incredibly easy and convenient. While online shopping comes with a number of benefits, there are drawbacks to know about, too. ProsConvenienceGreater selectionEasy access to information ConsCan be more expensiveIncreases risk of fraudLeads to longer wait times Pros of Online Shopping Using your computer or another digital device for shopping needs can be convenient, offer more options to choose from, and provide you with insight you might not find in person at a store. Convenience The greatest benefit of online shopping is its convenience. Greater Selection Easy Access to Information Cons of Online Shopping Can Be More Expensive
Computer Power Supply Troubleshooting - ATX PC Power Supply Diagnostic Flowchart The power supply troubleshooting chapter below is from my book, "Computer Repair with Diagnostic Flowcharts, Third Edition." The updates related to power supply diagnostics include a rework of the decision tree and attempting to force a dead power supply on, something I left out of previous editions for fear of doing more harm than good. Note that these steps correspond with decision points on the flowchart and are reached directly by clicking on the diamond symbols. The text below cannot be read sequentially. The first step in the troubleshooting process is simply determining if the power supply is coming on. Return to Diagnostic Chart If your computer has a display connected, can you get a live screen, whether it's a simple text message or a colorful splash screen? Newer components like quad core processors and dual PCI Express video adapters have doubled the power requirements of typical gaming PCs. Beep codes are reported out by the motherboard BIOS diagnostics at power up.
The Largest List of Chat Acronyms and Text Message Shorthand (IM, SMS) found of the Web - updated daily by NetLingo The Internet Dictionary: Online Dictionary of Internet Terms, Acronyms, Text Messaging, Smileys ;-) !I have a comment#FFFollow Friday(U)it means arms around you, hug for you*$Starbucks**//it means wink wink, nudge nudge,!!!!Talk to the hand/R/Requesting02Your (or my) two cents worth, also seen as m.0210QThank you1174Nude club121One to one123it means I agree1337Elite -or- leet -or- L33714it refers to the fourteen words142n8lyUnfortunately143I love you1432I Love You Too14AA41One for All and All for One182I hate you187it means murder/ homicide190 hand1dafulit means wonderful1V4One Vs.
Help Desk Frequently Asked Questions | Bloomfield College This is the Bloomfield College Helpdesk FAQ section. Here, you will find answers to the most commonly asked questions. Topics include, but are not limited to: GmailID CardsMoonlightPaperCutPassword ResetsWebAdvisor For the full list of questions, feel free to download our FAQ list here: Bloomfield College Helpdesk FAQ IT Help Desk FAQ's Gmail What is my email address? PaperCut What is my email address? Where do I log in? Can I use my Smartphone with Gmail? What do I do if I forget my password? How can I change my password if I know my current password? How long will I keep my email address? How much space do I have on my Google account? How do I mark messages as “unread” in my inbox after I open it? Can I reply to or forward just a single message in a conversation? Is there a size or type limitation for file attachments in Gmail? How long do messages stay in my Spam folder? How do I prevent messages from specific senders from being tagged as spam? How long do messages stay in the Trash?
How to Tell a Hardware Problem From a Software Problem Your computer seems to be malfunctioning — it’s slow, programs are crashing or Windows may be blue-screening. Is your computer’s hardware failing, or does it have a software problem that you can fix on your own? This can actually be a bit tricky to figure out. Hardware problems and software problems can lead to the same symptoms — for example, frequent blue screens of death may be caused by either software or hardware problems. Computer is Slow We’ve all heard the stories — someone’s computer slows down over time because they install too much software that runs at startup or it becomes infected with malware. If a computer is slowing down, it has a software problem that can be fixed. Blue Screens RELATED: Everything You Need To Know About the Blue Screen of Death Modern versions of Windows are much more stable than older versions of Windows. If you are encountering frequent blue screens of death, there’s a good chance your computer’s hardware is failing. Computer Won’t Boot
Anatomy of a URL In February 2010, techy web magazine Read Write Web published an article entitled Facebook Wants to Be Your One True Login. The article was about a new partnership between Facebook and AOL aimed at making it easier for users to log in to Facebook. Which is quite ironic considering what happened next. Soon after it was published, the article somehow managed to reach number one in Google for the search term Facebook log in. So when thousands of people started landing on this Read Write Web page, believing it was the Facebook log in page, they proceeded to log in! What's wrong with this situation? They didn't check the URL? Evidently not. What is a URL? URL stands for Uniform Resource Locator, or in other words, the web address of an online resource, i.e. a web site or document. Web browsers display the URL in the address bar Every website you visit has a URL. The URL is created in one of two ways ♫The protocol's connected to the domain name and the domain name's connected to the file path Port ?