

Configure ASA: SSL Digital Certificate Installation and Renewal. Introduction This document describes the various operations to successfully install and use a third-party trusted Secure Socket Layer (SSL) digital certificate on the Adaptive Security Appliance (ASA) for Clientless SSLVPN and the AnyConnect client connections.
A GoDaddy Certificate is used in this example. Each step contains the Adaptive Security Device Manager (ASDM) procedure and the CLI equivalent. Prerequisites Requirements This document requires access to a trusted third-party Certificate Authority (CA) for certificate enrollment. Before you start, verify that the ASA has the correct clock time, date, and time zone. ASA Anyconnect VPN and OpenLDAP Authorization with Custom Schema and Certificates Configuration Example. Configure ASA: SSL Digital Certificate Installation and Renewal. Configure Anyconnect with LDAP Authenti... Configuring Cisco SSL VPN AnyConnect (WebVPN) on Cisco IOS Routers. Our Web SSL VPN article written back in 2011 introduced this new wave of VPN services.

This article extends the topic by covering the installation and configuration of Cisco’s SSL AnyConnect VPN for Cisco IOS Routers. Web SSL VPN delivers the following three modes of SSL VPN access: • Clientless - Clientless mode provides secure access to private web resources and will provide access to web content. This mode is useful for accessing most content that you would expect to access in a web browser such as Internet access, web-based intranet, webmail etc. • Thin Client (port-forwarding Java applet) - Thin client mode extends the capability of the cryptographic functions of the web browser to enable remote access to TCP-based applications such as Post Office Protocol version 3 (POP3), Simple Mail Transfer Protocol (SMTP), Internet Message Access protocol (IMAP), Telnet and Secure Shell (SSH). AnyConnect: Configure Basic SSLVPN for IOS Router Headend With the Use of CLI. Introduction This document describes the basic configuration of a Cisco IOS Router as an AnyConnect SSLVPN Headend.
Prerequisites Requirements. Cisco ASA – VPN AnyConnect. Dans cet article nous verrons comment configurer un VPN AnyConnect, permettant à des clients de se connecter à distance au réseau local de l’ASA.
Le VPN AnyConnect est la solution la plus mise en avant par Cisco en ce moment. Elle a l’avantage d’être simple est légère pour le client. En revanche, les licences sont couteuses. Nous ne débâterons pas ici sur ses avantages et inconvénients. Voyons tout de suite la configuration. SSL VPN Configuration Guide, Cisco IOS Release 15M&T - SSL VPN [Support] SSL VPN supports the following types of licenses: Permanent licenses—No usage period is associated with these licenses.
![SSL VPN Configuration Guide, Cisco IOS Release 15M&T - SSL VPN [Support]](http://cdn.pearltrees.com/s/pic/th/configuration-release-support-144965123)
All permanent licenses are node locked and validated during installation and usage. Evaluation licenses—These are metered licenses that are valid for a limited period. The usage period of a license is based on a system clock. The evaluation licenses are built into the image and are not node locked. For all the license types, except the evaluation license, a EULA has to be accepted during the license installation. Cisco ASA 5520 SSL Installation Instructions. If you have not yet created a Certificate Signing Request (CSR) and ordered your certificate, see SSL Certificate CSR Creation for Cisco ASA 5500 VPN.

As a way of helping you to manage the certificate chain that will be sent out to clients, you are required to create a trustpoint for each certificate in the chain that is sent out. You will first need to create trustpoints for the two intermediate certificates DigiCertCA2.crt, and DigiCertCA.crt Open the Cisco ASDM, then Under the Remote Access VPN window pane, then in the Configuration tab, expand Certificate Management and click 'CA Certificates'.
Click the 'Add' button. Assign a 'Trustpoint Name' to the certificate (e.g. The ADSM will then show your certificate details under trustpoint. FlexVPN and Anyconnect IKEv2 Client Configuration Example. Introduction This document describes how to configure Cisco AnyConnect Secure Mobility Client to use Remote Authentication Dial-In User Service (RADIUS) and local authorization attributes in order to authenticate against Microsoft Active Directory.
Note: Currently, use of the local user database for authentication does not function on Cisco IOS® devices. This is because Cisco IOS does not function as an EAP authenticator. Enhancement request CSCui07025 has been filed to add support. Prerequisites Requirements. Configure ASA: SSL Digital Certificate Installation and Renewal. Introduction This document describes the various operations to successfully install and use a third-party trusted Secure Socket Layer (SSL) digital certificate on the Adaptive Security Appliance (ASA) for Clientless SSLVPN and the AnyConnect client connections.

A GoDaddy Certificate is used in this example. Each step contains the Adaptive Security Device Manager (ASDM) procedure and the CLI equivalent. Prerequisites Requirements This document requires access to a trusted third-party Certificate Authority (CA) for certificate enrollment. Before you start, verify that the ASA has the correct clock time, date, and time zone. SSL/TLS Certificate Installation Instructions - Cisco ASA SSL VPN — Technote Article — Entrust. Entrust Certificate Services Support Knowledge Base Audience: GeneralLast Modified: 2015-11-25 15:39:32.0.
Data Center and Network Technobabble: Cisco AnyConnect VPN 3.1 Untrusted VPN Server Certificate Installation. If you've upgraded your Cisco AnyConnect VPN Client to 3.1, you might run into the following warning pop up when you attempt to establish a VPN connectivity.
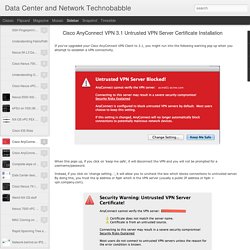
When this pops up, if you click on 'keep me safe', it will disconnect the VPN and you will not be prompted for a username/password. Instead, if you click on 'change setting…', it will allow you to uncheck the box which blocks connections to untrusted server. By doing this, you trust the ip address or fqdn which is the VPN server (usually a public IP address or fqdn = vpn.company.com). After the previous image, the above pop up shows up. 'Connect anyway' will complete the VPN connection.
Why do these security warnings show up in the first place? Cisco made some changes to their Server Certificate Verification on 3.1. "–If a Subject Alternative Name extension is present with relevant attributes, name verification is performed solely against the Subject Alternative Name. How do you make these disappear? Cisco AnyConnect - With Google Authenticator 2 Factor Authentication. KB ID 0001256 Dtd 09/11/16 Problem This was asked as a question on Experts Exchange this week, and it got my interest. A quick search turned up a bunch of posts that said, yes this is possible, and you deploy it with FreeRADIUS and it works great.
The problem was, a lot of the information is a little out of date, and some of it is 'wrong enough' to make the non-technical types give up. But I persevered, and got it to work. Disclaimer: This is not an exercise in deploying AnyConnect, I've got that covered to death all over the website, use the search function above, or simply go to the following article; Configure Anyconnect with LDAP Authentication. Introduction: This document provides step-by-step instructions on how to allow Cisco AnyConnect VPN client access to the Internet while they are tunneled into a Cisco Adaptive Security Appliance (ASA) 8.4(2). This configuration allows the client secure access to corporate resources via SSL while giving unsecured access to the Internet using split tunneling. This document will also give you information on how to use LDAP for user authentication. Prerequesites: KB0000943 - Cisco ASA 5500 AnyConnect Setup From Command Line.
KB ID 0000943 Dtd 21/04/14 Problem Also See Cisco ASA5500 AnyConnect SSL VPN This procedure was done on Cisco ASA version 8.4, so it uses all the newer NAT commands. I'm also going to use self signed certificates so you will see this error when you attempt to connect. CLI Book 3: Cisco ASA Series VPN CLI Configuration Guide, 9.6 - AnyConnect VPN Client Connections [Cisco ASA 5500-X Series Firewalls] The Cisco AnyConnect Secure Mobility Client provides secure SSL and IPsec/IKEv2 connections to the ASA for remote users. Without a previously-installed client, remote users enter the IP address in their browser of an interface configured to accept SSL or IPsec/IKEv2 VPN connections.
Unless the ASA is configured to redirect requests to users must enter the URL in the form After entering the URL, the browser connects to that interface and displays the login screen. If the user satisfies the login and authentication, and the ASA identifies the user as requiring the client, it downloads the client that matches the operating system of the remote computer. After downloading, the client installs and configures itself, establishes a secure SSL or IPsec/IKEv2 connection and either remains or uninstalls itself (depending on the configuration) when the connection terminates. Cisco AnyConnect Secure Mobility Client Administrator Guide, Release 4.0 - Configure VPN Access [Cisco AnyConnect Secure Mobility Client]
AnyConnect integrates support for RSA SecurID client software versions 1.1 and later running on Windows 7 x86 (32-bit) and x64 (64-bit). RSA SecurID software authenticators reduce the number of items a user has to manage for safe and secure access to corporate assets. RSA SecurID Software Tokens residing on a remote device generate a random one-time-use passcode that changes every 60 seconds. The term SDI stands for Security Dynamics, Inc. technology, which refers to this one-time password generation technology that uses hardware and software tokens. Typically, users make an AnyConnect connection by clicking the AnyConnect icon in the tools tray, selecting the connection profile with which they wish to connect, and then entering the appropriate credentials in the authentication dialog box. Purchase SSL Certificate. Configure ASA as a Local CA Server and AnyConnect Headend. Introduction This document describes how to setup a Cisco Adaptive Security Appliance (ASA) as a Certificate Authority (CA) server and as a Secure Sockets Layer (SSL) gateway for Cisco AnyConnect Secure Mobility Clients.
Prerequisites Requirements Cisco recommends that you have knowledge of these topics: Basic ASA configuration that runs software version 9.1.xASDM 7.3 or higher Components Used The information in this document is based on these software and hardware versions: Cisco 5500 Series ASA that runs software version 9.1(6)AnyConnect Secure Mobility Client version 4.x for WindowsPC which runs an supported OS per the Compatibility Chart.Cisco Adaptive Security Device Manager (ASDM) version 7.3 Note: Download the AnyConnect VPN Client package (anyconnect-win*.pkg) from the Cisco Software Download (registered customers only) .
The information in this document was created from the devices in a specific lab environment. Background Information Guidelines and Limitations Configure Network Diagram. KB0000335 - Securing Cisco SSL VPN's with Certificates. KB ID 0000335 Dtd 01/10/10 Problem It's been a while since I wrote a walk though on the Cisco AnyConnect/SSL VPN solution, and usually I secure these with Active Directory or simply using the local user database on the firewall. But what if you wanted to use certificates instead? Perhaps your users are too "technically challenged" to remember their passwords.
AnyConnect to IOS Headend Over IPsec with IKEv2 and Certificates Configuration Example. What is SSL VPN (Secure Sockets Layer virtual private network)? - Definition from WhatIs.com.