

Welcome to Forbes. The Stingray: the cellphone tracker the government won't talk about. The government has the ability to track cellphones using the portable device pictured above called the Stingray — it was recently revealed in a criminal case in Arizona, but the government doesn't want anyone to know how it works.

When the judge in the case asked for more information about the Stingray in order to determine if its use requires a search warrant, the government filed a memo basically arguing both ways: it said Stingray use generally doesn't require a warrant, but concedes that one was required in this specific instance — a huge concession that could cost them the case, just so the Stingray's design and functionality remain a secret. Although the government's lawyers are willing to tie themselves in knots trying to conceal the Stingray, we do have some information on how it works: experts told the WSJ that it mimics an actual cell tower pinging for a specific device, and the data can be used to triangulate a phone's location.
Met police using surveillance system to monitor mobile phones. Britain's largest police force is operating covert surveillance technology that can masquerade as a mobile phone network, transmitting a signal that allows authorities to shut off phones remotely, intercept communications and gather data about thousands of users in a targeted area.

The surveillance system has been procured by the Metropolitan police from Leeds-based company Datong plc, which counts the US Secret Service, the Ministry of Defence and regimes in the Middle East among its customers. Strictly classified under government protocol as "Listed X", it can emit a signal over an area of up to an estimated 10 sq km, forcing hundreds of mobile phones per minute to release their unique IMSI and IMEI identity codes, which can be used to track a person's movements in real time. The disclosure has caused concern among lawyers and privacy groups that large numbers of innocent people could be unwittingly implicated in covert intelligence gathering. Datong declined to comment. SHR. What is SHR ?
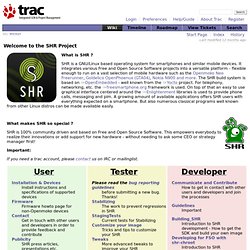
SHR is a GNU/Linux based operating system for smartphones and similar mobile devices. It integrates various Free and Open Source Software projects into a versatile platform - flexible enough to run on a vast selection of mobile hardware such as the Openmoko Neo Freerunner, Goldelico OpenPhoenux (GTA04), Nokia N900 and more. The SHR build system is based on OpenEmbedded - well known from the Yocto project. For telephony, networking, etc. the freesmartphone.org framework is used.
On top of that an easy to use graphical interface centered around the Enlightenment libraries is used to provide phone calls, messaging and pim. What makes SHR so special ? SHR is 100% community driven and based on Free and Open Source Software. Important: If you need a trac account, please contact us on IRC or mailinglist. Installation & Devices Install instructions and specifications of supported devices Firmware Firmware howto page for non-Openmoko devices Contact Publicity Pictures and Videos Weekly News.
Hackers crack crypto for GPRS mobile networks. High performance access to file storage A cryptographer has devised a way to monitor cellphone conversations by exploiting security weaknesses in the technology that forms the backbone used by most mobile operators.

Karsten Nohl, chief scientist of Berlin-based Security Research Labs, said the attack works because virtually all of the world's cellular networks deploy insecure implementations of GPRS, or general packet radio service. Some, such as those operated by Italy's Wind or Telecom Italia, use no encryption at all, while Germany's T-Mobile, O2 Germany, Vodafone, and E-Plus use crypto that's so weak that it can easily be read by unauthorized parties. Le lobby des opérateurs s’impose à Bruxelles. Aujourd'hui la commissaire au numérique va donner raison au lobby des télécoms.

Les documents confidentiels obtenus par OWNI décrivent leur redoutable offensive des semaines passées. L’Internet du futur sera celui des opérateurs. La commissaire européenne en charge du numérique Neelie Kroes s’apprête en effet à trancher ce 13 juillet unilatéralement en faveur du scénario ficelé par les opérateurs de télécommunication pour “atteindre les objectifs du Digital Agenda for Europe“. Une position allant au-delà des derniers communiqués de la Commission, plus ambigus, sur Internet. Au menu, le programme rêvé des opérateurs: gestion différenciée du trafic Internet, promotion de plusieurs degrés de qualité de service, mais aussi participation des fournisseurs de services (autrement dit, les sites) au financement des infrastructures. Un triumvirat telco-centré pour les diriger tous Des modèles de co-investissements seront promus (cela devrait impliquer au moins deux parties).
L’alibi du “best-effort”