

IrfanView - Official Homepage - one of the most popular viewers worldwide. 10 Useful Google Spreadsheet Formulas You Must Know. The “Gentlemen’s” Take On Facebook. 30 Useful (and Unknown) Web Apps You Need to Bookmark - Page 2.
FillAnyPDF FillAnyPDF is a fairly simple web app which allows you to upload a PDF file, then easily write on it wherever you want.

This allows you to easily fill out any form, even if they’re not in an editable PDF form. You can also share your blank form with others, so you can collect forms from a group easily. Learn to Code: The Full Beginner's Guide. Stack Overflow. Programmer 101: Teach Yourself How to Code. Cyber xtreme Resources and Information. This website is for sale! Virtual private network. VPN connectivity overview A virtual private network connection across the Internet is similar to a wide area network (WAN) link between sites.
From a user perspective, the extended network resources are accessed in the same way as resources available within the private network.[2] VPNs allow employees to securely access their company's intranet while traveling outside the office. Similarly, VPNs securely connect geographically disparate offices of an organization, creating one cohesive network. VPN technology is also used by Internet users to connect to proxy servers for the purpose of protecting personal identity and location. Types[edit] Early data networks allowed VPN-style remote connectivity through dial-up modems or through leased line connections utilizing Frame Relay and Asynchronous Transfer Mode (ATM) virtual circuits, provisioned through a network owned and operated by telecommunication carriers.
VPN systems may be classified by: Security mechanisms[edit] Authentication[edit] At a Cafe? I Can Hack Your Facebook, Twitter, Etc...With a Firefox Extension. Whenever you connect to an unsecured WiFi network, you're taking a chance, but now it's easier than ever for someone to gain access to all of your social network login information.
A new Firefox extension called Firesheep makes it simple for anyone to see that you're connected to the network, grab your login information for any number of social networks, and take over your online identity. Without this, hacking your account over an unsecured wireless network may not be rocket science, but it surely isn't the one-click magic made possible by Firesheep. Firesheep takes advantage of unsecured wireless networks and unencrypted cookies to "sidejack", or gain access to sites by way of accessing these cookies. Developed by Eric Butler, a freelance web application and software developer in Seattle, Washington, Firesheep was created and released at Toorcon 12 to demonstrate the security risk inherent in storing unencrypted login data in cookies. How to install Android on your Netbook/PC.
UPDATED – Using Googles Full Capabilities « XBOX, XBOX 360, PS2, PS3, PSP, & MORE! – Your source for the latest in console modding. Here is an updated version of the ‘Using Google’s Full Capabilities’.
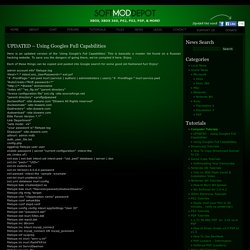
157 of the Most Useful Websites on the Internet.
Programing & Software. Top 50 Programming Quotes of All Time. Public Domain Movie Torrents with PDA iPod Divx PSP versions. Are your search engine queries being hijacked? Who doesn't trust their search engine?

When we need to find something, we all turn to Google, Bing, or Yahoo. We shouldn't be so trusting through. On Bing, cyber-crooks are now placing ads to ensnare people who want to switch to the Chrome Web-browser. Now, we find that some U.S. Internet Service Providers (ISP)s are sending your search queries to a third-party proxy company instead of your search engine of choice.
According to the Electronic Frontier Foundation (EFF), several recent research studies have revealed that "some or all traffic to major search engines, including Bing, Yahoo! Further research by the EFF and the ICSI Networking Group, a non-profit organization that researches Internet architecture and related networking issues, has revealed that your searches are sent to a company called Paxfire. Paxfire proudly proclaims itself to be the "proven industry leader in monetizing Address Bar Search and DNS Error traffic for Network Operators. Related Stories: Web tool's.
What can you learn on youtube? - Tomash.soup. World’s First Computer Rebuilt, Rebooted After 2,000 Years. Painting by Numbers - Microsoft Malware Protection Center. The MMPC came across an interesting piece of social engineering today that embeds a malicious script, which has been observed circulating on 4chan message boards.

On further investigation, it became apparent that this is the next stage in the evolution of a threat known as 4chan.js that has been around since 2008. This scenario relies on a user's trust of image file formats and an unfamiliarity of the .HTA format (by the way, HTA stands for HTML Application). The user is sent a .PNG file that looks similar to the following screenshots: The .PNG file stores the data in a compressed format that is quite innocuous. Did you notice the fuzz at the bottom of the images shown above? The Ultimate List: 40 Social Networking Sites Specifically for Small Business, Entrepreneurs, and Startups. We all know of the huge social networking sites like Twitter and Facebook.

They’re great for large scale connections and discussion. But, as entrepreneurs and small business owners sometimes it’s nice to connect with other like minded individuals in a smaller, more focused setting. If that sounds like what you are looking for in a social network, the below list is for you. We’ve scoured the Internet looking for social networking sites specifically for small businesses, entrepreneurs and startups, and found 40 we feel are worth a look. 1. Your Polldaddy Contents. Youtube Video Downloader. Microsoft Surface 2 imminent: more than a big iPad with legs. Interacting with Microsoft Surface version 2, built by Samsung.

Photo: Bloomberg The Australian launch of Microsoft's new intelligent touch-screen table is imminent, sources say - the company's second attempt after its first Surface product bombed. 70 Things Every Computer Geek Should Know. The term ‘geek’, once used to label a circus freak, has morphed in meaning over the years. What was once an unusual profession transferred into a word indicating social awkwardness. As time has gone on, the word has yet again morphed to indicate a new type of individual: someone who is obsessive over one (or more) particular subjects, whether it be science, photography, electronics, computers, media, or any other field. A geek is one who isn’t satisfied knowing only the surface facts, but instead has a visceral desire to learn everything possible about a particular subject.
A techie geek is usually one who knows a little about everything, and is thus the person family and friends turn to whenever they have a question. What Are Websites Made Of? (Infographic) MOVIE BITES – QUIDDITCH PLAYER’S PIE. Musical pairing – The Quidditch Match by John Williams I am completely in love with the world of Harry Potter.

I wear my Gryffindor scarf with pride. I pick up sticks when I’m on walks with my husband just to wave them in the air at him and say “Expelliarmus!” When we visited The Wizarding World of Harry Potter last October, I literally went running through the park like some sort of crazed madwoman just to get to the ride “Harry Potter and the Forbidden Journey.” CSSDesk - Online CSS Sandbox. Stolen Camera Finder - find your photos, find your camera.