

Free Online Computer Science and Programming Books, Textbooks, and Lecture Notes. Appendix D. Appendix Purpose and Scope This Appendix to the C++ Programming book will attempt to provide users a complementary understanding of the C++ programming language.

It will be interconnected and dependent on the lessons and theoretical content already presented on the C++ Programming book but at the same time will attempt to remain as self contained as possible to enable the series of exercises and problems to be used alone in practical/laboratory classes. This is an open work, if you find any problems with terms or concepts you can help by contribute to it, your participation is needed and welcomed! You are also welcome to state any preference, shortcomings or vision for the actual book content, structure or other conceptual matters, see this Wikibook's discussion page for the right forum for participating. C++ Programming/Exercises/Iterations. Iterations[edit] Solutions requirements.
Borland C++ Compiler version 5.5 Free Download Is Here !!! How to be a Programmer: A Short, Comprehensive, and Personal Summary. Debugging is the cornerstone of being a programmer.

The first meaning of the verb to debug is to remove errors, but the meaning that really matters is to see into the execution of a program by examining it. A programmer that cannot debug effectively is blind. Idealists that think design, or analysis, or complexity theory, or whatnot, are more fundamental are not working programmers. The working programmer does not live in an ideal world. Even if you are perfect, your are surrounded by and must interact with code written by major software companies, organizations like GNU, and your colleagues. Debugging is about the running of programs, not programs themselves. To get visibility into the execution of a program you must be able to execute the code and observe something about it. The common ways of looking into the ‘innards’ of an executing program can be categorized as: Scirus - for scientific information.
WTF Code.
Create Beautiful Hair-like Abstract Lines to Decorate Your Design in Photoshop. Create Beautiful Hair-like Abstract Lines to Decorate Your Design in Photoshop In this tutorial, I will show you the process of creating Beautiful Hair-like Abstract Lines to Decorate Your Design in Photoshop.
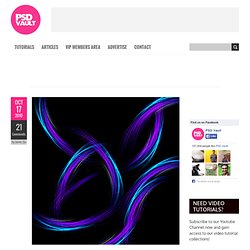
This is a beginner level tutorial with the aim of teaching how you to utitilise the Pen Tool and dynamic brush settings. Have a try :) Previously I published a tutorial called “Create Beautiful Surreal Photo Effect via Cloud, Star and Vexel Hair in Photoshop” and received a number of emails about the vexel hair part, which requires extensive use of Pen Tool. As a result, I decided to create a new tutorial showing more details about it, but with a different effect which you can use in a wider range of occasions (such as Photoshop retouch, web graphics and so on).
Here is a preview of the final result: (click to enlarge) PSD File Download You can download the PSD File for this tutorial via the VIP Members Area for only $6.95/Month (or less)! OK let’s get started! Step 1 Step 2 Step 3 Step 4. Sorting. WebMatrix. OnlySoftwareGr. Best Programming Quotations. A good programmer is someone who looks both ways before crossing a one-way street. -- Doug Linder, systems administrator A most important, but also most elusive, aspect of any tool is its influence on the habits of those who train themselves in its use.
If the tool is a programming language this influence is, whether we like it or not, an influence on our thinking habits. -- Edsger Dijkstra, computer scientist. Best Hacking Softwares_ 1000sw(Free download) - www.crack$hack.ws. Visual Cryptography. What is Visual Cryptography Visual Cryptography is a special encryption technique to hide information in images in such a way that it can be decrypted by the human vision if the correct key image is used.

The technique was proposed by Naor and Shamir in 1994. Visual Cryptography uses two transparent images. One image contains random pixels and the other image contains the secret information. It is impossible to retrieve the secret information from one of the images. When the random image contains truely random pixels it can be seen as a one-time pad system and will offer unbreakable encryption. How Visual Cryptography works Each pixel of the images is divided into smaller blocks. Tutorial - Learn Python in 10 minutes. NOTE: If you would like some Python development done, my company, Stochastic Technologies, is available for consulting.

This tutorial is available as a short ebook. The e-book features extra content from follow-up posts on various Python best practices, all in a convenient, self-contained format. All future updates are free for people who purchase it. Preliminary fluff So, you want to learn the Python programming language but can't find a concise and yet full-featured tutorial. Properties Python is strongly typed (i.e. types are enforced), dynamically, implicitly typed (i.e. you don't have to declare variables), case sensitive (i.e. var and VAR are two different variables) and object-oriented (i.e. everything is an object). Getting help. Algorithms.