

SSH Tunnel - Local and Remote Port Forwarding Explained With Examples - Trackets Blog. There are two ways to create an SSH tunnel, local and remote port forwarding (there’s also dynamic forwarding, but we won’t cover that here).

The best way to understand these is by an example, let’s start with local port forwarding. Imagine you’re on a private network which doesn’t allow connections to a specific server. Let’s say you’re at work and imgur.com is being blocked. To get around this we can create a tunnel through a server which isn’t on our network and thus can access Imgur. $ ssh -L 9000:imgur.com:80 user@example.com The key here is -L which says we’re doing local port forwarding. The awesome thing about SSH tunnels is that they are encrypted. Connecting to a database behind a firewall Another good example is if you need to access a port on your server which can only be accessed from localhost and not remotely. An example here is when you need to connect to a database console, which only allows local connection for security reasons.
. $ psql -h localhost -p 9000 GatewayPorts yes. HOWTO: SSH Tunneling Made Easy. By Frank Wiles I was surprised at how long it took me to find a good HOWTO on setting up a simple SSH tunnel that I wanted to write up this Quick-Tip.

Using OpenSSH on a Linux/Unix system you can tunnel all of the traffic from your local box to a remote box that you have an account on. For example I tunnel all of my outbound E-mail traffic back to my personal server to avoid having to change SMTP servers, use SMTP-AUTH, etc. when I am behind firewalls. I find that hotel firewalls, wireless access points, and the other various NATing devices you end up behind while traveling often do not play nice. To do this I use the following: ssh -f user@personal-server.com -L 2000:personal-server.com:25 -N The -f tells ssh to go into the background just before it executes the command. This essentially forwards the local port 2000 to port 25 on personal-server.com over, with nice benefit of being encrypted. Another useful feature of port forwarding is for getting around pesky firewall restrictions.
Proxy - The right way for dynamic ssh port-forwarding. SSH/OpenSSH/PortForwarding. Parent page: Internet and Networking >> SSH Port forwarding via SSH (SSH tunneling) creates a secure connection between a local computer and a remote machine through which services can be relayed.

Because the connection is encrypted, SSH tunneling is useful for transmitting information that uses an unencrypted protocol, such as IMAP, VNC, or IRC. SSH's port forwarding feature can smuggle various types of Internet traffic into or out of a network. This can be used to avoid network monitoring or sniffers, or bypass badly configured routers on the Internet. Note: You might also need to change the settings in other programs (like your web browser) in order to circumvent these filters. SSH Port Tunneling with Putty. SSH Port Tunneling with Putty.
Portforwarding with SSH (Putty) Overview Often you do not have direct access to a desired server, because a firewall blocks the port or you are on another network than the server.
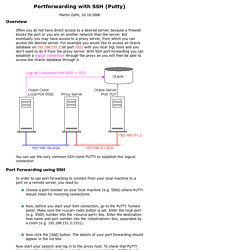
But eventually you may have access to a proxy server, from which you can access the desired server. For example you would like to access an Oracle database on 192.168.151.2 on port 1521 with you local SQL tools and you don't want to do it from the proxy server. With SSH port forwarding you can establish a logical connection through the proxy an you will then be able to access the Oracle database through it.
You can use the very common SSH client PUTTY to establish this logical connection Port Forwarding using SSH In order to use port forwarding to connect from your local machine to a port on a remote server, you need to: Choose a port number on your local machine (e.g. 5500) where PuTTY should listen for incoming connections. After clicking the Add Button. SSH (Linux)