

Ubuntu Linux Add Static IPv6 Address Network Configuration. ByVivek GiteonJune 19, 2009 How do I configure static IPv6 networking under Ubuntu Linux server operating systems?
You need to simply edit /etc/network/interfaces file and add the IPv6 networking configuration. Here is our sample setup: Ipv6 Address IP: 2607:f0d0:2001:000a:0000:0000:0000:0010/64Ipv6 Gateway IP: 2607:f0d0:2001:000a:0000:0000:0000:0001Interface name: eth0IPv6 Type: Static WARNING! Change Ubuntu Server from DHCP to a Static IP Address. If the Ubuntu Server installer has set your server to use DHCP, you will want to change it to a static IP address so that people can actually use it.

Changing this setting without a GUI will require some text editing, but that’s classic linux, right? Let’s open up the /etc/network/interfaces file. I’m going to use vi, but you can choose a different editor sudo vi /etc/network/interfaces For the primary interface, which is usually eth0, you will see these lines: Configuring NTP on Windows Server 2012. This article explains how to configure NTP on Windows Server 2012.

If you're looking for Windows Server 2008 R2, see my article here. Remember, that in a domain environment, time synchronization is taken care of but you should configure the PDC Emulator of a domain to sync externally since that is the server which decides what time it is! This is all you need if you want to keep it simple. Run using PowerShell as admin: w32tm /config /manualpeerlist:pool.ntp.org /syncfromflags:MANUAL Stop-Service w32time Start-Service w32time.
Selected ASDM VPN Configuration Procedures for the Cisco ASA 5500 Series, Version 5.2 - Configuring L2TP over IPSec [Cisco Adaptive Security Device Manager] Table Of Contents Configuring L2TP over IPSec L2TP Overview IPSec Transport and Tunnel Modes Configuring L2TP over IPSec Configuring L2TP over IPSec This chapter describes how to use ASDM to configure L2TP over IPSec on the security appliance, and includes the following topics: •L2TP Overview •Configuring L2TP over IPSec L2TP Overview The primary benefit of configuring L2TP with IPSec in a remote access scenario is that remote users can access a VPN over a public IP network without a gateway or a dedicated line, enabling remote access from virtually anyplace with POTS.
![Selected ASDM VPN Configuration Procedures for the Cisco ASA 5500 Series, Version 5.2 - Configuring L2TP over IPSec [Cisco Adaptive Security Device Manager]](http://cdn.pearltrees.com/s/pic/th/configuration-configuring-113292218)
An additional benefit is that the only client requirement for VPN access is the use of Windows 2000 with Microsoft Dial-Up Networking (DUN). No additional client software, such as Cisco VPN client software, is required. The configuration of L2TP with IPSec supports certificates using the pre-shared keys or RSA signature methods, and the use of dynamic (as opposed to static) crypto maps.
KB0000571 - Cisco ASA5500 - L2TP over IPSEC VPN. KB ID 0000571 Dtd 16/02/12 Problem When Cisco released version 7 of the operating system for PIX/ASA they dropped support for the firewall acting as a PPTP VPN device.
Note: If you want to use PPTP you can still terminate PPTP VPNs on a Windows server, if you enable PPTP and GRE Passthrough on the ASA. Set up web content filtering in 4 steps with Ubuntu. Journal Entry 8/9/2015. Journal Entry 8/8/2015. Journal 8/7/2015. 8/1/2015. Journal Entry 7/27/2015. Journal Entry 7/25/2015. Journal Entry 7/21/2015. Journal Entry 7/20/2015. Journal Entry 7/17/2015. Journal Entry 7/13/2015. Journal Entry 7/6/2015. Testing IPv6 Connectivity by Using the Ping Command (Windows CE 5.0) Send Feedback You can test IPv6 connectivity, and reachability for a specific destination, by using the ping command.
To test IPv6 connectivity by using the ping command To obtain the IPv6 address of a Windows CE-based device, run ipconfig /all at a command prompt. To ping another IPv6 node, use one of the commands shown in the following table. Opsview-core:agents - Opsview Documentation. Opsview supports the use of monitoring agents to gather data from remote devices.
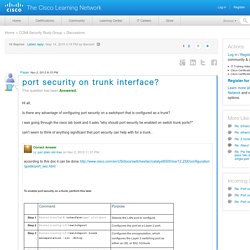
The most common types of monitoring agents used with Opsview are SNMP (Simple Network Management Protocol) and NRPE (Nagios Remote Plugin Executor). Generic Agents SNMP agents are provided with all managed network devices such as switches, routers and firewalls. SNMP polling is the standard method for gathering data, monitoring plugins exist for all commonly used devices. SNMP may also be used for server monitoring. Port security on trunk interface? 3560#show int trunk Port Mode Encapsulation Status Native vlan Fa0/1 on 802.1q trunking 20 Port Vlans allowed on trunk Fa0/1 1-4094.
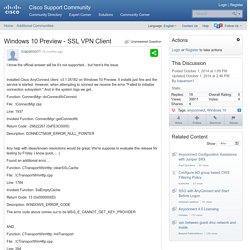
Opsview4.4:faq - Opsview Documentation. Installation and Initial Configuration I'm having trouble with the Opsview installation - can I get any help?
If you have issues installing, sign up to the forums and post a question in the relevant topic. Try to put in as much information as you can, especially: IT Monitoring for Networks, Applications, Virtual Servers and the Cloud. Windows 10 Preview - SSL VPN Client. I know the official answer will be it's not supported... but here's the issue.
Installed Cisco AnyConnect client v3.1.05182 on Windows 10 Preview. It installs just fine and the service is started. Activate ASDM as GUI Interface for Cisco ASA/PIX Firewall. Clientless SSL VPN (WebVPN) on ASA Configuration Example. Introduction Clientless SSL VPN (WebVPN) allows for limited but valuable secure access to the corporate network from any location. Users can achieve secure browser-based access to corporate resources at anytime. Journal Entry 6/29/2015. Journal Entry 6/20/2015. Microsoft Azure: Cloud Computing Platform & Services. AWS Products and Services - Global Compute, Storage, Database, Analytics, Mobile, Application, and Deployment Services. Amazon Web Services offers a broad set of global compute, storage, database, analytics, application, and deployment services that help organizations move faster, lower IT costs, and scale applications.
These services are trusted by the largest enterprises and the hottest start-ups to power a wide variety of workloads including: web and mobile applications, data processing and warehousing, storage, archive, and many others. Amazon Web Services provides a variety of cloud-based computing services including a wide selection of compute instances which can scale up and down automatically to meet the needs of your application, a managed load balancing service as well as fully managed desktops in the cloud.
Blade Servers, Blade Server Systems and Technology Solutions. Dell converged platforms — FX, VRTX and blade server products. PowerEdge FX Architecture: Redefining the Converged Data Center Dell's new FX architecture lets you configure complete, workload-specific blocks of servers, storage and networking so you can rapidly respond to your organizations needs. PowerEdge M630 Blade Server A 2-socket blade used in M1000e or VRTX converged infrastructures, equally well suited for office environments or large data centers, and ideal for private cloud.
PowerEdge FX Architecture: Redefining the Converged Data Center Dell's new FX architecture lets you configure complete, workload-specific blocks of servers, storage and networking so you can rapidly respond to your organizations needs. DansGuardian - True Web Content Filtering for All. Five content filters suitable for both home and business. Jack Wallen identifies five content access management and filtering apps. I am not one to advocate a Big Brother-esque environment for business as that does little for morale or instilling a two-way sense of trust. But there are companies out there that must lock down machines, for whatever reason, and need the tools to do so. Home use, of course, is a different story - where young children are susceptible to falling into the clutches of the wealth of mature content the web has to offer. When you need to block content, it's a relief to know there are plenty of tools out there that do the job.
I have identified five such tools that I believe can do the trick for anyone willing (or needing) to take the time to get these products set up and running properly. 7 killer open source monitoring tools.