

MDM web filtering. Sans titre. Note to publishers: If you intend to host our files on your server, please instead consider linking to this page. It will help us prevent spreading of obsolete versions, which we believe is critical when security software is concerned. Thank you. Supported versions of operating systems. Documentation Microsoft Identity Manager. Microsoft Identity Manager. Détails.

NAXSI, un module de filtrage HTTP pour nginx. Nbs-system/php-malware-finder: Detect potentially malicious PHP files. NAXSI : un pare-feu applicatif pour Nginx - NBS System. Une protection en temps réel contre les attaques.
PfSense Setup HQ - The ultimate resource for pfSense setup information, tips and techniques. Quadrant Information Security. Open Source IDS / IPS / NSM engine. We are thrilled to announce Suricata 4.0.

This is a major new release, improving detection capabilities, adding new output options and more protocols. Improved Detection Based on valuable feedback from the rule writing teams at Emerging Threats and Positive Technologies we’ve added and improved many rule keywords for inspecting HTTP, SSH and other protocols. TLS additions were contributed by Mats Klepsland at NorCERT, including decoding, logging and matching on TLS serial numbers. Additionally, Suricata now allows rule writers to specify who’s the target in a signature. TLS improved, NFS added. Snorby. Home · Snorby/snorby Wiki. Snort. Fichiers Support. Les prix VPN - tarifs VPN réduits. Pricing Tunnello VPN. Firewall pfSense® SG-2440 30Go - pfSense - Firewall. HTTPS : Let’s Encrypt annonce l’arrivée des certificats génériques. La sécurité du web passe par le développement des sites en HTTPS et les initiatives comme Let’s Encrypt ont permis d’avancer sensiblement dans cette voie.

Buttercup. Conférences. Hash & Validate - Online MD5, SHA1, SHA256 and CRC32 file hasher. Blog de Gentil Kiwi. The No More Ransom Project. Tools. FOCA. FOCA includes a server discovery module, whose purpose is to automate the servers search process using recursively interconnected routines.
The techniques used to this end are: Web SearchSearches for hosts and domain names through URLs associated to the main domain. Each link is analyzed to extract from it new host and domain names. DNS SearchEach domain is checked to ascertain which are the host names configured in NS, MX, and SPF servers to discover new host and domain names. IP resolutionEach host name is resolved by comparison to the DNS to obtain the IP address associated to this server name. PTR ScanningTo find more servers in the same segment of a determined address, IP FOCA executes a PTR logs scan. Bing IPFor each IP address discovered, a search process is launched for new domain names associated to that IP address. Common namesThis module is designed to carry out dictionary attacks against the DNS.
Virtual Private Network Service Provider. The App I Used to Break Into My Neighbor’s Home. When I broke into my neighbor’s home earlier this week, I didn’t use any cat burglar skills.
I don’t know how to pick locks. I’m not even sure how to use a crowbar. It turns out all anyone needs to invade a friend’s apartment is an off switch for their conscience and an iPhone. KeyMe: Copy Keys, Solve Lockouts. ABUS KeyGarage™ 767 (53507) Niara – Use Cases. Total Security Management. Security Incident and Event Management (SIEM)Traditionally SIEM is a highly complex technology where, while it can be easy to deploy, is also extremely difficult to decipher when an alert comes in.

Our SIEM module simplifies this by providing you with actionable data in clear simple terms, and at any time you can hit the Ask an Expert button for help from our Security Operations Center! We provide both "self-response" and "fully-managed" options for our technology, meaning you can choose to receive the alerts yourself (via email, SMS or phone call), or you can have us handle it, make sure it's a real threat, and contact you day and night as needed to mitigate a situation.
Parrot Security. Cloud Pentesting Parrot Cloud is a special edition of our OS specifically designed for servers, it consists on a lightweight parrot system without graphic interfaces, wireless and forensic tools and any other tools that can be considered useless in a remote-controlled virtual environment.
Concept The idea of Parrot Cloud is to have a VPS or a dedicated server with a special operating system full of useful security tools, neither relying all the dirty work to your local machine nor relying the security of your confidential data to a 3rd party provider. It can also be used to store private files (preferably encrypted), scan targets in the background and other stuff that you don't need to do with your own machines, allowing you to go everywhere you want with just a Parrot live USB and to do great penetration tests without having confidential data physically with you.
Parrot Security OS - Une autre distrib pour faire de la sécu. On connait tous Kali, la distrib orientée sécu mais en voici une autre baptisée Parrot Security OS qui permet aussi de faire du pentest, du forensic, du reverse engineering, de protéger son anonymat, de faire du chiffrement, de coder...etc.

Basée sur une Debian, Parrot Security OS, embarque des tas d'outils sympa dont vous pouvez retrouver la liste ici. Notez qu'il existe aussi une version Cloud, qui s'installe sur un serveur à vous et qui permet de profiter de tous les outils de Parrot Security OS à distance et en tous lieux. iPhone / iPad L2TP Client Setup - SoftEther VPN Project. This document describes how to connect to your SoftEther VPN Server by using the L2TP/IPsec VPN Client which is bundled with iOS.
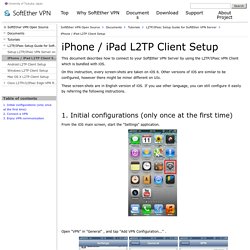
On this instruction, every screen-shots are taken on iOS 6. Other versions of iOS are similar to be configured, however there might be minor different on UIs. These screen-shots are in English version of iOS. If you use other language, you can still configure it easily by referring the following instructions. 1. From the iOS main screen, start the "Settings" application. Open "VPN" in "General" , and tap "Add VPN Configuration... " . A new L2TP VPN connection setting will be created, and the configuration screen will appear.
On this screen, you have to specify either hostname or IP address of the destination SoftEther VPN Server. 2. OpenVPN project. OpenVPN is entirely a community-supported OSS project which uses the GPL license.

The project has many developers and contributors from OpenVPN Technologies, Inc and from the broader OpenVPN community. In addition, there are numerous projects that extend or are otherwise related to OpenVPN. Your support can go a long way towards ensuring OpenVPN's continuing development, including staying on top of security issues, maintaining a rigorous testing program, adding new features, improving documentation, and providing technical support. Take a look at this Wiki article for ideas on how to contribute.
SoftEther VPN Open Source - SoftEther VPN Project. Sans titre. The following outlines the minimum hardware requirements for pfSense 2.x. Note the minimum requirements are not suitable for all environments. You may be able to get by with less than the minimum, but with less memory you may start swapping to disk, which will dramatically slow down your system. Network Card Selection Selection of network cards (NICs) is often the single most important performance factor in your setup. Inexpensive NICs can saturate your CPU with interrupt handling, causing missed packets and your CPU to be the bottleneck. NICs based on Intel chipsets tend to be the best performing and most reliable when used with pfSense software.
The Secret Surveillance Catalogue. Samy Kamkar: PoisonTap - exploiting locked computers over USB. Created by @SamyKamkar || When PoisonTap (Raspberry Pi Zero & Node.js) is plugged into a locked/password protected computer, it: emulates an Ethernet device over USB (or Thunderbolt)hijacks all Internet traffic from the machine (despite being a low priority/unknown network interface)siphons and stores HTTP cookies and sessions from the web browser for the Alexa top 1,000,000 websitesexposes the internal router to the attacker, making it accessible remotely via outbound WebSocket and DNS rebinding (thanks Matt Austin for rebinding idea!) Live demonstration and more details available in the video: Inverse Path - USB armory. The USB armory from Inverse Path is an open source hardware design, implementing a flash drive sized computer. The compact USB powered device provides a platform for developing and running a variety of applications.
Reporting: Export Kibana Visualizations. Logstash. An Introduction to the ELK Stack (Now the Elastic Stack) Most Recent Getting Started On Demand Videos: Looking for a hosted & managed solution? Check out the Elastic's 14-Day Free Cloud Trial. By combining the massively popular Elasticsearch, Logstash, and Kibana (what was the ELK Stack is now the Elastic Stack), Elastic has created an end-to-end stack that delivers actionable insights in real time from almost any type of structured and unstructured data source. Built and supported by the engineers behind each of these open source products, the Elastic Stack makes searching and analyzing data easier than ever before.
An Introduction to the ELK Stack (Now the Elastic Stack) Tutoriel. Graylog permet de stocker tout type de messages, qu’il s’agisse de logs serveurs, de journaux web ou de logs applicatifs. Rufus - Create bootable USB drives the easy way. Penetration Testing and Ethical Hacking Linux Distribution. Tools for a Safer PC. An important aspect of securing any system is the concept of “defense-in-depth,” or having multiple layers of security and not depending on any one approach or technology to block all attacks. Here are some links to tools and approaches that I have found useful in stopping malware from invading a PC. Your mileage may vary. Learn, Memorize, Practice the 3 Rules Follow Krebs’s 3 Basic Rules for online safety, and you will drastically reduce the chances of handing control over your computer to the bad guys. In short, 1) If you didn’t go looking for it, don’t install it; 2) If you installed, update it. 3) If you no longer need it, get rid of it!
How France's TV5 was almost destroyed by 'Russian hackers' Image copyright Getty Images A powerful cyber-attack came close to destroying a French TV network, its director-general has told the BBC. TV5Monde was taken off air in April 2015. A group calling itself the Cyber Caliphate, linked to so-called Islamic State, first claimed responsibility. But an investigation now suggests the attack was in fact carried out by a group of Russian hackers.
The attack used highly targeted malicious software to destroy the TV network's systems. Uniformatic. Boutique de Query Informatique - Clés USB sécurisées chiffrées. Classifier les actifs pour analyser les risques - Cases. Home - SECURITYMADEIN.LU. CIRCL » CIRCLean - USB key sanitizer. CIRCLean Malware regularly use USB sticks to infect victims and the abuse of USB sticks is a common vector of infection (as an example Lost USB keys have 66% chance of malware). CIRCLean is a independent hardware solution to clean documents from untrusted (obtained) USB keys / USB sticks. Charte de sécurité : 11 commandements - Cases. Se protéger - Cases. Felony - Pour se mettre au chiffrement avec PGP en toute simplicité. PGP c'est le pied quand il s'agit de chiffrement. Mais ce n'est pas forcement simple à prendre en main par tout le monde. Trials and Freeware Software. Page 4 sur 1711 « Upgrade your mind.
Chers amis, vous n’êtes pas sans savoir que Google concentre la plupart de nos recherches. Et parmi ces recherches, il y a nos inquiétudes les plus profondes. Notamment, lorsque nous sommes malades. Et en ce moment, le monde est malade, y compris la France. Comment fonctionne l’itinérance de profil utilisateur ? Cinq questions brulantes sur la redirection USB. Disable USB Flash Drives.
Cadenas usb lindy. Disable USB Flash Drives.