

Vulnérabilités. Virus. Tuto. Les meilleurs cours sur la sécurité informatique. Tutoriel.securite. IAM. Aperçu - Authentic 2 - Projets Entr'ouvert. A versatile identity management server. sponsored by Entr'ouvert <info+authentic@entrouvert.com> Features¶ Authentic 2 is heavily customisable.Authentic 2 is written using Python and the Django framework and some C when speed matters - cryptography.
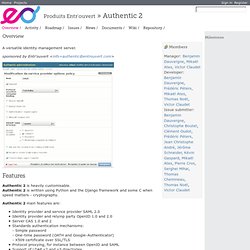
Authentic 2 main features are: Identity provider and service provider SAML 2.0 Identity provider and relyinp party OpenID 1.0 and 2.0 Server CAS 1.0 and 2 Standards authentication mechanisms:- Simple password- One-time password (OATH and Google-Authenticator)- X509 certificate over SSL/TLS Protocol proxying, for instance between OpenID and SAML Support of LDAP v2 and v3 directories Support of the PAM backend Identity attribute management.
Hacking. IT Security. The Surveillance Catalog - The Wall Street Journal. As the Internet has grown to handle more data, monitoring companies have had to keep up.

Interception now can mean taking all the traffic from the Internet backbone and funneling it through devices that inspect the packets of data, determine what is inside them, and make decisions about whether to copy them for law enforcement. Agence nationale de la sécurité des systèmes d’information. Sécurité de l'information.
CYBERWAR.