

Top 10 Web hacking techniques of 2010 revealed. Network World - A Web hack that can endanger online banking transactions is ranked the No. 1 new Web hacking technique for 2010 in a top 10 list selected by a panel of experts and open voting.

Called the Padding Oracle Crypto Attack, the hack takes advantage of how Microsoft's Web framework ASP.NET protects AES encryption cookies. FROM THE SECURITY WORLD: Quirky moments at Black Hat DC 2011 If encryption data in the cookie has been changed, the way ASP.NET handles it results in the application leaking some information about how to decrypt the traffic. With enough repeated changes and leaked information, the hacker can deduce which possible bytes can be eliminated from the encryption key.
That reduces the number of unknown bytes to a small enough number to be guessed. The developers of the hack -- Juliano Rizzo and Thai Duong -- have developed a tool for executing the hack. Here are the rest of the top 10 Web hacks voted in the competition: 2. How To Become A Hacker. Copyright © 2001 Eric S.
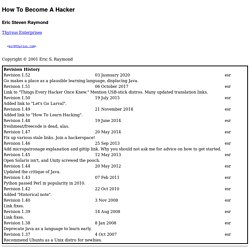
Raymond As editor of the Jargon File and author of a few other well-known documents of similar nature, I often get email requests from enthusiastic network newbies asking (in effect) "how can I learn to be a wizardly hacker? ". Back in 1996 I noticed that there didn't seem to be any other FAQs or web documents that addressed this vital question, so I started this one.
A lot of hackers now consider it definitive, and I suppose that means it is. Still, I don't claim to be the exclusive authority on this topic; if you don't like what you read here, write your own. If you are reading a snapshot of this document offline, the current version lives at Note: there is a list of Frequently Asked Questions at the end of this document.
Numerous translations of this document are available: ArabicBelorussianBulgarianChinese, Czech. The five-dots-in-nine-squares diagram that decorates this document is called a glider. If you want to be a hacker, keep reading. An Incredible Way to Reveal Passwords Behind Asterisks. How to Unlock a Computer Without a Password Reset Disk. Hack This Site! The Best Hacking Tutorial Sites - Learn Legal Hacking - StumbleUpon. How to use Google for Hacking. Google serves almost 80 percent of all search queries on the Internet, proving itself as the most popular search engine.

However Google makes it possible to reach not only the publicly available information resources, but also gives access to some of the most confidential information that should never have been revealed. In this post I will show how to use Google for exploiting security vulnerabilities within websites. The following are some of the hacks that can be accomplished using Google. 1. Hacking Security Cameras There exists many security cameras used for monitoring places like parking lots, college campus, road traffic etc. which can be hacked using Google so that you can view the images captured by those cameras in real time. Inurl:”viewerframe?
Click on any of the search results (Top 5 recommended) and you will gain access to the live camera which has full controls. you now have access to the Live cameras which work in real-time. Intitle:”Live View / – AXIS” 2. 3. . “? 4.