

Tor: Linux/BSD/Unix Install Instructions. Note that these are the installation instructions for running a Tor client.

The easiest way to do this is to simply download the Tor Browser Bundle and you are done. Step One: Download and Install Tor The latest release of Tor can be found on the download page. We have packages for Debian, Red Hat, Gentoo, *BSD, etc there too. If you're using Ubuntu, don't use the default packages: use our deb repository instead. If you're building from source, first install libevent, and make sure you have openssl and zlib (including the -devel packages if applicable).
Tor comes configured as a client by default. Step Two: Configure your applications to use Tor If you want to use Tor for anonymous web browsing, please use the Tor Browser Bundle. For information on how to Torify other applications, check out the Torify HOWTO. If it's still not working, look at this FAQ entry for hints. Step Three: Configure it as a relay The Tor network relies on volunteers to donate bandwidth. Batch Resize Images with Gimp » Ulyssesonline. Most digital cameras nowadays, have resolutions that are far bigger than the normal monitor screen size.
On average most point-and-shoot digital cameras have resolution anywhere from 3 megapixels to 10 megapixels. Most monitors these days have resolution of either 1024×768 or the slightly larger 1280×1024 pixels. If you ever need to upload pictures online to a gallery or to a webpage, you will need to resize your images to fit the screen as well as reduce the image size. If you use Gimp, an image manipulation program, you can use David’s Batch Processor, a Gimp plugin to manage the resizing of multiple images in a single command. To download the Batch Processor, open your Synaptic Package Manager located under System > Administration.
Start Gimp. You can select a single file or multiple images for our purposes here in this article. SQL Injection Walkthrough. 1.0 Introduction When a machine has only port 80 opened, your most trusted vulnerability scanner cannot return anything useful, and you know that the admin always patch his server, we have to turn to web hacking.
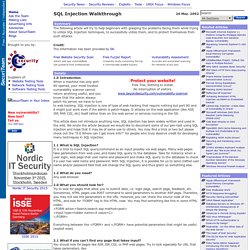
SQL injection is one of type of web hacking that require nothing but port 80 and it might just work even if the admin is patch-happy. It attacks on the web application (like ASP, JSP, PHP, CGI, etc) itself rather than on the web server or services running in the OS. This article does not introduce anything new, SQL injection has been widely written and used in the wild. We wrote the article because we would like to document some of our pen-test using SQL injection and hope that it may be of some use to others. You may find a trick or two but please check out the "9.0 Where can I get more info? " 1.1 What is SQL Injection? 1.2 What do you need? 2.0 What you should look for?
Everything between the <FORM> and </FORM> have potential parameters that might be useful (exploit wise). Tech talks. Tutorials. Beginner GIMP Quickies Use GIMP for simple graphics needs without having to learn advanced image manipulation methods.
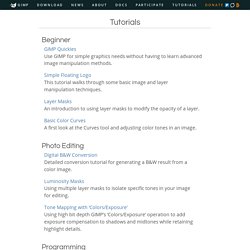
Simple Floating Logo This tutorial walks through some basic image and layer manipulation techniques. Layer Masks An introduction to using layer masks to modify the opacity of a layer. Basic Color Curves A first look at the Curves tool and adjusting color tones in an image. Photo Editing Digital B&W Conversion Detailed conversion tutorial for generating a B&W result from a color image. Luminosity Masks Using multiple layer masks to isolate specific tones in your image for editing. Tone Mapping with ‘Colors/Exposure’ Using high bit depth GIMP’s ‘Colors/Exposure’ operation to add exposure compensation to shadows and midtones while retaining highlight details.
Programming Basic GIMP Perl Learn how to write simple perl scripts using the gimp-perl module (GNU/Linux users only). Automate Editing Using GIMP Python to automate a workflow. All (Legacy) Tutorials List. Linux from Scratch Free eBook.