

Understanding OAuth2 « BubbleCode by Johann Reinke. If OAuth2 is still a vague concept for you or you simply want to be sure you understand its behaviours, this article should interest you.

What is OAuth2? OAuth2 is, you guessed it, the version 2 of the OAuth protocol (also called framework). This protocol allows third-party applications to grant limited access to an HTTP service, either on behalf of a resource owner or by allowing the third-party application to obtain access on its own behalf. Access is requested by a client, it can be a website or a mobile application for example. Version 2 is expected to simplify the previous version of the protocol and to facilitate interoperability between different applications. Specifications are still being drafted and the protocol is constantly evolving but that does not prevent it from being implemented and acclaimed by several internet giants such as Google or Facebook. Basic knowledge Roles. Jazzband/django-oauth-toolkit: OAuth2 goodies for the Djangonauts!
Defining Scopes - OAuth 2.0 Servers. A good place to start with defining scopes is to define read vs write separately.
This works well for Twitter, since not all apps actually want to be able to post content to your Twitter account, some just need to access your profile information. What is the OAuth 2.0 Implicit Grant Type? The Implicit Grant Type is a way for a single-page JavaScript app to get an access token without an intermediate code exchange step.
It was originally created for use by JavaScript apps (which don’t have a way to safely store secrets) but is only recommended in specific situations. AppAuth. OSSystems/python-hydra-sdk: Hydra SDK for Python. Guide to an OAuth2 API with Django - Halfspring - Medium. In this guide I will show you how to configure your next project to use the cutting-edge OAuth2 standard.
I will assume no prior knowledge to Django. Django Written in Python, Django is opinionated web framework with a lot of third party packages. A couple of sites using Django: DisqusPinterestGiphy. API Access Rules · ORY Documentation. ORY Oathkeeper reaches decisions to allow or deny access by applying Access Rules.
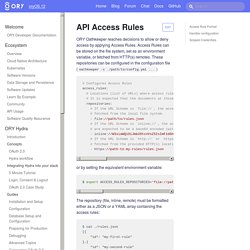
Access Rules can be stored on the file system, set as an environment variable, or fetched from HTTP(s) remotes. These repositories can be configured in the configuration file (oathkeeper -c . /path/to/config.yml ...) or by setting the equivalent environment variable: $ export ACCESS_RULES_REPOSITORIES=' The repository (file, inline, remote) must be formatted either as a JSON or a YAML array containing the access rules: OAuth 2 Simplified. This post describes OAuth 2.0 in a simplified format to help developers and service providers implement the protocol.
The OAuth 2 spec can be a bit confusing to read, so I've written this post to help describe the terminology in a simplified format. The core spec leaves many decisions up to the implementer, often based on security tradeoffs of the implementation. Instead of describing all possible decisions that need to be made to successfully implement OAuth 2, this post makes decisions that are appropriate for most implementations.
Note: This post has been updated from the original 2012 version based on the current best practices of OAuth 2.0. REST API · ORY Documentation. A cloud native access control server providing best-practice patterns (RBAC, ABAC, ACL, AWS IAM Policies, Kubernetes Roles, ...) via REST APIs.
You are viewing REST API documentation. This documentation is auto-generated from a swagger specification which itself is generated from annotations in the source code of the project. It is possible that this documentation includes bugs and that code samples are incomplete or wrong.If you find issues in the respective documentation, please do not edit the Markdown files directly (as they are generated) but raise an issue on the project's GitHub presence instead. This documentation will improve over time with your help! If you have ideas how to improve this part of the documentation, feel free to share them in a GitHub issue any time. engines Check if a request is allowed POST /engines/acp/ory/{flavor}/allowed HTTP/1.1 Content-Type: application/json Accept: application/json Request body Parameters Responses Overview Response Schema Status Code 500 Examples.
How to register an OAuth 2.0 client / OpenID Connect relying party. A client must be signed up with the Connect2id server before it can request OpenID Connect or OAuth 2.0 tokens from it.

First and foremost this establishes the credentials for identifying and authenticating the client in the requests that will follow. Second, this sets up various global client settings, such as the preferred crypto algorithm for the ID tokens that will be issued to the client. Without these settings there won't be enough context to complete many of the client requests, as the OAuth requests are designed to be fairly minimal and carry few parameters. Upon sign up, the registrant, which can be the developer, an administrator, or the client software itself (yes, automated self-registration is possible) needs to provide several pieces of information: The methods, or grant types in OAuth jargon, that the client will use to obtain the end-user's authorisation and tokens. Note that the server's security policy dictates what parameters may ultimately get registered. With curl: The problem with OAuth for Authentication. I want to thank Nat Sakimura for doing a version of this post in Japanese.
In some of the feedback I have gotten on the openID Connect spec, the statement is made that Connect is too complicated. Basic Authentication Header Generator. Understanding scopes for OAuth Apps. Scopes let you specify exactly what type of access you need.
Scopes limit access for OAuth tokens. They do not grant any additional permission beyond that which the user already has. OAuth 2.0 Scopes for Google APIs