

Gobetween - modern & minimalistic load balancer for the cloud era. Pushkin. Jfokus.
Web Crawling. Node.js. 20 Command Line Tools to Monitor Linux Performance. It’s really very tough job for every System or Network administrator to monitor and debug Linux System Performance problems every day. After being a Linux Administrator for 5 years in IT industry, I came to know that how hard is to monitor and keep systems up and running.
For this reason, we’ve compiled the list of Top 20 frequently used command line monitoring tools that might be useful for every Linux/Unix System Administrator. These commands are available under all flavors of Linux and can be useful to monitor and find the actual causes of performance problem. Untitled. Obey the State!

When you hear the term State Machine, you may think of totalitarian societies as depicted in George Orwell’s 1984 run by ruthless dictators. However, in programming, state machines are quite benign and helpful in solving certain kinds of programming problems. Chapter 10 of Learning PHP Design Patterns, explains the State design pattern in full detail. In this post I want to introduce the concept of a state machine, but we will not see a true State design pattern just yet. Here, we’ll just look at a state machine and how it can be used in OOP programming in general. Generally speaking in programming, a state is the current value of a variable. A State Class To get started, begin with an interface that encompasses all of the different states (moves) in R-P-S-L-S. Note that all of the methods are public. Good Programmers Wanted. Three Things I Expect From a Software Architect - Yegor Bugayenko. A software architect is a key person in a software project, which I explained in my What Does a Software Architect Do?
Post a few months ago. The architect is personally responsible for the technical quality of the product we're developing. No matter how good the team is, how complex the technology is, how messy the requirements are, or how chaotic the project sponsor is, we blame the architect and noone else. Of course, we also reward the architect if we succeed. Here is what I, as project manager, expect from a good architect. In all projects we run at Teamed.io, I expect regular reports from software architects a few times a week. Scope Status The first and most important type of information I'm looking for is the scope status, which should be presented in Product Breakdown Structure (PBS) format.
LearnProgramming on Github. Category:Programming Tasks. Programming tasks are problems that may be solved through programming.
When such a task is defined, Rosetta Code users are encouraged to solve them using as many different languages as they know. The end goal is to demonstrate how the same task is accomplished in different languages. These are the Programming Tasks that have been defined and solved. Feel free to add solutions in languages not already included. The Category:Simple is a small subset with only "really simple" tasks, like "Hello World", and demonstrations of basic language-features. The Category:Draft Programming Tasks is a list of tasks, some of which are just awaiting more implementations before they can be promoted to tasks. Read the guidelines on creating new tasks. The following 871 pages are in this category, out of 871 total. Web Data Platform & Free Web Scraping Tool.
Roberto Cortez Java Blog. In one way or another, every developer has come in touch with an API.
Either integrating a major system for a big corporation, producing some fancy charts with the latest graph library, or simply by interacting with his favorite programming language. The truth is that APIs are everywhere! Alfresco. The Twelve-Factor App. IMPORTANT to read/listen. 10 Questions To Make Programming Interviews Less Expensive. Conducting Interview is not cheap and costs both time and money to a company.

It take a lot of time to find the right candidate for a job from 100s resume you receive from consultants and agents. They will always tell you that this guy is a Java Guru, this one is SQL Expert and next one is the full stack developer you are looking for. If you have trust them blindly and invite all of them for face-to-face interview, you are going to be disappointed. One of the first thing you should do is to filter candidates who claims to have certain skills e.g.
SQL but doesn't have them, the faster you can weed out those candidates the cheaper will be the hiring process.
Facebook-dev. IT razno. Social engines. Document Managament Systems (DMS) Messaging. SSO Security Auth. Google. CSS. XML. eLearning. DB. Posao. RFID. Productivity. MREZE. Norse - IPViking Live. Every second, Norse collects and analyzes live threat intelligence from darknets in hundreds of locations in over 40 countries.
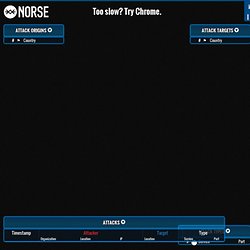
The attacks shown are based on a small subset of live flows against the Norse honeypot infrastructure, representing actual worldwide cyber attacks by bad actors. At a glance, one can see which countries are aggressors or targets at the moment, using which type of attacks (services-ports). Hovering over the Attack Origins, Attack Targets, or Attack Types will highlight just the attacks emanating from that country or over that service-port respectively. Vert.x. Mutli Platform apps. HTML5 provides developers the potential to develop rich internet applications.

HTML5 turns any website into a Web App. HTML5 web apps are not only limited to desktop but are also accessible on modern mobile and tablets as well. On mobile, we have a great tool called PhoneGap.
GIT. FOR READ. Articles. SOA ESB Architecture. Security. Development. Windows. Php. Linux. Actionscript. E-commerce. Web HTML. Scala. Java. Javascript.