

Physical security. Overview[edit] Canadian Embassy in Washington, D.C. showing planters being used as vehicle barriers to increase the standoff distance, and barriers and gates along the vehicle entrance Physical security systems for protected facilities are generally intended to:[2][3][4] deter potential intruders (e.g. warning signs and perimeter markings); detect intrusions and monitor/record intruders (e.g. intruder alarms and CCTV systems); andtrigger appropriate incident responses (e.g. by security guards and police).
Security guard. A security officer (or security guard) is a person who is paid to protect property, assets, or people.

They are usually privately and formally employed civilian personnel. Security officers are generally uniformed and act to protect property by maintaining a high visibility presence to deter illegal and inappropriate actions, observing (either directly, through patrols, or by watching alarm systems or video cameras) for signs of crime, fire or disorder; then taking action and reporting any incidents to their client and emergency services as appropriate.
Functions and duties[edit] An American security guard at a North Carolina apartment complex in April 2010. Many security firms and proprietary security departments practice the "detect, deter, observe and report" methodology. The Most Critical Element. Surveillance. Surveillance (/sərˈveɪ.əns/ or /sərˈveɪləns/)[1] is the monitoring of the behavior, activities, or other changing information, usually of people for the purpose of influencing, managing, directing, or protecting them.[2] This can include observation from a distance by means of electronic equipment (such as CCTV cameras), or interception of electronically transmitted information (such as Internet traffic or phone calls); and it can include simple, relatively no- or low-technology methods such as human intelligence agents and postal interception.
The word surveillance comes from a French phrase for "watching over" ("sur" means "from above" and "veiller" means "to watch"), and is in contrast to more recent developments such as sousveillance.[3][4][5] Surveillance is very useful to governments and law enforcement to maintain social control, recognize and monitor threats, and prevent/investigate criminal activity.
Types[edit] Computer[edit] Security alarm. A LYNX wireless home alarm system control panel, made by Honeywell A security alarm[1] is a system designed to detect intrusion – unauthorized entry – into a building or area.

Security alarms are used in residential, commercial, industrial, and military properties for protection against burglary (theft) or property damage, as well as personal protection against intruders. Car alarms likewise protect vehicles and their contents. Prisons also use security systems for control of inmates. Some alarm systems serve a single purpose of burglary protection; combination systems provide both fire and intrusion protection. Glass break detector. Passive glass break detector A glass break detector is a sensor used in electronic burglar alarms that detects if a pane of glass is shattered or broken.
These sensors are commonly used near glass doors or glass store-front windows to detect if an intruder broke the glass and entered. Motion detector. Wall. Etymology[edit] Wall comes from Latin vallum meaning "...an earthen wall or rampart set with palisades, a row or line of stakes, a wall, a rampart, fortification...

" while the Latin word murus meant a defensive stone wall[1] It is notable that English uses the same word to refer to an external wall, and the internal sides of a room. This is by no means universal, and many languages distinguish between the two. A German City Has Deployed Special Paint That Deflects Drunks’ Pee Back Onto Their Shoes. IG St.

Pauli on YouTube If you happen to live in a well-trafficked area, particularly one close to drinking establishments, you’re going to have to deal with some funky aromas. One public urinator here and there isn’t a big deal, but if enough dudes start doing it, the streets start to smell like the trough at the ball park. Well, the residents of one particularly unine-soaked area of Hamburg, Germany have come up with a solution. They’ve coated their walls and other things that guys may want to mark with hydrophobic paint. Anti-graffiti coating. An anti-graffiti coating is a coating that prevents graffiti paint from bonding to surfaces.

Annual expenses of graffiti worldwide[edit] Types of paint[edit] There are two common types of paint used today. The first are water-based paints such as latex and acrylic paint, and the second are oil-based paints. Anti-climb paint. Anti-climb paint on a brick wall in the UK Anti-climb paint (also known as non-drying paint, anti-intruder paint, anti-vandal grease) is a class of paint consisting of a thick oily coating that is applied with a stiff brush, trowel or by hand using a protective glove.

In appearance it is similar to smooth gloss paint when applied but it remains slippery indefinitely thereby preventing any intruder from gaining a foothold. Advantage[edit] It is used to prevent climbing on objects such as lamp posts, walls and fences. It owes its effectiveness to the fact that it is based on a non-drying oil and keeps the surface greasy and slippery. High Security Fencing Systems. TRISPIKE is a unique anti-climb device.
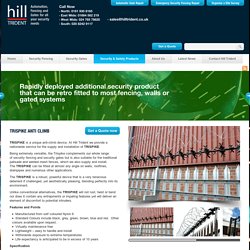
At Hill Trident we provide a nationwide service for the supply and installation of TRISPIKE. Being extremely versatile, the Trispike complements our whole range of security fencing and security gates but is also suitable for the traditional palisade and welded mesh fences, which we also supply and install. The TRISPIKE can be fitted at almost any angle on walls, rooflines, drainpipes and numerous other applications.
Perimeter protection, sensor network, fences. Fenced-in areas, such as airports, nuclear power stations, industrial sites, or private plots of land, can now be monitored thanks to novel sensor technology that has been developed by a team of experimental physicists. The sensors respond immediately as soon as someone tries to climb over or cut through the fence, providing information on the precise location of the security breach. Fenced-in areas, such as airports, nuclear power stations, industrial sites, or private plots of land, can now be monitored thanks to novel sensor technology that has been developed by a team of experimental physicists, led by Professor Uwe Hartmann at Saarland University.
The sensors respond immediately as soon as someone tries to climb over or cut through the fence, providing information on the precise location of the security breach. The sensors are even able to detect a low-flying drone passing overhead. “The cable can be attached to the fence, built into it or even buried beneath it. Mantrap (access control) A mantrap, air lock, sally port or access control vestibule is a physical security access control system comprising a small space with two sets of interlocking doors, such that the first set of doors must close before the second set opens.[1] In a manual mantrap, a guard locks and unlocks each door in sequence.
An intercom and/or video camera are often used to allow the guard to control the trap from a remote location. Piggybacking (security) In security, piggybacking refers to when a person tags along with another person who is authorized to gain entry into a restricted area, or pass a certain checkpoint.[1] The act may be legal or illegal, authorized or unauthorized, depending on the circumstances. However, the term more often has the connotation of being an illegal or unauthorized act.
To describe the act of an unauthorized person who follows someone to a restricted area without the consent of the authorized person, the term tailgating is also used. "Tailgating" implies without consent (similar to a car tailgating another vehicle on the freeway), while "piggybacking" usually implies consent of the authorized person. Piggybacking came to the public's attention particularly in 1999, when a series of weaknesses were exposed in airport security.
Piggybackers have various methods of breaching security. Permanently Disable a Household Lock with Lock-Kill. What do I do about someone squirting glue into the locks of my house? - burglary security. Hello all. Over the last 3 weeks, someone has been squirting glue into the keyholes of my house. I live alone in a house with 2 locks on the front door and one lock on the back door. One morning three weeks ago, my top front door lock had suddenly become gummy and difficult to use.
I thought it was suspicious but put it down to kids' pranks. My top front door lock became increasingly difficult to use, and last week I stopped using it altogether (so I only locked my bottom front door lock as I left for work every day). DoS. Safety and security window film. Safety and security window films are polyester, or PET films that are applied to glass and glazing in order to hold them together if the glass is shattered (similar to laminated glass).
Polycarbonate. Polycarbonates (PC) are a group of thermoplastic polymers containing carbonate groups in their chemical structures. Floor. Ceiling. Ceilings have frequently been decorated with fresco painting, mosaic tiles and other surface treatments. While hard to execute (at least in place) a decorated ceiling has the advantage that it is largely protected from damage by fingers and dust. In the past, however, this was more than compensated for by the damage from smoke from candles or a fireplace. Many historic buildings have celebrated ceilings. Perhaps the most famous is the Sistine Chapel ceiling by Michelangelo. Ceiling height may have psychological impacts.[3] demonstrative reconstruction of a Roman suspended ceiling in an Imperial palace of c. Fire-resistance rated ceilings[edit] The most common ceiling that contributes to fire-resistance ratings in commercial and residential construction is the dropped ceiling.
Kensington Security Slot. Padlock. History[edit] Safe. A typical home safe, which is portable. These types of safes are generally used for protection against fire. Bank vault. Time-delay combination locks. Fire protection. Public sign warning of the highest level of fire hazard at a campsite in Germany. Base isolation. How Faraday Cages Work.