

A run around the new ASP.NET Data Protection & Authorization Stacks - Barry Dorrans. What’s new in Security in ASP.NET 5 and MVC 6 - Dominick Baier. Announcing IdentityServer for ASP.NET 5 and .NET Core. Over the last couple of years, we’ve been working with the ASP.NET team on the authentication and authorization story for Web API, Katana and ASP.NET 5.
This included the design around claims-based identity, authorization and token-based authentication. In the Katana timeframe we also reviewed the OAuth 2.0 authorization server middleware (and the templates around it) and weren’t very happy with it. But as usual, there were deadlines and Web API needed a token-based security story, so it shipped the way it was. One year ago the ASP.NET team decided to discontinue that middleware and rather focus on consuming tokens instead. They also asked us if IdentityServer can be the replacement going forward.
By that time there were many unknowns – ASP.NET was still in early betas and literally changing every day. With RC1 (and soon RC2), we decided that now would the right moment in time to start porting IdentityServer – and here it is: IdentityServer4 (github / nuget / samples) Cryptographic Improvements in ASP.NET 4.5, pt. 2. Thanks for joining us for day two of our series on cryptography in ASP.NET 4.5!

In yesterday’s post, I discussed how ASP.NET uses cryptography in general, where key material is pulled from and how it is stored, and various problems that the APIs have introduced over the years. In today’s post, I’ll discuss how we’re mitigating those issues using 4.5’s opt-in model. The series outline is copied below for quick reference. Throughout the series I’ll refer to a sample solution. This Visual Studio 2012 solution contains projects that demonstrate many of the core concepts mentioned here. Cryptographic Improvements in ASP.NET 4.5, pt. 1. I am Levi Broderick, a developer on the ASP.NET team at Microsoft.

In this series, I want to introduce some of the improvements we have made to the cryptographic core in ASP.NET 4.5. Most of these improvements were introduced during beta and spent several months baking. When you create a new project using the 4.5 templates baked into Visual Studio 2012, those projects will take advantage of these improvements automatically. The intent of this series is both to explain why the ASP.NET team made these investments and to educate developers as to how they can take maximum advantage of this system.
This series will be divided into three posts: Throughout the series I’ll refer to a sample solution. Background Ever since ASP.NET’s inception over a decade ago, the product has consumed cryptography in some form. We quickly released a patch for that issue, but at the same time we realized that we needed to perform a more thorough investigation of cryptographic uses inside ASP.NET.
Fortinet Threat Map. Norse Attack Map. Your intelligent guide to the seedier side. DeepDotWeb - Surfacing The News From The Deep Web. CryptoLocker Ransomware Information Guide and FAQ. Info: The original CryptoLocker infection was disabled on June 2nd, 2014 when Operation Gameover took down its distribution network.

Since then there have been numerous ransomware infections that have been released that utilize the CryptoLocker name. It should be noted that these infections are not the same infection that is discussed below. If you have recently been infected with something that is calling itself CryptoLocker, you are most likely infected with the TorrentLocker infection. For more information on TorrentLocker, please visit our TorrentLocker support topic. Once at the topic, and if you are a member, you can subscribe to it in order to get notifications when someone adds more information to the topic. Table of Contents The purpose of this guide There is a lot of incorrect and dangerous information floating around about CryptoLocker. In many ways this guide feels like a support topic on how to pay the ransom, which sickens me. What is CryptoLocker. Watch surveillance online IP cameras in Canada. CA, - 1 ch.
CA, - 4 ch. CA, - 3 ch. Superfish Checker. 10,000 Top Passwords. Back when I wrote Perfect Passwords, I generated a list of the top 500 worst (aka most common) passwords which seems to have propagated quite a bit across the internet, including being mentioned on Gizomodo, Boing Boing, Symantec, Laughing Squid and many other sites.
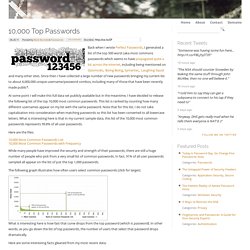
Since then I have collected a large number of new passwords bringing my current list to about 6,000,000 unique username/password combos, including many of those that have been recently made public*. At some point I will make this full data set publicly available but in the meantime, I have decided to release the following list of the top 10,000 most common passwords. This list is ranked by counting how many different usernames appear on my list with the same password. Note that for this list, I do not take capitalization into consideration when matching passwords so this list has been converted to all lowercase letters. Here are the files: 10,000 Most Common Passwords List10,000 Most Common Passwords with Frequency.