

Bibliography of Quantum Cryptography. By Gilles Brassard Département IRO, Université de Montréal.
C.P. 6128, Succursale "Centre-Ville" Montréal (Québec) Canada H3C 3J7 The original PostScript file from Gilles Brassard - provided by Edith Stoeveken - was converted to ASCII and reformatted in HTML; Sept 2 1994, Stephan Kaufmann. HTTP pointers to DVI files added by Claude Crépeau, March 6 1995. Abstract This paper provides an extensive annotated bibliography of papers that have been written on quantum cryptography and related topics. 1. For ages, mathematicians have searched for a system that would allow two people to exchange messages in perfect privacy.
In addition to key distribution, quantum techniques may also assist in the achievement of subtler cryptographic goals, important in the post-cold war world, such as protecting private information while it is being used to reach public decisions. 2. Quantum cryptography is best known for key distribution. How Quantum Cryptology Works" The idea that a vote cast by a person remains the same after he submitted it is taken very seriously in any democracy.
Voting is the right of the citizen, and it's how we choose the people who make important decisions on our behalf. When the security of the ballot is compromised, so, too, is the individual's right to choose his leaders. There are plentiful examples of vote tampering throughout history in the United States and in other countries. Votes get lost, the dead manage to show up on the poll results, and sometimes votes are even changed when they're tallied.
But, hopefully, the days when paper ballots get lost on the back roads of Florida en route to be counted will soon be gone, and the hanging chad will become an obscure joke on sitcom reruns from the early 21st century. Traditional Cryptology" Privacy is paramount when communicating sensitive information, and humans have invented some unusual ways to encode their conversations.
In World War II, for example, the Nazis created a bulky machine called the Enigma that resembles a typewriter on steroids. This machine created one of the most difficult ciphers (encoded messages) of the pre-computer age. Traditional Cryptology Problems" Both the secret-key and public-key methods of cryptology have unique flaws.
Oddly enough, quantum physics can be used to either solve or expand these flaws. The problem with public-key cryptology is that it's based on the staggering size of the numbers created by the combination of the key and the algorithm used to encode the message. These numbers can reach unbelievable proportions. What's more, they can be made so that in order to understand each bit of output data, you have to also understand every other bit as well. This means that to crack a 128-bit key, the possible numbers used can reach upward to the 1038 power [source: Dartmouth College]. The keys used in modern cryptography are so large, in fact, that a billion computers working in conjunction with each processing a billion calculations per second would still take a trillion years to definitively crack a key [source: Dartmouth College].
But SKC has its problems as well. Quantum physics has provided a way around this problem. Photon Properties" Photons are some pretty amazing particles.

They have no mass, they're the smallest measure of light, and they can exist in all of their possible states at once, called the wave function. Using Quantum Cryptology" Quantum cryptography uses photons to transmit a key.
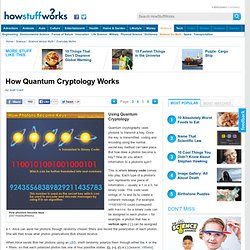
Once the key is transmitted, coding and encoding using the normal secret-key method can take place. But how does a photon become a key? How do you attach information to a photon's spin? This is where binary code comes into play. Each type of a photon's spin represents one piece of information -- usually a 1 or a 0, for binary code. When Alice sends Bob her photons using an LED, she'll randomly polarize them through either the X or the + filters, so that each polarized photon has one of four possible states: (|), (--), (/) or ( ) [source: Vittorio]. Introducing Eve" The goal of quantum cryptology is to thwart attempts by a third party to eavesdrop on the encrypted message.
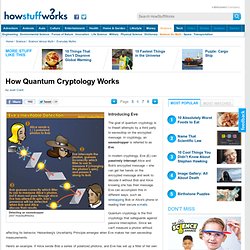
In cryptology, an eavesdropper is referred to as Eve. In modern cryptology, Eve (E) can passively intercept Alice and Bob's encrypted message -- she can get her hands on the encrypted message and work to decode it without Bob and Alice knowing she has their message. Eve can accomplish this in different ways, such as wiretapping Bob or Alice's phone or reading their secure e-mails. Quantum Cryptology Problems" Despite all of the security it offers, quantum cryptology also has a few fundamental flaws.
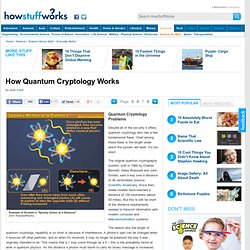
Chief among these flaws is the length under which the system will work: It’s too short. The original quantum cryptography system, built in 1989 by Charles Bennett, Gilles Brassard and John Smolin, sent a key over a distance of 36 centimeters [source: Scientific American]. Since then, newer models have reached a distance of 150 kilometers (about 93 miles). But this is still far short of the distance requirements needed to transmit information with modern computer and telecommunication systems.
The reason why the length of quantum cryptology capability is so short is because of interference. One group of Austrian researchers may have solved this problem. The Austrian team put a photon from an entangled pair at each end of a fiber optic cable. Even though it’s existed just a few years so far, quantum cryptography may have already been cracked. Quantum Cryptography: Lots More Information"