


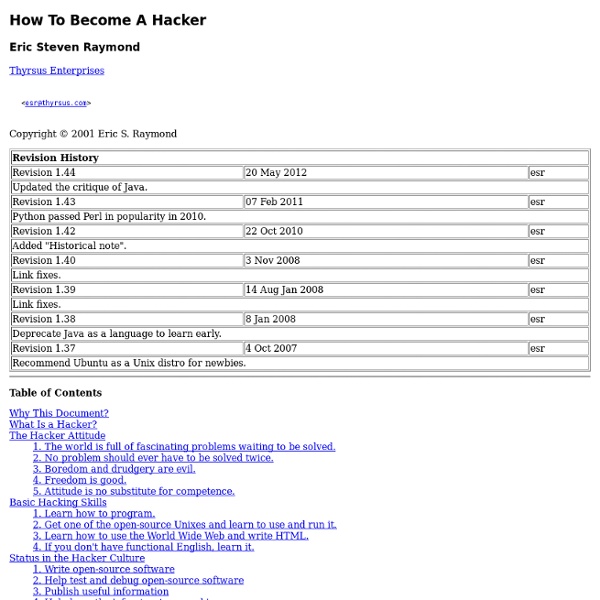
What is a Hacker Copyright © 2001 Eric S. Raymond As editor of the Jargon File and author of a few other well-known documents of similar nature, I often get email requests from enthusiastic network newbies asking (in effect) "how can I learn to be a wizardly hacker?". Back in 1996 I noticed that there didn't seem to be any other FAQs or web documents that addressed this vital question, so I started this one. A lot of hackers now consider it definitive, and I suppose that means it is. If you are reading a snapshot of this document offline, the current version lives at Note: there is a list of Frequently Asked Questions at the end of this document. Numerous translations of this document are available: ArabicBelorussianChinese (Simplified), Czech, Danish, Dutch, Estonian, German, GreekItalianHebrew, Norwegian, PersianPortuguese (Brazilian), RomanianSpanish, Turkish, and Swedish. If you find this document valuable, please leave me a tip on Gittip. 1. 2. 3. 5. 2.
The GNU Manifesto The GNU Manifesto (which appears below) was written by Richard Stallman in 1985 to ask for support in developing the GNU operating system. Part of the text was taken from the original announcement of 1983. Through 1987, it was updated in minor ways to account for developments; since then, it seems best to leave it unchanged. Since that time, we have learned about certain common misunderstandings that different wording could help avoid. If you want to install the GNU/Linux system, we recommend you use one of the 100% free software GNU/Linux distributions. The GNU Project is part of the Free Software Movement, a campaign for freedom for users of software. What's GNU? GNU, which stands for Gnu's Not Unix, is the name for the complete Unix-compatible software system which I am writing so that I can give it away free to everyone who can use it.(1) Several other volunteers are helping me. GNU will be able to run Unix programs, but will not be identical to Unix. Why I Must Write GNU
How to Hack Featured Article Categories: Featured Articles | Hacks In other languages: Español: hackear, Português: Hackear, Italiano: Hackerare, Français: hacker un système informatique, Русский: стать хакером, Deutsch: Einen Computer "hacken", 中文: 成为黑客, Bahasa Indonesia: Meretas, Čeština: Jak hackovat, Nederlands: Leren hacken
Hackers, pirates, cyberpunks : la résistance du web, Vu sur le w L'avènement des nouvelles technologies dans les années 1970, la démocratisation du micro-ordinateur, l'accès à une information toujours plus large, ont permis l'émergence d'une autre culture de masse. Cet essor a engendré l'accès à de nouveaux savoirs, à une pluralité d'informations. Cependant la quasi-totalité de la toile étant gérée par quelques multinationales surpuissantes, il existe une frange qui se détache de cette information, la considérant comme tronquée. Qu'est ce qu'un hacker? Hacker : nom masculin (de l'anglais to hack into, entrer par effraction) Personne qui, par jeu, goût du défi ou souci de notoriété, cherche à contourner les protections d'un logiciel, à s'introduire frauduleusement dans un système ou un réseau informatique. Voici la définition qu'on peut trouver dans le Larousse édition 2009. Le Hacker Space Festival 2009 A l'origine, hacker est un mot anglais signifiant bidouilleur, bricoleur. Aux origines du hacker : le phreaker John Draper (DR) Origine du cyberpunk
Les « bidouilleurs » de la société de l’information, par Jean-Ma En 2005, deux électroniciens découvrirent, stupéfaits, que les données confidentielles contenues dans la carte Vitale n’étaient pas protégées : on pouvait les lire, mais aussi les modifier. Pour d’obscures raisons, le mécanisme de sécurité n’avait pas été activé. L’affaire aurait pu faire scandale ; elle ne suscita que quelques articles de presse, et fut rapidement oubliée après que les responsables de la carte Vitale, tout en reconnaissant le problème, eurent déclaré qu’il serait corrigé. Quelques mois plus tard, l’un des deux électroniciens remonta au créneau en faisant remarquer que rien n’avait été fait. La sensibilité aux questions de vie privée, d’informatique et de libertés est autrement plus vive dans d’autres pays. Cette décision de justice tout comme la médiatisation internationale de cette (...) Taille de l’article complet : 2 001 mots. Vous êtes abonné(e) ? Connectez-vous pour accéder en ligne aux articles du journal. Vous n'êtes pas abonné(e) ? Accès sans abonnement
GNU Project The GNU logo, by Etienne Suvasa The GNU Project i/ɡnuː/[1] is a free software, mass collaboration project, announced on 27 September 1983, by Richard Stallman at MIT. In order to ensure that the entire software of a computer grants its users all freedom rights (use, share, study, modify), even the most fundamental and important part, the operating system (including all its numerous utility programs), needed to be written. The project's current work includes software development, awareness building, political campaigning and sharing of the new material. Origins[edit] Richard Stallman announced his intent to start coding the GNU Project in a Usenet message in September 1983.[3] Once the kernel and the compiler were finished GNU was able to be used for program development. The origins and development of most aspects of the GNU Project (and free software in general) are shared in a detailed narrative in the Emacs help system. GNU Manifesto[edit] Philosophy and activism[edit] Participation[edit]
How Heartbleed transformed HTTPS security into the stuff of absurdist theater If you want to protect yourself against the 500,000 or so HTTPS certificates that may have been compromised by the catastrophic Heartbleed bug, don't count on the revocation mechanism built-in to your browser. It doesn't do what its creators designed it to do, and switching it on makes you no more secure than leaving it off, one of the Internet's most respected cryptography engineers said over the weekend. For years, people have characterized the ineffectiveness of the online certificate status protocol (OCSP) as Exhibit A in the case that the Internet's secure sockets layer and transport layer security (TLS) protocols are hopelessly broken. Until now, no one paid much attention. Certificate revocation is the process of a browser or other application performing an online lookup to confirm that a TLS certificate hasn't been revoked. "That's why I claim that revocation checking is useless—because it doesn't stop attacks," Langley wrote.
How-To Permanently Delete Your Facebook Account Looking to permanently delete your Facebook account? Not surprising. Over the years, Facebook has seen its share of controversy in regards to the privacy of its users. It’s hard to say what sparked all the excitement: Rapid growth of its service? Whatever the reason, it’s obvious some no longer trust the social giant and I keep hearing the same question over and over again from my readers: “Is it possible to delete my facebook account?” and “I managed to deactivate it so it’s deleted right?” You would think the answer would be fairly straightforward. Personally, I feel Facebook has crossed the line of unethical behavior on this. Facebook Terms of Service Agreement – Section 2 - Sharing Your Content and Information – (updated 10/3/2012) You own all of the content and information you post on Facebook, and you can control how it is shared through your privacy and application settings. There is plenty there to chew on, especially the areas I’ve highlighted in bold. …is still in effect.
Free Culture movement Social movement concerning creative works The free-culture movement is a social movement that promotes the freedom to distribute and modify the creative works of others in the form of free content,[1][2] otherwise known as open content.[3][4][5] They encourage creators to create such content by using permissive and share-alike licensing, like that used on Wikipedia. Additionally, some free-culture advocates support piracy due to viewing copyright as illegitimate.[6] The movement objects to what it considers over-restrictive copyright laws. Many members of the movement argue that over-restrictive laws hinder creativity[7] and create a "permission culture", which they worry will shrink the public domain[8] and fair use. Background of the formation of the free-culture movement [edit] In 1998, the United States Congress passed the Sonny Bono Copyright Term Extension Act, which President Clinton signed into law. In 1999, Lessig challenged the Bono Act, taking the case to the US Supreme Court.
Advanced Search, Multicriteria with Planet, Sign and House With this advanced research, you can use 3 simultaneous criteria in order to search celebrities among 47,390 with good affinity with you. You can choose as criteria planets in signs with a powerful option, their position in degrees with a precision between 1 and 15 degrees, planets in astrological houses (Placidus), and houses (cuspids) in signs. When you click on the option "Add/substract a criterion" a window appears or disappears to continue the selection. Try to search for example celebrities who have the Sun on your Moon and the Moon on your Sun (husband/wife affinity), or Venus on your Mars and Mars on your Venus (sexual compatibility). If you increase the precision (more degrees) you 'll get more celebrities. You can also take a look at the conjunctions Pluton Vénus (passion and instinct), Uranus Venus (cerebral erotism), Soleil Venus (affective links), Moon Ascendant (mood and instinct): these critera are often used in astrology.
Hackers: Heroes of the Computer Revolution - Wikipedia, the free 1984 non-fiction book by Steven Levy The book saw an edition with a new afterword (entitled "Afterword: Ten Years After") by the author in 1994.[1] In 2010, a 25th anniversary edition with updated material was published by O'Reilly.[2] Levy traces developments in the history of hacking, beginning with The Tech Model Railroad Club at MIT, whose members were among the first hackers. Several chapters discuss the history of computer gaming, beginning with Spacewar! Other highlights include: Conway's Game of Life, a computer simulation written by John Horton Conway which became Bill Gosper's focus in 1970. Revolt in 2100: Lee Felsenstein and Jude Milhon founded Community Memory, an offshoot of Resource One based in Berkeley, California. PC Magazine stated that Levy "does capture the essential composite of the hacker personality but fails to accept that the true hacker, driven by machine lust, is equally content to hack in the corporate corridors.
About Creative Commons (CC) is an international nonprofit organization dedicated to helping build and sustain a thriving commons of shared knowledge and culture. Together with an extensive member network and multiple partners, we build capacity, we develop practical solutions, and we advocate for better open sharing of knowledge and culture that serves the public interest. As part of this work, we help overcome legal obstacles to the sharing of knowledge and creativity to address the world’s most pressing challenges. In order to achieve our mission, we: Learn more about CC through our mission and strategy and our collection of public reports and financials. For information about CC’s funding agreements, please see our Contributions Policy.
do you need hacking services? let me recommend to you the best hacker contact DAMERICANHACKER@GMAIL.COM or Whatsapp +1267 405 2105 by jenilo Jun 4