

Malware. Google's Safe Browsing Diagnostic Tool. A week ago Google announced the release of a safe browsing diagnostic tool.

To use the tool, just append a URL to the end of For example, to test this site, you would enter Google will then return four sets of security information about that page. (1) The current listing status of a site and also information on how often a site or parts of it were listed in the past. (2) The last time Google analyzed the page, when it was last malicious, what kind of malware Google encountered and so fourth. (3) Did the site facilitated the distribution of malicious software in the past? (4) Also, has the site has hosted malicious software in the past? Provos.pdf (application/pdf Object)
Fetch as Google - Webmaster Tools Help. Website Security Check - Unmask Parasites. About malware and hacked sites - Webmaster Tools Help. Cleaning your site - Webmaster Tools Help. Chaque jour, les cybercriminels piratent des milliers de sites Web.

Les piratages sont souvent invisibles pour les internautes, mais restent nuisibles pour toute personne qui consulte la page, y compris le propriétaire du site. Par exemple, à l'insu du propriétaire du site, le pirate informatique peut placer sur ce dernier un code malveillant capable d'enregistrer les frappes sur les ordinateurs des visiteurs. Le cybercriminel peut ainsi voler les identifiants qu'ils utilisent pour se connecter à leurs services bancaires en ligne ou effectuer des transactions financières. Cette vidéo aborde les sujets suivants: CCleaner. Www.stevengould.org - CleanUp! Home. RKill Download.
McAfee VirusScan Definition. Downloads. Internet Security and Ethical Hacking. The Ethical Hacker Network. Know your Enemy: Tracking Botnets. Scareware Definition. Scareware, also known as "rogue security software," is software that uses false error messages to lure you into purchasing a software program.

These alerts or warnings may appear on websites or within applications installed on your computer. When you click the associated download link, the software is downloaded to your computer. A typical scareware warning message will state that your computer is infected with a virus or malware without actually scanning your computer. The message will also recommend that you download software to "fix" the non-existent problem. Once you download the software, the installer may install spyware, adware, or other unwanted programs on your computer. In order to avoid scareware schemes, it is helpful to check the source of security alerts that pop up on your computer. 26 Online Backup Services Reviewed (Updated March 2013) 9.

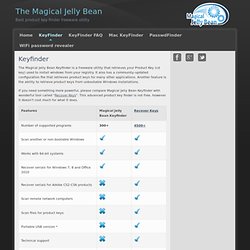
Livedrive Review. Protect The Business - Enable Access. Magical Jelly Bean. The Magical Jelly Bean Keyfinder is a freeware utility that retrieves your Product Key (cd key) used to install windows from your registry.
It also has a community-updated configuration file that retrieves product keys for many other applications. Another feature is the ability to retrieve product keys from unbootable Windows installations. If you need something more powerful, please compare Magical Jelly Bean Keyfinder with wonderful tool called "Recover Keys". This advanced product key finder is not free, however it doesn't cost much for what it does. Computer Security. Computer Security Jane F. Kinkus Mathematical Sciences Librarian Purdue Universityjkinkus@purdue.edu The term computer security is used frequently, but the content of a computer is vulnerable to few risks unless the computer is connected to other computers on a network.
As the use of computer networks, especially the Internet, has become pervasive, the concept of computer security has expanded to denote issues pertaining to the networked use of computers and their resources. The major technical areas of computer security are usually represented by the initials CIA: confidentiality, integrity, and authentication or availability. While confidentiality, integrity, and authenticity are the most important concerns of a computer security manager, privacy is perhaps the most important aspect of computer security for everyday Internet users. Scope of this Guide Methods General Sources Center for Education and Research in Information Assurance and. Free Tech Support - Computer Questions and Answers - Ask Bob Rankin. How to Protect Your Small Business Against a Cyber Attack.
The Seattle hacker drove a black Mercedes.

He owned a Rolex. He liked to frequent a downtown wine bar. While it's easy to think of cyber criminals as faceless, digital pickpockets in far-flung countries, the reality is that they are among us. In one notorious case, a bandit and his gang of cyber crooks compromised at least 53 Seattle-area small and medium-size businesses between 2008 and 2010, stealing enough data to cause $3 million in damages to the companies, their employees and their customers. Antivirus for Windows. Webutation - Website Reputation Community against fraud and badware. Support. Website Backup in the Cloud. WPSC.pdf. Why is my SSL web page insecure? Find the culprit! Digital Access Pass: Preventing SPAM Sign-Ups using G.A.S.P. technique. Digital Access Pass, as with any membership site that has a sign-up form, will be subject to SPAM.

If you’re not doing anything to prevent SPAMmers and bots, you’re likely going to get overwhelmed quickly. My solution was to adopt, and extend upon, the elegance of the Growmap Anti Spambot Plugin for WordPress comment spam. Athenaforensics. Computer hack. Network/Security. Hackers & hacking. WWW Health.