

Interaction Design Foundation. Privacy for anyone anywhere. RFC 821 - Simple Mail Transfer Protocol (RFC821) JavaScript. Nine-board Tic Tac Toe. Rules Nine-board tic-tac-toe is a tic tac toe variant where nine ordinary, 3-by-3 tic-tac-toe boards make up a 3-by-3 array.
Players take turns making marks (human 'X', computer 'O') in the ordinary tic-tac-toe boards. The first mark can appear anywhere. Each subsequent mark gets made in any un-marked spot in the ordinary board that corresponds to the spot where the previous mark got made. 10-year-old problem in theoretical computer science falls. Thomas VidickPhoto: M.

Scott Brauer Interactive proofs, which MIT researchers helped pioneer, have emerged as one of the major research topics in theoretical computer science. In the classic interactive proof, a questioner with limited computational power tries to extract reliable information from a computationally powerful but unreliable respondent. Interactive proofs are the basis of cryptographic systems now in wide use, but for computer scientists, they’re just as important for the insight they provide into the complexity of computational problems. Twenty years ago, researchers showed that if the questioner in an interactive proof is able to query multiple omniscient respondents — which are unable to communicate with each other — it can extract information much more efficiently than it could from a single respondent.
Piet (programming language) History[edit] Early implementations of INTERCAL were tied to the IBM System/360 and an unidentified Atari computer (probably the Atari 2600) and have not survived.

For many years INTERCAL was represented only by paper copies of the INTERCAL manual. The language's revival in 1990 as an implementation in C under Unix stimulated a wave of interest in the intentional design of esoteric computer languages. Turing tarpit. A Turing tarpit is a language that aims for Turing-completeness in an arbitrarily small number of linguistic elements - ideally, as few as possible.
History[edit] The 1950's and 1960's were something of a heyday for Turing tarpits. Academic interest in them was keen, and they enjoyed considerable popularity in computability research circles. Near the middle of the 1960's, however, the bubble of optimism surrounding them burst. In his 1987 paper The Busy Beaver Game and the Meaning of Life, Allen Brady relates a private conversation with John McCarthy (inventor of LISP) circa 1964 in which Prof.
We thought if we were to find the smallest universal machine then we could learn a great deal about computability -- of course that wouldn't be so! In the final chapter, Very Simple Bases for Computability, of his 1967 book Computation: Finite and Infinite Machines, Marvin Minsky writes: Top 10 Truly Bizarre Programming Languages. Technology This is a list of some of the most bizarre programming languages you will ever see.
These types of languages are usually called “Esoteric Programming Languages”. An esoteric programming language (sometimes shortened to esolang) is a computer programming language designed either as a test of the boundaries of programming language design, to experiment with weird ideas or simply as a joke, rather than for practical reasons. There is usually no intention of the language being adopted for real-world programming. Such languages are often popular among hackers and hobbyists. Usability is rarely a high priority for such languages; often quite the opposite. KI Bioinformatics and Computing Core Facility - Rous. The Little Lisper - Daniel P. Friedman, Linda Weiser Friedman, Matthias Felleisen. The Little lisper - The MIT PressThere are surprises in store for the diligent reader of this masterful introduction to recursion as a fundamental tool for expressing and solving problemsmitpress.mit.edu/catalog/item/default.asp?
Ttype=2&tid=4879 The little lisper (2nd ed.)The little lisper (2nd ed.) Purchase this Book. Source. Pages: 212. More The Little lisper@Everything2.comThe Little lisper seems unique in its approach to computer science instruction: the entire 200+ page book (and even the review on the back) are a series of ...everything2.com/e2node/The%2520Little%2520LISPer The little lisper [worldcat.org]The little lisper. Language Reference (API) \ Processing 2+ Prompt Magic. This is the approved revision of this page, as well as being the most recent.

[edit] Introduction. Saacs05.pdf (application/pdf Object) TheProduct/Gestalt. TheProduct. .fr-08: .the .product - a demo in 63.5 kb. The Bourne Again Shell (bash) 8.3.1 Environment Variables A Linux system is a complex beast, and there's a lot to keep track of, a lot of little details that come into play in your normal interactions with various programs (some of which you might not even need to be aware of).
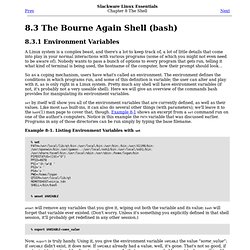
Nobody wants to pass a bunch of options to every program that gets run, telling it what kind of terminal is being used, the hostname of the computer, how their prompt should look... So as a coping mechanism, users have what's called an environment. The environment defines the conditions in which programs run, and some of this definition is variable; the user can alter and play with it, as is only right in a Linux system. Pretty much any shell will have environment variables (if not, it's probably not a very useable shell). Set by itself will show you all of the environment variables that are currently defined, as well as their values. Example 8-1. Now, export is truly handy. 8.3.2 Tab Completion (Here comes something cool again.) Collusion/website/demo.html at master · toolness/collusion. cURL - How To Use.
Curl - transfer a URL curl [options] [URL...] curl is a tool to transfer data from or to a server, using one of the supported protocols (DICT, FILE, FTP, FTPS, GOPHER, HTTP, HTTPS, IMAP, IMAPS, LDAP, LDAPS, POP3, POP3S, RTMP, RTSP, SCP, SFTP, SMB, SMBS, SMTP, SMTPS, TELNET and TFTP).

The command is designed to work without user interaction.