


Information ©Pat Ashforth & Steve Plummer 2014 In 2009 we suddenly took an interest in illusion knitting. It was very different from the mathematical work that can be found on the main part of the Woolly Thoughts site. As you move from page to page you will inevitably find some things repeated. Baby E - the noro entrelac scarf Ingredients- 3 skeins Noro Silk Garden (colourway 211 if you wanna be just like me). I used up just shy of three balls. I worked out I could cut out the boring grey bits of the end of the third ball and still have a long enough scarf. You can see the amount I didn't use in the pic at the end of this post.- 4.5mm bamboo needles Dimensions/ Specifications5 inches/ 13cm wide; 66 inches/ 166 cm long(X) = 5. TemplateI have chosen to write this pattern out with some flexibility, because when learning new techniques (like entrelac) I have difficulty separating what parts/ numbers of stitches are specific to the pattern, and what parts belong to the actual stitch pattern/ technique. What remains constant is that this is three blocks wide. Because of all that totally complex maths, you might like to copy this into Word and replace all the (X)es with the number you actually intend to use. Set Up TrianglesCast on 3 x (X) stitches. P2, turn.K2, turn.P3, turn.K3, turn.Continue until you P (X).
419 BAITER - Links When I first started scambaiting, I was inspired by a handful of sites. Unfortunately, a few of these sites have since vanished. I have listed the ones that remain. The Adventures of Wendy Willcox - I managed to locate this great story and thought, "Yeah, I could do that". I drew quite a bit of inspiration (and a few ideas) from Wendy's story. The 419 Game - Ebenezer Codpiece is back. What's the Bloody Point? After my first foray into this growing internet sport, I found many more sites devoted to scambaiting. 419 Eater - Claims to be the world's largest organized group of scambaiters. Scam-o-Rama - The operators of this site don't do any scambaiting themselves. Nigerian Money Scams - The Nigerian Letters - J. The Brad Christensen Exhibit - Hilarious scambaiting here, this guy even makes his scammers laugh, though not for long. theScamBaiter.com - Home of "Anus Laptops". www.scambuster419.co.uk - "Gilbert Murray" is one of the best waster of the scammers' time I've seen. Vladdio...
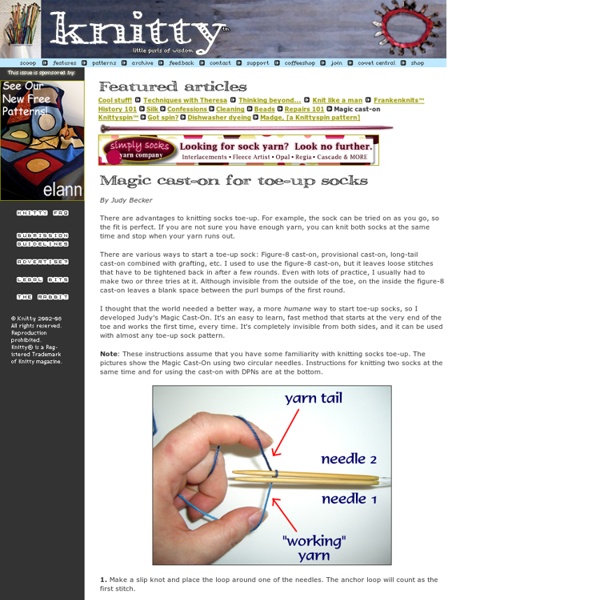
How to knit with two circulars How to knit small circumferences with two circulars You don't need double-pointed needles to knit small circumferences like sleeves, gloves, socks, and the top of hats. Instead you can use two circulars, which cuts the number of joins down to only two. A few people have claimed credit for this neat trick; I think it's one of those things that occured to multiple people about the same time. Select your needles You can use two circulars of any length; 16" through 29" seem to work the best. I prefer to use two needles with different cable lengths so I can always tell at a glance which needle I'm holding. If your two circulars are identical in brand and length (which makes them impossible to tell apart) you can place a marker after a few stitches have been worked on the first needle so you know the circular with the marker is needle #1. Casting on Cast on the required number of stitches onto one circular. How it works The concept is amazingly simple. That's it! [Go to my knitting start page]
Tricksy Knitter - Knitting Patterns (plus tips and tricks to help you knit) Top Ten 2.0 Tools – 2010 « John Steltz-Teacher/Author I am finishing my 14th year as an English-Language Arts teacher of students. I have grown more as an educator in this one academic year than in the lasGet Shortlinkt five years combined. I should really be more specific; I was on paternity leave for six weeks in November and December, so the new growth really didn’t begin until the New Year began. Through the assistance, encouragement, and on-going support of my colleague, Jessica (@jbrogley for Twitter followers), I have expanded my professional horizons to the vast frontier of technology. I can’t say enough about her confidence building personality, her willingness to help, and her wide range of Web 2.0 knowledge. It began with Twitter. Writing is a passion of mine and I was searching for an efficient way of sharing my writing with more people. Jessica sent me a link, maybe even through Twitter, to a Wiki that listed a plethora of Web 2.0 tools to for students (I consider myself a student too) to use, CoolToolsforSchools. 1. 2. 3. 4.
The Pretty Picot Cast On...a Tutorial I have uploaded two videos demonstrating the details of today's post, but in the first video, I was alone, and had to content with severe body contortion and a deep sustained squint (I was eventually sure that I was looking myself in the eye...) in order to film this here little clip... Normally my precious daughter does the filming while yours truly demonstrates knitting bliss, but in the first video, I set up my trusty tripod and after considerable trial and error , I managed to get the whole thing focused, while leaning, arms akimbo, back pretzeled, around the darned tripod. This resulted in me only being able to see what the heck I was doing , by looking at the video viewer a half inch from my nose :[ Ok, so what am I trying to say? The Picot Cast On...with a twist! Now, I am sure that the vast majority of readers out in Blogland, have already come across or even mastered this little cast on, and if you have, I am sorry... a tedious description will now follow... Cast on 5 stitches.
The Thumb Trick: Sometimes called an afterthought thumb, I first read about it in Elizabeth Zimmermann's Knitter's Almanac. I really like this method because it's seamless; sometimes when patterns have you place stitches on a holder and then cast on the top stitches you can get an odd seam right in the crease where your thumb meets the hand, and that can be uncomfortable. The only trouble that some people may have with this method is that you cannot immediately try on your mitten in progress, as you can with mittens where the stitches are put on holders. But if you want to you can just knit a few more rows and then pick up the stitches instead of waiting until the mitten is done, threading the waste yarn through them so you can try on your mittens as you knit. The trick: Knit to where you want to place the thumb hole, and take a length of contrasting yarn, and knit the thumbhole stitches with it instead of your working yarn: (see the working yarn, still on the right-hand side of the work?) Ta da!
31 Aquariums From Wow to WTF [Pics] People enjoy watching fish swim. It’s soothing in our otherwise crazy high-speed lifestyles. Fish habitats come in practically every shape and size you can imagine. Some are works of wonder while others are more like WTF were they thinking when they designed that aquarium. These are 31 of those very unique aquariums found around the world. Want an Aquarium? (image credits Born Rich,hometone,gizmodo,Sydney Morning Herald,Born Rich) Fish habitats have come a long way since simple rectangular aquariums or a round bowl. glass-art (image credits: Vanessa Mitrani ) If you have a fondness for glass art yet also want to keep fish as pets, there are dozens of options available for you. Ice (image credits doseng) Want fish but not the mess of cleaning their habitat? Strange or Cool? (image credits gizmodo,Born Rich,gizmodo,novate) The Spillarium has a waterfall effect to circulate and purify water in the aquarium. Fish Fans (image credits Luxury Housing Trends,Opulent Items,Opulent Items,Elseware Inc)
Maybe on my next pair of socks I'll give that a try. I only do the 1 or 2 circs method. Should work fine I'd say. by douglasgrendahl Dec 21
I have done it and it's not hard to master, although I have to read the directions again each time I use it. I usually do socks 2 at a time and there are instructions for that on the Internet too. I don't know if I've save that link in Pearltrees. by stacyw Dec 20
Ok, has anyone tried this technique and if so, comments? by douglasgrendahl Dec 20