


All FAR "Let me see your I.D." In 24 states police may require you to identify yourself (if they have reasonable suspicion that you’re involved in criminal activity.) “Stop and identify” statutes are laws in the United States that allow police to detain persons and request such persons to identify themselves, and arrest them if they do not. In the United States, interactions between police and citizens fall into three general categories: consensual (“contact” or “conversation”), detention (often called a Terry stop), or arrest. Consensual At any time, police may approach a person and ask questions. Police are not usually required to tell a person that he is free to decline to answer questions and go about his business; however, a person can usually determine whether the interaction is consensual by asking, “Am I free to go?” Detention Police may briefly detain a person if they have reasonable suspicion that the person has committed, is committing, or is about to commit a crime. Arrest Related
Returning Home to the US is to Enter a Police State A few weeks ago, I got a vivid comparative look at how far this country has moved towards becoming a police state. The occasion was a brief visit to Montreal, where my wife was to give a harpsichord recital at an early keyboard music conference. At the Canadian border crossing, just above Lake Champlain, the Canadian official politely asked us our purpose in coming to Canada. Informed it was to perform harpsichord music at a music conference, he actually asked my wife what composers she was playing! On our way back into the US, we found ourselves being questioned by a grim-faced, beefy, cop-like guy, complete with sidearm, about where we’d been and what we’d done in Canada. The stupid thing, of course, about such questions, is that if I actually were doing something illegal — say passing stolen state secrets to a spy connection in Canada, or meeting with some terrorist organization to plot a bombing in the US — I certainly wouldn’t offer that information to a border patrol officer.
13 Things the Government Is Trying to Keep Secret From You - Page 2 of 2 Six. The Government is fighting to keep Top Secret a key 2011 decision of the FISA court even after the court itself said it can be made public There is an 86 page 2011 top secret opinion of the FISA court which declared some of the National Security Agency’s surveillance programs unconstitutional. The Administration, through the Department of Justice, refused to hand this over to the Electronic Frontier Foundation which filed a public records request and a lawsuit to make this public. First the government said it would hurt the FISA court to allow this to be made public. Then the FISA court itself said it can be made public. Seven. With a NSL letter the FBI can demand financial records from any institution from banks to casinos, all telephone records, subscriber information, credit reports, employment information, and all email records of the target as well as the email addresses and screen names for anyone who has contacted that account. Eight. Nine. Ten. Eleven. Twelve. Thirteen.
Darkness in the heart of America: Why the Snowden docs should really make us nervous Here, at least, is a place to start: intelligence officials have weighed in with an estimate of just how many secret files National Security Agency contractor Edward Snowden took with him when he headed for Hong Kong last June. Brace yourself: 1.7 million. At least they claim that as the number he or his web crawler accessed before he left town. Such figures should stagger us and what he did take will undoubtedly occupy journalists for months or years more (and historians long after that). And keep something else in mind: that’s just intelligence agencies. We do know that, in 2011, the whole government reportedly classified 92,064,862 documents. Summoned From the Id of the National Security State In the face of such boundlessness, perhaps the words “whistleblower” and “leaker” — both traditionally referring to bounded and focused activities — are no longer useful. In a sense, valuable as they have been, Snowden’s revelations have helped promote this delusion.
View Daily Life in a Japanese-American Internment Camp Through the Lens of Ansel Adams Seventy-five years ago, nearly 120,000 Americans were incarcerated because of their Japanese roots after the bombing of Pearl Harbor. More than 10,000 were forced to live in the hastily built barracks of Manzanar—two thirds of whom were American citizens by birth. Located in the middle of the high desert in California's Eastern Sierra region, Manzanar would become one of the best-known internment camps—and in 1943, one of America’s best-known photographers, Ansel Adams, documented daily life there. As Richard Reeves writes in his history of Japanese-American internment, Adams was friends with the camp’s director, who invited him to the camp in 1943. But his photo shoot did not go as planned. Adams wasn’t the only noteworthy photographer to train his lens on Manzanar. Though internees were initially banned from using cameras inside Manzanar, photographer Tōyō Miyatake defied the rules and photographed the camp anyway.
Judge orders tech company to release Web user data from anti-Trump website The DOJ wants personal data of visitors of this Trump protesters' website DreamHost is resisting a DOJ search warrant for more than 1.3 million IP addresses to identify visitors to a website set up to coordinate protests on Inauguration Day. DreamHost is resisting a DOJ search warrant for more than 1.3 million IP addresses to identify visitors to a Trump protestor website. DreamHost is resisting a DOJ search warrant for more than 1.3 million IP addresses to identify visitors to a website set up to coordinate protests on Inauguration Day. A D.C. During an hour-long hearing, attorneys for DreamHost, which hosts the website Disruptj20.org, argued the federal search warrant still was too broad and would include information about people who visited the site but were not part of violent Inauguration Day rioting. DreamHost attorney Raymond Aghaian said the site was not an anti-Trump website but an “advocacy site that addresses political issues.” Judge Robert E. local public-safety follow-dallas
Who Confesses to a Crime They Didn't Commit? We like to believe that there is no more reliable evidence of a crime than a confession. Why would anyone admit to a crime they didn't commit? Yet my research into all of the 250 innocent exonerations suggests that innocents actually confess to a lot. In doing so, they may reportedly offer up crime scene details known to nobody but police investigators. The case of Frank Sterling is illustrative. In 1988, an elderly woman, out for a walk, was killed in Rochester, N.Y. To try to get more out of him, an investigating officer used a hypnotic-type "relaxation" technique, in which he laid down beside Sterling, held his hand, and they breathed deeply. At trial, officers testified they never told Sterling any of those key facts, although one admitted he showed Sterling some crime scene photos during the interrogation. Finally, Sterling even agreed that no one put those words in his mouth, that he did not "dream this up," and the detectives did not influence him.
Do You Have A Right to Remain Silent? Thoughts on the “Sleeper” Criminal Procedure Case of the Term, Salinas v. Texas This morning the Supreme Court decided a very important criminal procedure case, Salinas v. Texas, by a 5-4 vote. I’m guessing that you haven’t heard of Salinas. I. To understand Salinas, you need to know a little bit of Fifth Amendment history. Two cases in the mid-1960s made important cracks in that doctrinal edifice. The second case that cut against the traditional understanding of the Fifth Amendment was Miranda v. The complex set of rules announced in Miranda was justified as a way of protecting the Fifth Amendment right. In accord with our decision today, it is impermissible to penalize an individual for exercising his Fifth Amendment privilege when he is under police custodial interrogation. So after 1966, we have essentially two ways of thinking about the Fifth Amendment right against self-incrimination. II. In particular, “right” in what sense? III. That brings us (finally) to the new case, Salinas v. Justice Thomas penned a short 2-page concurrence joined by Justice Scalia.
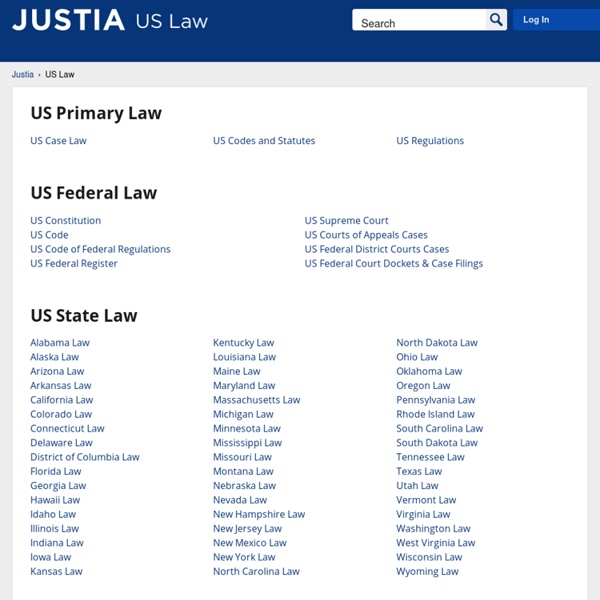
Justia; Provides access to US and State codes, regulations, case law and more. by thecyberesq May 19