


DVWA (4/4) : Solutions, explications et étude des protections DVWA, ou Damn Vulnerable Web Application, fait généralement partie des premiers travaux pratiques sur lesquels on se penche pour débuter en audit/pentest. Dans ces quatre articles, nous allons étudier les solutions aux défis qui sont présents sur DVWA, l’intérêt sera alors de comprendre pourquoi une vulnérabilité est présente, comment la détecter, comment l’exploiter et enfin comment s’en protéger, ce qui est de loin le plus important. Note : Les méthodes et procédés d’attaque expliqués dans ces articles ont pour objectif de vous faire comprendre les enjeux de la sécurité et l’importance de la protection du système d’information. Pour rappel, l’utilisation de ces attaques sur des systèmes réels est strictement interdite et passible de peines d’emprisonnement ainsi que d’amendes lourdes. Plus d’informations ici : atteintes aux systèmes de traitement automatisé de données. Voici les autres articles de cette série : Failles de type File Upload Quelles conséquences pour la sécurité ?
About Exploit Exercises ha.ckers.org web application security lab Here we are, my friends. The 1000th post. Whew! It’s quite a load off to have finally made it. It wasn’t that long ago that I unfortunately lost my love affair with security. I started ha.ckers.org as a place for me to experiment on my own, and share ideas with a few like-minded folks. With any kind of work you get a sense of anxiety. They say that if you look at the graph of happiness in your life you can tell what sort of life you led. I’m not an oracle and I really don’t like giving people incorrect information. Although I’m a fun loving person in many ways I also tend to be a pessimist and I do take things too seriously sometimes - definitely to a fault. So this is it - I’m taking my happiness back and I’ll be taking on new and exciting challenges without the drama of intense public scrutiny. So… where can this mythical happiness monster be found, you may be asking?
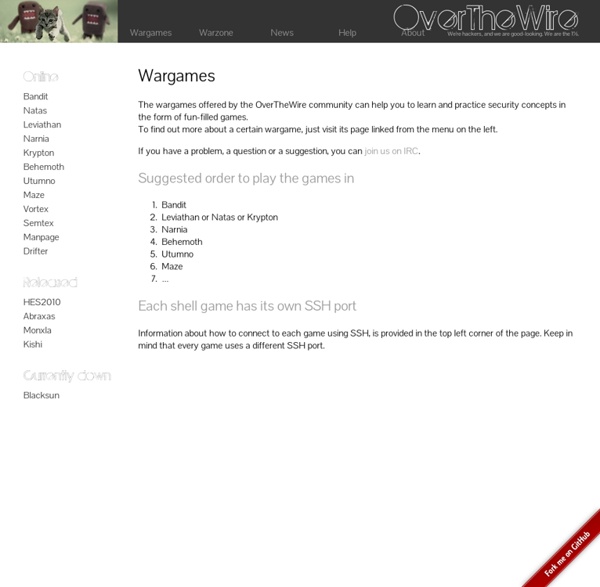
professional education - What "hacking" competitions/challenges exist? I don't know a good reference to point to for further reading. Thus I will try to list a few time-wasters that I personally enjoy. In the following I will allow myself to differentiate between various styles of hacking competitions. I don't know if this is a canonical approach, but it will probably help explaining the differences between the ones I know: These games take place on given server, where you start with an ssh login and try to exploit setuid-binaries to gain higher permissions. These games are usually available 24/7 and you can join whenever you want. These games will present you numerous tasks that you can solve separately. These actually require you to capture and protect "flags". iCTF (typically in December)CIPHER CTF (will be renewed by new organizers this year)RuCTF and RuCTFe (a Russian CTF and its international version) There are also a bunch of downloadable virtual machines available to play offline, which is some kind of mix between 3) and 2) I suppose. Edit: /Edit
CS50.tv This is CS50 OpenCourseware. Computer Science 50 (otherwise known as CS50) is Harvard College's introductory course for majors and non-majors alike, a one-semester amalgam of courses generally known as CS1 and CS2 taught mostly in C. Even if you are not a student at Harvard, you are welcome to "take" this course via cs50.tv by following along via the Internet. If you're a teacher, you are welcome to adopt or adapt these materials for your own course, per the license. If you'd like to take this course for real (on Harvard's campus or via the Internet) in order to receive feedback on work, grades, and a transcript, the course will next be offered through Harvard Extension School (as "Computer Science E-50") in Fall 2013; you can register online starting in July 2013. Special thanks to Dan Coffey, Shelley Westover, Andrew Hill, Colton Ogden, Ramon Galvan '16, and Kenny Boyle for the course's videos and to Rob Bowden '13, Daven Farnham, and Gabriel Guimaraes '17, Fall 2014's heads. djm
Des podcasts sur la sécurité informatique - Information Security Lorsque l’on fait de la veille informatique, plusieurs supports peuvent se présenter à nous. Parmi eux, un « nouveau » que j’ai découvert récemment dans le domaine de la sécurité informatique, les podcasts audio. Je vais ici vous présenter deux podcasts français que j’ai découvert récemment et qui méritent d’être plus largement diffusés : Comptoir Sécu et NoLimitSecu. Des podcasts ? Il s’agit en effet de podcasts, qui prennent la forme d’émissions radio, que l’on peut donc écouter le matin en allant au travail dans la voiture ou dans les transports en commun. Ces podcasts sont plutôt dédiés à une population technique, ou du moins ayant des connaissances en informatique plutôt que le grand public. Comptoir Sécu Les premiers podcasts ont débutés en mai 2013 et depuis, il en sort un par mois. Parmi les sujets traités dernièrement (lors de l’écriture de ce billet), on trouve par exemple le malware Poseidon, la présentation du DEFNET 2015. No Limit Secu
Hack.me - Build, Host & Share Vulnerable Web Application Code Hack.me is a FREE, community based project powered by eLearnSecurity. The community allows you to build, host and share vulnerable web application code for educational and research purposes. It aims to be the largest collection of “runnable” vulnerable web applications, code samples and CMS’s online. The platform is available without any restriction to any party interested in Web Application Security: students, universities, researchers, penetration testers and web developers. Features Upload your own code Online IDE for PHP & MySQL Your code hosted in the cloud FREE!! Safety Every time you run a new Hackme the site will initiate a new sandbox for you. What about the 1%? We have written about a variety of web apps where you can practice your hack-fu such as: So head over to hack.me and see what you think:
Dan Kaminsky's Blog 1 Live CD + many reads/videos 'Super Markup World' tests your HTML chops in an oddly satisfying platformer If using HTML to navigate a Mario-inspired world sounds like the perfect platformer for you, ‘Super Markup World‘ is not to be missed. The game lacks a real storyline or characters, but it does have a helpful blinking blue dot that guides you through HTML challenges that progress in difficulty as you advance. Our best speaker lineup, ever. This year’s edition of TNW Conference in Amsterdam includes some of the biggest names in tech. Learn more Unlike Mario games, Super Markup World isn’t about finding the princess or jumping on flagpoles, but instead features a series of puzzles that you solve from the HTML command window at the top of the screen. Although it lacks any elements that would make this a typical platformer, such as music, a storyline or even a defined end goal, Super Markup World was a satisfying time killer that allowed us to knock the dust off of our HTML knowledge for a practical purpose. ➤ Super Markup World [Daggasoft via Product Hunt]
DVWA (3/4) : Solutions, explications et étude des protections DVWA ou Damn Vulnerable Web Applications fait généralement partie des premiers travaux pratiques sur lesquels on se penche pour débuter en audit/pentest de sécurité. Dans ces quatre articles, nous allons étudier les solutions aux défis qui sont présents sur DVWA, l’intérêt sera alors de comprendre pourquoi une vulnérabilité est présente, comment la détecter, comment l’exploiter et enfin comment s’en protéger, ce qui est de loin le plus important. Note : Les méthodes et procédés d’attaque expliqués dans ces articles ont pour objectif de vous faire comprendre les enjeux de la sécurité et l’importance de la protection du système d’information. Voici les autres articles de cette série : Dans le précédent article, nous nous sommes intéressés aux failles de sécurité CSRF et File Inclusion. Failles de type SQL Injection Les failles de type SQL Injection sont parmi les failles les plus courantes et les plus dangereuses dans le domaine des applications web. Résultat :