

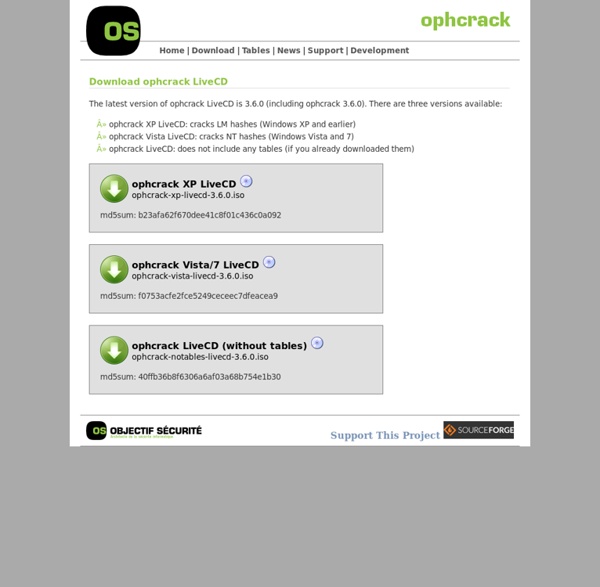
7 Free Windows Password Recovery Tools Trinity Rescue Kit needs to be booted from a disc or USB stick to work. It includes many different tools, one of which is for password recovery. You can use Trinity Rescue Kit to clear a password entirely, making it blank, or to set a custom one. Some of you may find this program difficult to use because there isn't a graphical interface. Trinity Rescue Kit should work with Windows 10, 8, 7, Vista, and XP. Trinity Rescue Kit v3.4 Free Download Note: The password resetting tool in Trinity Rescue Kit, called winpass, is actually just an automated script for the chntpw tool, which is what Offline NT Password & Registry Editor, listed above, is based on.
How I Started Learning Python Disclaimer: If you already know Python really well, this post might not be handy for you. However, I’d still love to see your comments and feedback if you have a moment to reply. Much of my recent work has centered on OpenStack and I’ve found myself overwhelmed by learning Python. Although I don’t have any formal education on anything related to computer science or programming, I’ve worked my way through PHP, Perl and Ruby. Ruby seems to be the most comfortable language for me to use due to the simplicity of the syntax and the handy features provided by the standard libraries and common gems. Python always caught me as strange due to the forced indenting (I indent my code properly anyway, but it still feels weird to be forced to do so), module namespaces and the overall syntax. All of that had to change over the past few months. Learn Python The Hard Way Zed Shaw’s guide to learning Python has been the primary recommendation from every Python developer I’ve polled at Rackspace.
How to Clean an LCD Screen | Electronics The “L” in LCD stands for “liquid,” and what holds this liquid in is not a glass plate like you remember having on your big, heavy CRT or television. It’s soft plastic, and you’ve got to treat it very delicately. So, first of all, let’s decide what we don’t use to clean it: Anything containing bleach or ammonia, such as Windex. That will react with the plastic and make the plastic screen become cloudy and discolored.Anything sharp, pointy or abrasive. Your easiest choice is one of those LCD cleaning solutions they sell in places where they sell computers. What you’ll need: Distilled water (available at your supermarket; tap water leaves streaks and minerals).White vinegar (you may substitute isopropyl alcohol; either way, make sure these substances are diluted before they come near your screen).A clean, soft cloth (never use any kind of paper product).A spray bottle. Directions: Hands Off! Fingers leave dirt and oil smudges that must be cleaned off.