


About Roundcube Webmail This project is a free and open source webmail solution with a desktop-like user interface which is easy to install/configure and that runs on a standard LAMPP server. The skins use the latest web standards to render a functional and customizable UI. Roundcube includes other sophisticated open-source libraries such as PEAR, an IMAP library derived from IlohaMail the TinyMCE rich text editor, Googiespell library for spell checking or the WasHTML sanitizer by Frederic Motte. Released features Planned features Support for PGP and S/MIME encryption Online calendar module Advanced search over all folders Virtual folders (aka saved searches) Keyboard shortcuts Attachment previews Responsive skin for mobile devices Save/link attachments in cloud storage services Conversation view using XCONVERSATIONS Browser history support Admin interface See the development roadmap for more. Server Requirements More detailed list of requirements License Screenshots See our Supporters
mindmup Capture ideas at the speed of thought – using a mind map maker designed to help you focus on your ideas and remove all the distractions while mindmapping. Create unlimited mind maps for free, and store them in the cloud. Your mind maps are available everywhere, instantly, from any device. Brainstorm, create presentations and document outlines with mind maps, and publish your ideas online and to social networks. Get Started Why use MindMup? MindMup is great for individual note-taking, collaborative planning, teamwork and classrooms. 1 Powerful keyboard shortcuts speed up your work 2 Frictionless interface helps you focus 3 Convert maps easily to PDF, PowerPoint, outlines... 4 Publish and share maps online 5 Easily save to Google Drive and manage using Google Apps
Roundcube - Free and Open Source Webmail Software Features Deployment choice Install on your existing Linux servers (single or cluster) or install as VM. On premise, hosted or in your SOE through the Atmail provisioning API. As full server or on top of your IMAP/PoP stack. Full implementation and installation support. Easy Migration Need to migrate, and migrate quickly? Regulatory Fully regulatory compliant through lawful intercept and logging. Detailed user management What the admin gives, the admin can take away. Mass mail Notify your users en masse with the Mass mail utility. Plug-ins & Mash-ups Add extra functionality through the our documented plug-in framework for headache free version upgrades. Unlimited domains Multi tenancy enabled and no license restrictions on the number of domains. Authentication Integrate your Atmail with LDAP, Database Auth or OS Authentication. Sub-Administrator support Start delegating. Full source code You've got the skills, we've got the tools. Slim and scalable
Indie Box: Let's Bring Our Data Home The first ready-to-use personal server appliance for storing personal data and running indie web applications at home. Made for humans, not just geeks. Pre-installed indie web applications provide functionality such as calendaring, address book management, publishing, sharing, bookmarking, photo and media management and more. Indie Box One eliminates the need to entrust our personal data to big internet companies who often share and use it in ways we don't appreciate. For the first time in history, individuals now produce and collect large amounts of valuable data. For many of us, this valuable data includes years worth of e-mail, a myriad of digital family pictures, our bookmarks, our blog posts and tweets, but increasingly also health and fitness data, financial and commercial transactions, and data generated by the growing set of internet-of-things devices in our homes. Hardware You have two choices: our hardware or your hardware. Software Auto-administration A: It isn't. No.
Top 5 Email Client For Linux, Mac OS X, and Windows Users Linux comes with various GUI based email client to stay in touch with your friends and family, and share information in newsgroups with other users. The following software is similar to Outlook Express or Windows Live Mail and is used by both home and office user. Webmail interfaces allow users to access their mail with any standard web browser, from any computer, rather than relying on an e-mail client. However, e-mail client remains extremely popular in a large corporate environment, small business, home and power users. An e-mail client (also mail user agent (MUA)) is a frontend computer program used to manage e-mail. Mail can be stored on the client, on the server side, or in both places. The following are top five amazing piece of cross-platform software from various projects to make your life easy with wide variety of plug-ins / add-ons. #1: Mozilla Thunderbird It is an e-mail and news cross-platform client software package by Mozilla Foundation. Fig.01: Mozilla Thunderbird
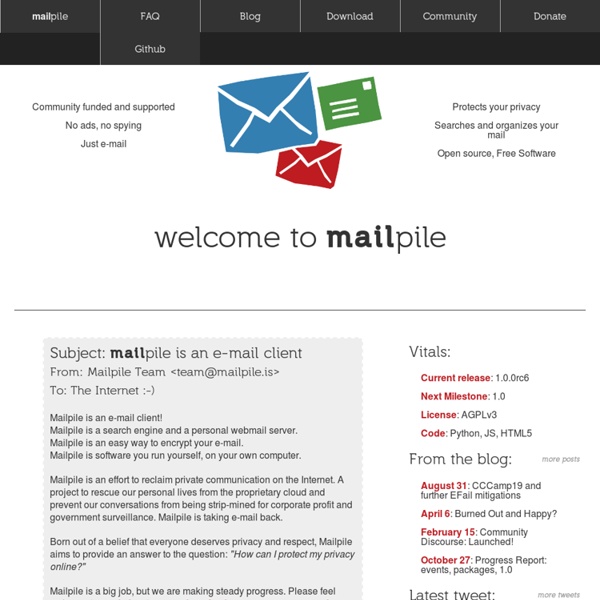
ActiveInbox: Make your Inbox your Donebox Mailpile: Turning Money Into Code Posted by Bjarni on August 20, 2013 With three weeks left of our campaign, we have already reached our goal of $100,000 USD! This is absolutely fantastic and we are deeply grateful to all of you for believing in us and supporting our vision with your hard earned cash. We have already had this discussion in private with some of our larger backers, but we feel it is only right to make a public statement about this and keep our entire community informed. A Young Project Mailpile is a project which is just in its infancy. Over the next few months, we need to sort out a lot of things to do with the infrastructure of the project: We need a community forum to continue interacting with our backersWe need automated tests for our code-baseWe need to define APIs for plug-ins and interacting with external appsWe need to further develop our theme architectureWe need to solidify the overall design of the system, so it is clear where and how people can pitch in What Can Money do? Thank you for your support!
Atmail - Messaging Platform. Email Server, Webmail & Calendar. Overview Rooms intelligently organize all your stuff. Your inbox can become a tangled mess of stuff. It's constantly filling with a stream of new messages, saved messages, forwarded messages, contacts, web links, embedded images, links to items in the cloud, all kinds of attachments: documents, spreadsheets, presentations—and plenty more. Yikes! Now, there’s a way to intelligently extract and convert the contents of your inbox into neatly organized, structured and shareable content. No matter what shape it arrived in, everything gets sorted for you into convenient ccGenie Rooms. It's automatic and it's magical. Rooms are the workspaces where your new content assets live—the places you store your stuff. ccGenie creates an array of content assets and groups these into your Rooms as Documents, Conversations, Notes, and People. You can have several Rooms and you can belong to many. Reserve your ccGenie Room right now or read on to learn more.
Persona || Email Reimagined A people focussed email experience where you can manage your message threads with specific contacts quickly and easily. You can manage particular ‘threads’ or ongoing discussions with a number of contacts, such as a group of friends or coworkers. See every attachment and get a bird’s eye view of everything and decide which ones you want to open, delete, or manage. Composing an email is a hassle free experience with a simple full screen view of your mail in progress, with a focus primarily on your writing. more Mail Pilot for Mac, iPhone + iPad: Task-oriented email
IQTELL - Everything In One Place Productivity App