


Full Path Disclosure This is an Attack. To view all attacks, please see the Attack Category page. Last revision: 11/8/2012 Description Full Path Disclosure (FPD) vulnerabilities enable the attacker to see the path to the webroot/file. e.g.: /home/omg/htdocs/file/. Risk Factors The risks regarding FPD may produce various outcomes. Warning: session_start() [function.session-start]: The session id contains illegal characters, valid characters are a-z, A-Z, 0-9 and '-,' in /home/example/public_html/includes/functions.php on line 2 In combination with, say, unproteced use of the PHP function file_get_contents, the attacker gets an opportunity to steal configuration files. The sourcecode of index.php: An attacker crafts a URL like so: The leaked sourcecode of config.php: Disregarding the above sample, FPD can also be used to reveal the underlaying operation system by observing the file paths. Microsoft Windows: The FPD may reveal a lot more than people normally might suspect. Examples Empty Array
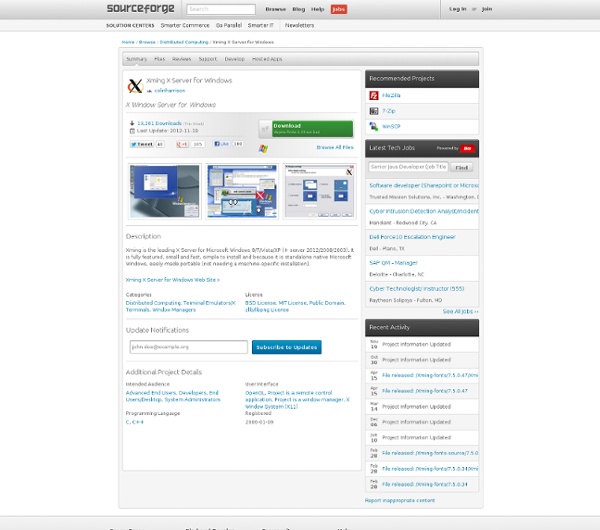
Xming X Server for Windows - Official Website Xming is the leading X Window System Server for Microsoft Windows®. It is fully featured, lean, fast, simple to install and because it is standalone native Windows, easily made portable (not needing a machine-specific installation or access to the Windows registry). Xming is totally secure when used with SSH and optionally includes an enhanced Plink SSH client and a portable PuTTY replacement package. Xming installers include executable code, and libraries, only built by me, Colin Harrison (Project Xming's chief developer) + this website is free of adverts, pop-ups and usage tracking of any kind, including cookies, and is hosted on machines only administered by me. Mesa with GLX, or Microsoft WGL, provide interactive OpenGL® 2D and 3D network transparent graphics rendering. AIGLX is available for graphics cards that support hardware-accelerated OpenGL. Xming is cross-compiled on Linux for Microsoft Windows, using MinGW-w64, mostly from canonical X.Org source code with my patches applied. X.Org,
PuTTY Download Page Home | FAQ | Feedback | Licence | Updates | Mirrors | Keys | Links | Team Download: Stable · Snapshot | Docs | Changes | Wishlist PuTTY is a free implementation of SSH and Telnet for Windows and Unix platforms, along with an xterm terminal emulator. It is written and maintained primarily by Simon Tatham. The latest version is 0.70. Download it here. LEGAL WARNING: Use of PuTTY, PSCP, PSFTP and Plink is illegal in countries where encryption is outlawed. Use of the Telnet-only binary (PuTTYtel) is unrestricted by any cryptography laws. Latest news 2017-07-08 PuTTY 0.70 released, containing security and bug fixes PuTTY 0.70, released today, fixes further problems with Windows DLL hijacking, and also fixes a small number of bugs in 0.69, including broken printing support and Unicode keyboard input on Windows. 2017-04-29 PuTTY 0.69 released, containing security and bug fixes 2017-02-21 PuTTY 0.68 released, containing ECC, a 64-bit build, and security fixes We've also redesigned our website. Site map
accountkiller Spring Financial is a finance company based in Canada. The company was founded in 2014. Spring Financial is a subsidiary of Canada Drives, which is a leading auto financing company in Canada. Upon loan approval, the funds will go into a secure trust account. Canceling your loan is simple. Web semántica El precursor de la idea, Tim Berners-Lee, intentó desde el principio incluir información semántica en su creación, la World Wide Web, pero por diferentes causas no fue posible.[2] Por ese motivo introdujo el concepto de semántica con la intención de recuperar dicha omisión. Relación con Internet[editar] La web semántica es una ampliación de la Web, por medio de la que se intenta realizar un filtrado de manera automática pero precisa de la información. En la actualidad, la World Wide Web está basada principalmente en documentos escritos en HTML, un lenguaje de marcado que sirve principalmente para crear hipertexto en Internet. HTML permite mediante una herramienta de visualización (como un navegador o un agente de usuario) mostrar por ejemplo un catálogo de objetos en venta. La web semántica se ocuparía de resolver estas deficiencias. Barreras[editar] Las tecnologías para expresar la información en el formato que requiere una web semántica existen hace años. Avances[editar]
Quick Unix Reference Unix Help 1 Log In Session 1.1 Log In Enter username at login: prompt. Be carefull - Unix is case sensitive. Enter password at password: prompt. 1.2 Change Password passwd 1.3 Log Out logout or exit 2 File System 2.1 Create a File cat > file Enter text and end with ctrl-D vi file Edit file using the vi editor 2.2 Make a Directory mkdir directory-name 2.3 Display File Contents cat file display contents of file more file display contents of file one screenfull at a time. view file a read only version of vi. less file similar to, but more powerfull than more. 2.4 Comparing Files diff file1 file2 line by comparison cmp file1 file2 byte by byte comparison 2.5 Changing Access Modes chmod mode file1 file2 ...chmod -R mode dir (changes all files in dir ) Mode Settings u user (owner) g group o other + add permission - remove permission r read w write x execute Example: chmod go+rwx public.html adds read, write, and execute permissions for group and other on public.html. 2.8 Copy Files simple: ?
CHAOS (operating system) Designed for large-scale ad hoc clusters, once booted, CHAOS runs from memory allowing the CD to be used on the next node (and allowing for automated rebooting into the host operating system). CHAOS aims to be the most compact, secure and straightforward openMosix cluster platform available.[2] A six node CHAOS/openMosix cluster: The mosmon view with no load While this deployment model suits the typical cluster builder, openMosix is a peer-based cluster, consisting of only one type of node. All openMosix nodes are inherently equal and each can be, simultaneously, parent and child. A six node CHAOS/openMosix cluster: The mosmon view with one process' load, launched from node two A six node CHAOS/openMosix cluster: The mosmon view with four process' load, launched from node two A six node CHAOS/openMosix cluster: The mosmon view with nine process' load, launched from node two The tool used to provide the cryptographic tests was John the Ripper (JtR).
Datos enlazados En informática , los datos enlazados o datos vinculados (a menudo capitalizados como Linked Data, en inglés) describe un método de publicación de datos estructurados para que puedan ser interconectados y más útiles. Se basa en tecnologías Web estándar, tales como HTTP, RDF y los URI, pero en vez de utilizarlos para servir páginas web para los lectores humanos, las extiende para compartir información de una manera que puede ser leída automáticamente por ordenadores. Esto permite que sean conectados y consultados datos de diferentes fuentes. Tim Berners-Lee, director del Consorcio de la World Wide Web, acuñó el término en una nota de diseño que trataba de cuestiones relativas al proyecto de Web Semántica. El término "datos enlazados" hace referencia al método con el que se pueden mostrar, intercambiar y conectar datos a través de URIs desreferenciables en la Web. Principios[editar] Componentes[editar] Proyecto de comunidad para la inter-conexión de datos abiertos[editar] Ejemplos[editar]
Cygwin Windows Automated Installation Kit History[edit] Windows AIK Version 1.0 was released with Windows Vista. New or redesigned tools and technologies included Windows System Image Manager (Windows SIM), SysPrep, ImageX, and Windows Preinstallation Environment (WinPE) v2.0.[2] Windows AIK Version 1.1 was released with Windows Vista SP1 (and Windows Server 2008). A number of new tools were introduced, including PostReflect and VSP1Cln. The new WinPE 2.1 could be more customized.[3] Supported operating systems include Windows Server 2008, Windows Vista, Windows Vista SP1, Windows Server 2003 SP1, Windows Server 2003 SP2 and Windows XP SP2. Windows AIK Version 2.0 was released with Windows 7 beta. Windows AIK version 3.0 is exactly the same as 2.0. The AIK has been renamed The Windows Assessment and Deployment Kit (ADK) for Windows 8 and now includes the Windows OEM Preinstallation Kit. [6] The Sysprep tool is not included with WAIK, but is instead included on the Operating System installation media (DVD). Features[edit] Concepts
Linked data An introductory overview of Linked Open Data in the context of cultural institutions. In computing, linked data (often capitalized as Linked Data) describes a method of publishing structured data so that it can be interlinked and become more useful. It builds upon standard Web technologies such as HTTP, RDF and URIs, but rather than using them to serve web pages for human readers, it extends them to share information in a way that can be read automatically by computers. This enables data from different sources to be connected and queried.[1] Tim Berners-Lee, director of the World Wide Web Consortium, coined the term in a design note discussing issues around the Semantic Web project.[2] Principles[edit] Tim Berners-Lee outlined four principles of linked data in his Design Issues: Linked Data note,[2] paraphrased along the following lines: All kinds of conceptual things, they have names now that start with HTTP.I get important information back. Components[edit] European Union Projects[edit]
ActivePython is Python for Windows, Mac, Linux, AIX, HP-UX & Solaris ActivePython Business and Enterprise Editions feature our precompiled, supported, quality-assured Python distribution used by millions of developers around the world for easy Python installation and quality-assured code. When you're using Python on production servers or mission-critical applications, ActivePython Business and Enterprise Editions offer significant time savings over open source Python for installing, managing, and standardizing your Python. Want Python on the cloud? Not sure which edition is right for you? Tested, Timely and Compatible Save time in your development cycles by starting with a precompiled Python distribution for out-of-the-box installation and standardization across the operating systems you rely on, including Windows, Linux, Mac OS X, Solaris, AIX, and HP-UX. ActivePython Business and Enterprise Editions includes: Business Edition licensing is for each production or external-facing server, including virtual servers. Additional Python Modules Free Custom pricing