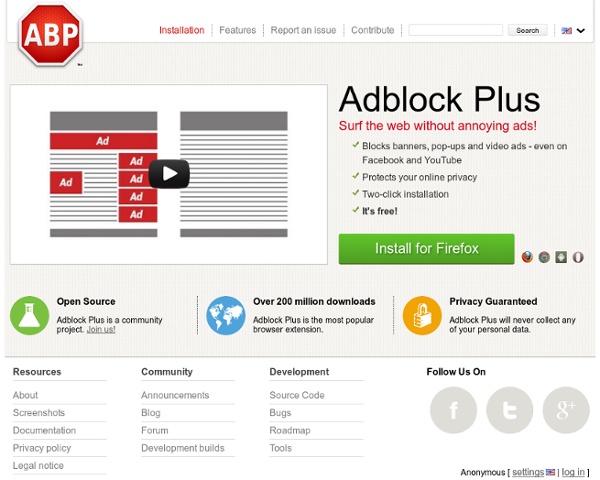
Adblock Plus — for annoyance-free web surfing
Download Firefox Adblock Plus Firefox is a free and open source browser available for Windows, OS X, Linux, and Android which supports addons. Addons are extensions to your browser to improve privacy and security and the way you view the web. Since its launch in 2006, Adblock Plus has continuously been the most popular addon for the Mozilla Firefox web browser. Adblock Plus for Firefox is more than a popup blocker. Are you troubled by banners, overlays and other annoying advertisements?
http://adblockplus.org/en/
NoScript - JavaScript/Java/Flash blocker for a safer Firefox experience! - what is it? - InformAction
Comodo Firewall Free
CNET Editors' Choice, 5-Star Rated Comodo Firewall Pro introduces the next evolution in computer security: Default Deny Protection (DDP™). What is DDP? Most security programs maintain a list of known malware, and use that list to decide which applications and files shouldn't access a PC.
TrackMeNot
Background Public awareness of the vulnerability of searches to systematic surveillance and logging by search engine companies, was initially raised in the wake of a case, initiated August 2005, in which the United States Department of Justice (DOJ) issued a subpoena to Google for one week's worth of search query records (absent identifying information) and a random list of one million URLs from its Web index. This was cited as part of its defense of the constitutionality of the Child Online Protection Act (COPA). When Google refused, the DOJ filed a motion in a Federal District Court to force compliance. Google argued that the request imposed a burden, would compromise trade secrets, undermine customers' trust in Google, and have a chilling effect on search activities.
BOINC malariacontrol - Linguistic Team International Wiki
From Linguistic Team International Wiki Return to BOINC Project Gateway The Project! The malariacontrol.net project is an application that makes use of network computing for stochastic modelling of the clinical epidemiology and natural history of Plasmodium falciparum malaria. Click here for more information. The project does the following simulations and more:
Ghostery
OpenDNS - Cloud Internet Security
7 billion people and you: What's your number?
Sources: All population data are based on estimates by the UN Population Division and all calculations provided by the UN Population Fund. The remaining data are from other sections of the UN, the Global Footprint Network and the International Telecommunications Union. Want to find out more? Visit the UN Population Fund's detailed population calculator, 7 billion and me.
Firebug
VirtualNES.com
Click a letter above to open the games menu! Hundreds of vintage Nintendo Entertainment System games are available here on VirtualNES.com, most of which you can access using the alphabar above this paragraph. Just click a letter, and you'll magically be taken away to a list of NES games that happen to start with that letter. However, there are some special games, such as unlicensed games, that we maintain separate lists for.
FoxTab
Lost Pyramids of Egypt Found Using Google Earth?
From: ArchaeologyNewsNetwork Two unidentified, possible pyramid complexes have been located with satellite imagery from Google Earth. One of the complex sites contains a distinct, four-sided, truncated, pyramidal shape that is approximately 140 feet in width.
Greasemonkey
Related:



Well, Not Completely Ad-free, Theres still popups. by pearlcat Jun 18
Finally, An Ad-free Internet. Recommended. by pearlcat Jun 18