AdwCleaner Download
BleepingComputer Review: AdwCleaner is a free program that searches for and deletes Adware, Toolbars, Potentially Unwanted Programs (PUP), and browser Hijackers from your computer. By using AdwCleaner you can easily remove many of these types of programs for a better user experience on your computer and while browsing the web. The types of programs that AdwCleaner targets are typically bundled with free programs that you download from the web.
They Are Coming For Our Water
Dave HodgesActivist Post America is under attack in so many ways, it is difficult to count. Along these lines, there is presently a three-pronged globalist plot designed to subjugate the people of this country.
Carpe Noctem - Seize the NightCarpe Noctem – Seize the Night
LSD was invented in Switzerland by Albert Hofmann, a researcher for Sandoz pharmaceuticals. The CIA was on to acid long before the flower children. It did not spontaneously appear among the youth of the Western world as a gift from the God of Getting’ High. So, for that matter, were upstanding citizens like Time-Life magnate Henry Luce and his wife, Clare Boothe Luce, who openly sang the praises of their magical mystery tours during the early sixties.
15 ferramentas importantes para criar apresentações bonitas
Ever since MS PowerPoint revolutionized corporate and marketing communication in the early part of the millennium, presenting ideas through attractive slideshows has become a mandatory component of any successful and engaging presentation. The effectiveness of any presentation relies heavily on the styling, structure and attractiveness of the slides that are being used to address the audience. This is why, over the years, marketers and communicators have focused heavily on bringing innovation and creativity in their presentations.
What Can You Do to Stop NSA Spying?
Michael MaharreyActivist Post Rosa Parks faced what likely seemed a hopeless situation at the time. Majority opinion, backed by the strong arm of government, relegated her to second-class citizenship. In that day, who imagined it would ever change? Parks was riding the Cleveland Avenue bus home from work in Montgomery, Alabama on Dec. 1, 1955, when the white only seats in the front filled with passengers.
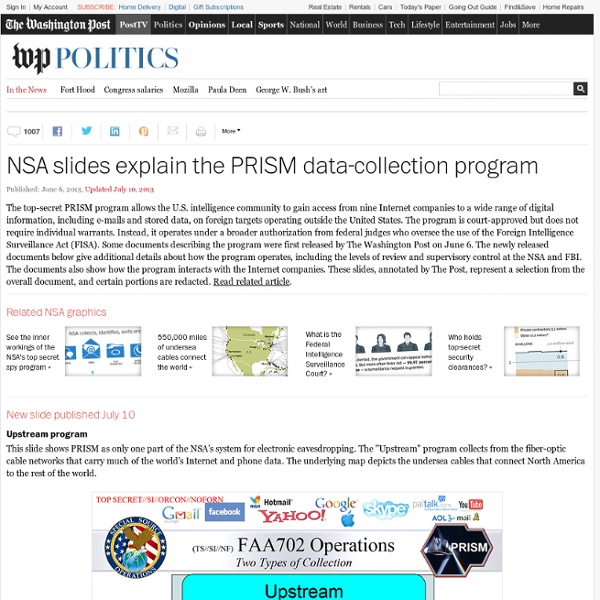
How the NSA's Domestic Spying Program Works
The NSA’s domestic spying program, known in official government documents as the “President’s Surveillance Program,” ("The Program") was implemented by President George W. Bush shortly after the attacks on September 11, 2001. The US Government still considers the Program officially classified, but a tremendous amount of information has been exposed by various whistleblowers, admitted to by government officials during Congressional hearings and with public statements, and reported on in investigations by major newspaper across the country. Our NSA Domestic Spying Timeline has a full list of important dates, events, and reports, but we also want to explain—to the extent we understand it—the full scope of the Program and how the government has implemented it. In the weeks after 9/11, President Bush authorized the National Security Agency (NSA) to conduct a range of surveillance activities inside the United States, which had been barred by law and agency policy for decades.
Carlos Lobo (carlos_lobo_5473) on We Heart It
We Heart It View cover Drag to reposition cover Carlos Lobo novas artes 5 12 days ago in collection: novas artes
These Are Not the Normal Activities of a Government Planning for Peace and Stability
Mac SlavoActivist Post Something is amiss. Most Americans know this – they can feel it deep down inside – even if they don’t know what it is, things just don’t seem right. The signs are everywhere.
Millions of Americans installing 'perfect spying device' in their own living rooms: Amazon Fire TV monitors and records your conversations - NaturalNews.com
Tuesday, July 15, 2014by Mike Adams, the Health RangerTags: Amazon Fire TV, audio surveillance, perfect spying device (NaturalNews) Amazon.com is building the CIA's new $600 million data center, reports the Financial Times. (1) At the same time Amazon.com is building this massive cloud computing infrastructure for the CIA, the company is also shipping millions of Fire TV set-top devices to customers who are placing them in their private homes. I have one myself, and it's a terrific piece of hardware for delivering Prime video content. In fact, in terms of its usability and specs, it's far superior to Roku or Netflix-capable devices. Fire TV is, hands down, the best set-top video delivery device on the market today. But there's something about it that always struck me as odd: it has no power button.
The Quackery of Chemotherapy, Gunpoint Medicine and the Disturbing Fate of 13-Year-Old Daniel Hauser
(NaturalNews) You see it in newspapers and websites across the 'net: People insisting that 13-year-old Daniel Hauser must be injected with chemotherapy in order to "save his life," and that anyone refusing to go along with that is a criminal deserving of arrest and imprisonment. What's most astonishing about the mainstream reaction to the forced chemotherapy of Daniel Hauser is not merely that they believe states now own the children, but that they believe in the entire world there exists but one single treatment for cancer, and it happens to be the one that makes pharmaceutical companies the most money. The arrogance (and ignorance) of that position is mind boggling. There was once a time when western medical doctors believed that the heavy metal mercury was a medicine, too. They methodically used mercury to treat hundreds of different diseases and conditions, oblivious to the fact that they were actually poisoning people with this toxic heavy metal.
MIT Updates Wi-Fi Tech That Can Track You Through Walls
Kevin SamsonActivist Post One of the hallmarks of technology is dual-use capability. It is for this reason that we are softened up with all of the benefits, before being introduced to the darker side.