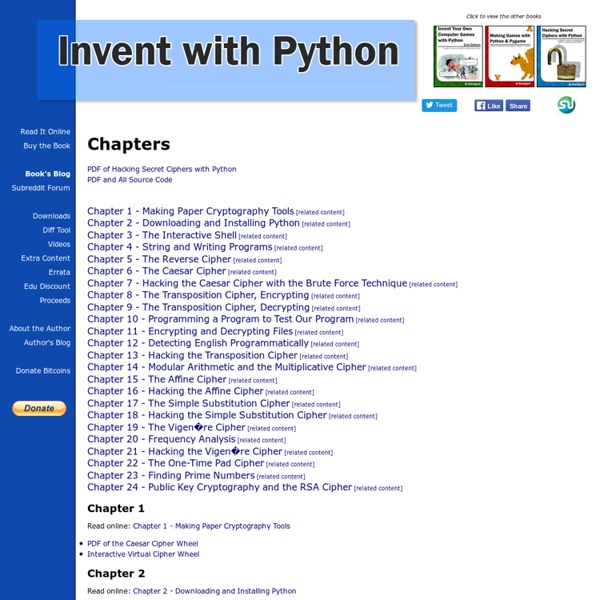
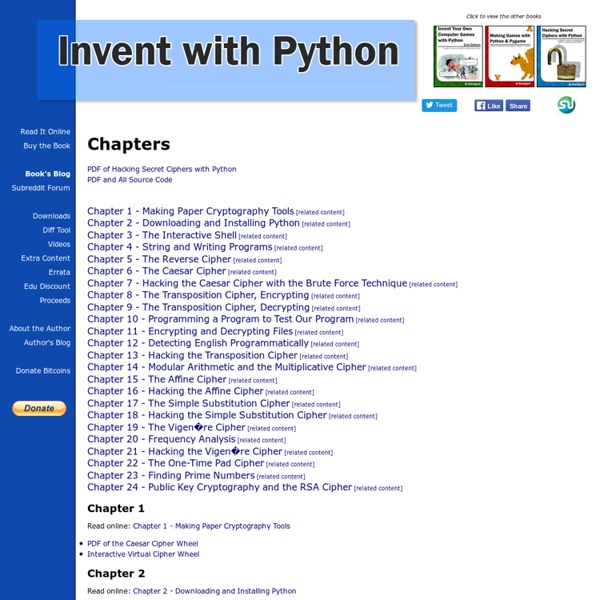
Hacking Secret Ciphers with Python - Chapters
Hacking for Artists
Уроки | Рисование в Фотошопе
Большая коллекция уроков рисования в фотошопе, в которых Вы сможете изучить основы и освоить как базовые навыки, так и фишки для продвинутых цифровых художников. В основном темы уроки рисования в фотошопе, собранные здесь, можно класcифицировать по нескольким разделам: Основа рисованияРисование людейПейзажиИнструменты фотошопаСпецэффекты Всех тонкостей работы с программой Adobe Photoshop здесь вряд ли удастся найти, т.к. материал этого раздела для тех, кто хочет научиться рисовать в фотошопе, а не освоить инструменты для фотомонтажа. Хотите научиться рисовать в фотошопе? Хороший совет: Главное в достижении успеха в рисовании — это практика и любовь к этому занятию. Чем больше Вы будете прогрессировать в направлении рисования, тем больше будет проявляться тяга к рисованию, а любимое дело всегда делать приятней! Всё, что нужно для того, чтобы преступить к урокам рисования в фотошопе — это, конечно же, фотошоп и желательно графический планшет для рисования. Как нарисовать лису Как рисовать облака
Main Page - Procedural Content Generation Wiki
Попаданцев.нет
PyBrain
Dive Into Python
Making Games with Python and Pygame
Book Description This is a programming book that covers the Pygame game library for the Python programming language. Each chapter gives you the complete source code for a new game and teaches the programming concepts from these examples. The book is available under a Creative Commons license and can be downloaded in full for free from This book was written to be understandable by kids as young as 10 to 12 years old, although it is great for anyone of any age who has some familiarity with Python. About the Authors Albert Sweigart (but you can call him Al), is a software developer in San Francisco, California who enjoys bicycling, volunteering, haunting coffee shops, and making useful software. He is originally from Houston, Texas.
Invent Your Own Computer Games with Python - Learn how to program with a free ebook programming tutorial
Chapter 1 Read online: Chapter 1 - Installing Python Videos: Chapter 2 Read online: Chapter 2 - The Interactive Shell Chapter 3 Read online: Chapter 3 - Strings Download source: hello.py Copy source to clipboard: Use the online diff tool to find typos in your code: hello.py Chapter 4 Read online: Chapter 4 - Guess the Number Download source: guess.py Use the online diff tool to find typos in your code: guess.py Chapter 5 Read online: Chapter 5 - Jokes Download source: jokes.py Use the online diff tool to find typos in your code: jokes.py Chapter 6 Read online: Chapter 6 - Dragon Realm Download source: dragon.py Use the online diff tool to find typos in your code: dragon.py Chapter 7 Read online: Chapter 7 - Using the Debugger Chapter 8 Read online: Chapter 8 - Flow Charts Chapter 9 Read online: Chapter 9 - Hangman Download source: hangman.py Use the online diff tool to find typos in your code: hangman.py Chapter 10 Read online: Chapter 10 - Tic Tac Toe Download source: tictactoe.py Chapter 11 Download source: bagels.py
cocos2d
Rosetta Code
IDA: About
What is IDA all about? IDA is a Windows, Linux or Mac OS X hosted multi-processor disassembler and debugger that offers so many features it is hard to describe them all. Just grab an evaluation version if you want a test drive. An executive summary is provided for the non-technical user. Getting IDA IDA is available for many platforms, and can be licensed under different terms. Support & Community We have placed a sensible amount of support links and documentation online that can be valuable both to new, and advanced users. Additionally, our user board is a valuable source of hints and tips for the IDA Disassembler. Technical Documentation Intro to the IDA Debugger. Screenshots
hugi 35 - demoscene resources adok demo sourcecode list
Demo Sourcecode List By Adok/Hugi Most of the following are links to sources of demos or demo-related products (e.g. intros, games) for Windows. Some are for Linux, and a few are for platforms that can be emulated on PC, such as Game Boy, C64 or Amiga. I take no warranty for anything. Scene.org has a directory with source codes. Feel free to notify me of new source code releases so that I can add them to this list! Adok/Hugi
Related:
Related: