


Welcome! - SmoothWall Types of Network Protocols What is a Network Protocol A protocol is a set of rules that govern the communications between computers on a network. These rules include guidelines that regulate the following characteristics of a network: access method, allowed physical topologies, types of cabling, and speed of data transfer. Types of Network Protocols The most common network protocols are: Ethernet Local Talk Token Ring FDDI ATM The followings are some commonly used network symbols to draw different kinds of network protocols. Ethernet The Ethernet protocol is by far the most widely used one. The Ethernet protocol allows for linear bus, star, or tree topologies. Fast Ethernet To allow for an increased speed of transmission, the Ethernet protocol has developed a new standard that supports 100 Mbps. Local Talk Local Talk is a network protocol that was developed by Apple Computer, Inc. for Macintosh computers. The Local Talk protocol allows for linear bus, star, or tree topologies using twisted pair cable. Token Ring
Editors Choice Notifications See all notifications All categories Marvin King Sveta Yaroshuk pollography Joan Le Jan Ryan Longnecker Stanislav Istratov Sebastian Tontsch Miguel Serra Elke Vogelsang John7 Jaime Penzellna Michael Underwood C/ marhraoui Ana Santl Babak Fatholahi Bob Cargin Photography David Uzochukwu Jesse Herzog Gyo Terauchi Max Gor Nicholas Ray raquel chicheri Geoffrey Greslin Visoot Uthairam Vincent DHETINE Foo J. Marsel van Oosten Derek Burdeny Andre Perry Kaiwan Abdulrahman Ale Di Gangi Simon Migaj Arnaud Moro 19.tides DGReps 马谦 Radius Images Chris Schmid Lamelle Albert Dros Made Devy Deria Justin Adam Lee Monologist Matt Jacobs Franz Weber Dyln Engls Amina Gingold Finished | Back to top Scroll to top
EtherApe, a graphical network monitor Communications protocol In telecommunications, a communications protocol is a system of digital rules for data exchange within or between computers. In computer science, when data is exchanged through a computer network, the rules system is called a network protocol. Communicating systems use well-defined formats for exchanging messages. Each message has an exact meaning intended to provoke a particular response of the receiver. Communicating systems[edit] In digital computing systems, the rules can be expressed by algorithms and data structures. Operating systems usually consist of a set of cooperating processes that manipulate shared data to communicate with each other. In contrast, because there is no common memory, communicating systems have to communicate with each other using a shared transmission medium. To implement a networking protocol, the protocol software modules are interfaced with a framework implemented on the machine's operating system. Basic requirements of protocols[edit] Protocol design[edit]
RFC 20 - ASCII format for network interchange [Docs] [txt|pdf] [Tracker] [Errata] INTERNET STANDARD Errata Exist Network Working Group Vint Cerf Request for Comments: 20 UCLA October 16, 1969 For concreteness, we suggest the use of standard 7-bit ASCII embedded in an 8 bit byte whose high order bit is always 0. This leads to the standard code given on the attached page, copies from USAS X3, 4- 1968. This code will be used over HOST-HOST primary connections. Break characters will be defined by the receiving remote host, e.g. 1. This coded character set is to be used for the general interchange of information among information processing systems, communication systems, and associated equipment. RFC 20 ASCII format for Network Interchange October 1969 2. RFC 20 ASCII format for Network Interchange October 1969 3. RFC 20 ASCII format for Network Interchange October 1969 4. 4.1 Control Characters RFC 20 ASCII format for Network Interchange October 1969 4.2 Graphic Characters Column/Row Symbol Name 2/0 SP Space (Normally Non-Printing) 2/1 !
Svitsjeprinsipper Innholdet i denne siden og sidene som ligger under alle pekerene, skal du ha kjennskap til. Både lyd og bilde kan digitaliseres. Derfor er elektronisk kommunikasjon basert på overføring av digitale signaler. En kilde sender ut en strøm av informasjon. Mange kilder med info-strøm skal behandles samtidig og overføres til mottaker så raskt som mulig. For å kunne skape en effektiv info-strøm, må info fra hver kilde deles i enheter. Figuren nedenfor viser i prinsippet hvordan enheter fra forskjellige kilder overføres på samme linje. Multipleksing er ikke en enkel metode eller prinsipp, men en samlebetegnelse på metoder og prinsipper som gjør det mulig å overføre mange signaler (telefonsamtaler, datafiler, bilder, video, ...) samtidig på en felles overføringskanal. Det skilles mellom to fundamentalt forskjellige priunsipper for multipleksing: frekvensdelt multipleksing (FDM) og tidsdelt multipleksing (TDM). Det er mulig å kombinere tids- og frekvensdelt multipleksing .
Computer Networking Computer networks differ in the physical media used to transmit their signals, the communications protocols to organize network traffic, the network's size, topology and organizational intent. In most cases, communications protocols are layered on (i.e. work using) other more specific or more general communications protocols, except for the physical layer that directly deals with the physical media. Computer networks support applications such as access to the World Wide Web, shared use of application and storage servers, printers, and fax machines, and use of email and instant messaging applications. History[edit] A computer network, or simply a network, is a collection of computers and other hardware components interconnected by communication channels that allow sharing of resources and information. The following is a chronology of significant computer network developments: Properties[edit] Network packet[edit] Main article: Network packet Network topology[edit] Network links[edit]
Emoji Symbols often used as emotional cues in text The "Grinning Face" emoji, from the Twemoji set Originating on Japanese mobile phones in 1997, emoji became increasingly popular worldwide in the 2010s after being added to several mobile operating systems.[5][6][7] They are now considered to be a large part of popular culture in the West and around the world.[8][9] In 2015, Oxford Dictionaries named the Face with Tears of Joy emoji (😂) the word of the year.[10][11] History Evolution from emoticons (1990s) Wingdings icons, including smiling and frowning faces Kurita's emoji were brightly colored, albeit with a single color per glyph. Development of emoji sets (2000–2007) The basic 12-by-12-pixel emoji in Japan grew in popularity across various platforms over the next decade. Smiley faces from DOS code page 437 The Smiley Company developed The Smiley Dictionary, which was launched in 2001. Beginnings of Unicode emoji (2008–2014) UTS #51 and modern emoji (2015–present) Cultural influence Color support
OSI model Model with 7 layers to describe communications systems The Open Systems Interconnection model (OSI model) is a conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system without regard to its underlying internal structure and technology. Its goal is the interoperability of diverse communication systems with standard protocols. The model partitions a communication system into abstraction layers. The original version of the model defined seven layers. A layer serves the layer above it and is served by the layer below it. The model is a product of the Open Systems Interconnection project at the International Organization for Standardization (ISO). Communication in the OSI-Model (example with layers 3 to 5) History[edit] In the late 1970s, the International Organization for Standardization (ISO) conducted a program to develop general standards and methods of networking. Description of OSI layers[edit] Layer 1: Physical Layer[edit]
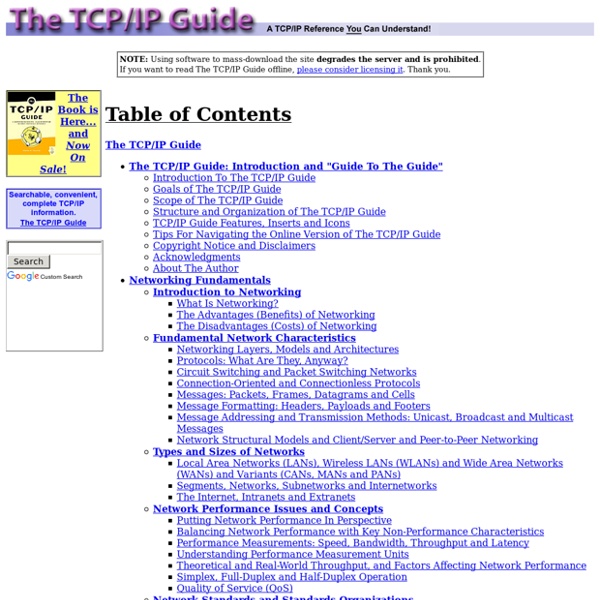
Internet protocol suite The Internet protocol suite is the computer networking model and set of communications protocols used on the Internet and similar computer networks. It is commonly known as TCP/IP, because its most important protocols, the Transmission Control Protocol (TCP) and the Internet Protocol (IP), were the first networking protocols defined in this standard. Often also called the Internet model, it was originally also known as the DoD model, because the development of the networking model was funded by DARPA, an agency of the United States Department of Defense. TCP/IP provides end-to-end connectivity specifying how data should be packetized, addressed, transmitted, routed and received at the destination. The TCP/IP model and related protocol models are maintained by the Internet Engineering Task Force (IETF). History[edit] Early research[edit] Diagram of the first internetworked connection Specification[edit] Adoption[edit] Key architectural principles[edit] Abstraction layers[edit] Link layer[edit]
All TLDs Network Cabling Standards Guide, By Siemon Home > Standards Dear customers, partners and friends, At Siemon, we believe industry standards help you achieve the most out of your networks. For this reason, we have put together a guide to network cabling and data center standards. We are pleased to introduce: Standards Informant. Standards Informant is a new website covering a wide range of standards topics including twisted-pair cabling, fiber optic cabling, data center standards, pathways and spaces, bonding and grounding, industrial premises standards, building automation systems, energy efficiency and a whole lot more. We hope you enjoy the new Standards Informant website. Thanks, - All of Us at Siemon Standards Update Learn what's going on in with standards development with this Industry Standards Activity Overview of activites in TIA, IEEE, ISO/IEC JTC 1/SC 25/WG 3 (Customer Premises Cabling), IEC SC 48B (Connectors), and BISCI. »Download PDF Shielded Copper Cabling Resource Center »Shielded Cabling Resource Center »Full Article »More
How TCP/IP Works When transmitting data, the Transport layer gets data from the Application layer and divides them into several data packets. TCP (Transmission Control Protocol) is the most used protocol on the Transport layer. When receiving data, TCP protocol gets the packets sent by the Internet layer and put them in order, because packets can arrive at the destination out-of-order, and also checks if the contents of the received packet are intact and sends an acknowledge signal to the transmitter, allowing it to know that the packet arrived intact at destination. If no acknowledge signal is received (either because it didn’t arrive the destination or because TCP found out that data was corrupted), the transmitter will re-send the lost packet. While TCP re-orders packets and also uses this acknowledge system we mention, which is desirable when transmitting data, there is another protocol that works on this layer that does not have these two features.