


Atom 1.0 disponible para descargar Desde hace bastante tiempo estoy usando para trabajar como FrontEnd dos editores de texto bastante famosos, me estoy refiriendo a Sublime Text y Brackets, siendo este último el que uso de forma predeterminada. En su momento había probado versiones previas de Atom y nunca me convenció. Era bastante lento, su auto-completado de código era ineficiente y carecía de muchísimas opciones, sin embargo, con la versión 1.0, disponible hace un par de días, el panorama ha cambiado y mucho. ¿Qué nos trae Atom? Como ya mencioné, una de las cosas que más me molestaba de las versiones previas de Atom era su triste y decadente auto-completado de código, pero en esta versión ha mejorado muchísimo gracias a autocomplete-plus, el cual viene instalado en forma de paquete. Personalización al máximo Lo increíble de todo esto es que se ha mejorado muchísimo el rendimiento de la aplicación, así como su respuesta al escribir texto. Brackets aún sigue siendo para mi una mejor opción para el trabajo como FrontEnd.
Telechargement Civilization V [PC] Megaupload ★ MesDDl | Votre paradis du download Éditeur : 2K GamesDéveloppeur : FiraxisType : StratégieNote du test : 17/20Note des joueurs : 15/20Date de sortie Française : 24 septembre 2010 (21 septembre 2010 aux Etats-Unis) Annoncé début 2010, dévoilé à l’occasion de plusieurs previews plutôt prometteuses, Civilization V n’aura mis que quelques mois à fédérer les attentes d’une communauté de fans toujours plus nombreux, qui se plaisent à réécrire 6000 ans d’histoire humaine à chaque nouveau volet. Mais c’est aussi pour attirer un public encore plus large que Firaxis, le studio de Sid Meier, fait le pari du (…) Hébergeur : MultiSourceFormat : ISOPlateforme : PCLangue : Multi-5 Français Découper avec : WinRar Nombre et taille des fichiers 3 X 999 Mo et 1 X 315 Mo Total du post : 3312 Mo Uploaded – Turbobit - Gigasize - Rapidgator Le crack et patch seul : Uploaded - Turbobit - Gigasize - Rapidgator Mot de passe de décompression : *UpByPatshanka* Rating: 9.5/10 (2 votes cast) Civilization V [PC], 9.5 out of 10 based on 2 ratings Lien remplacé !!
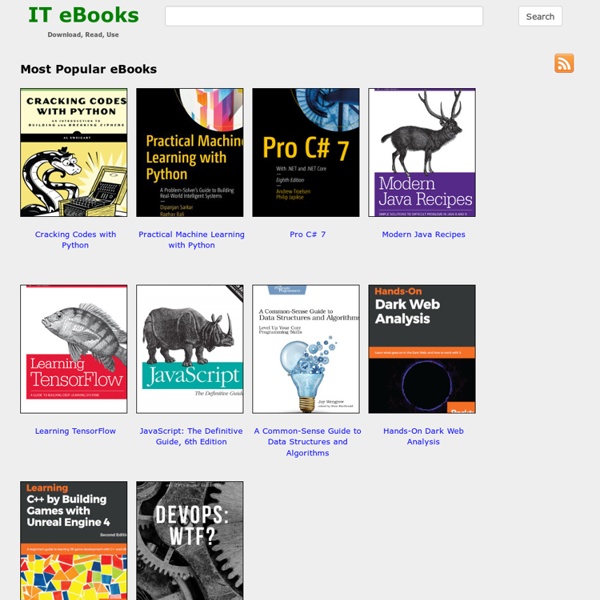
Free eBooks Download From RapidShare eBooks | Free Download eBooks Book Depository: Millions of books with free delivery worldwide Agile Principles, Patterns, and Practices in C# eBook: Robert C. Martin, Micah Martin 5 webs con libros electrónicos gratuitos de programación En cumplimiento de lo establecido en la Ley Orgánica 15/1999, el 13 de diciembre, de Protección de Datos de Carácter Personal, te informamos que mediante la cumplimentación del presente formulario estás dando el consentimiento expreso a que sus datos personales queden incorporados y sean tratados en un fichero de El arte del programador con la finalidad de poder gestionar tu solicitud. El fichero será gestionado por El arte del programador, que actúa como responsable del fichero. Asimismo, salvo que manifiestes expresamente lo contrario, se podrán utilizar tus datos personales para mantenerte informado de noticias y novedades relacionadas con nuestros servicios.
Ebook Search & Free Ebook Downloads - Ebookbrowse.com Ultimate List of Top 50 Free Ebook Download Websites & Ebook Search Engines - Fedobe Have you ever wanted to get your hands on the perfect pdf or ebook but could not figure out where to search for the damn book. Well you know what, this is your lucky day as today you will be getting the complete list all the websites from where you can search for to download almost any pdf ebook. And if you have any more resources or websites to add to the list, feel free to suggest them in the comment. ManyBooks Offers 36,000 free ebooks which you can download to ur system by just clicking a button Gutenburg Enlightens on wide range of books for free downloading Ebooks A free e-books links library where you can find and download free books in almost any category Globusz One of he most happening site having a large number of freely downloadable documents.It helps in promoting your own ebooks with great ease. EbookLink Helps in finding totally filtered data about everything going on with daily updates rendering effciency KnowFree Wide Collection of free online pdf books and pdf ebooks FreeBookSpot
Learning jQuery, Third Edition eBook: Jonathan Chaffer Libros del Programador