


Topsy - Real-time search for the social web With iOS 9, Search lets you look for content from the web, your contacts, apps, nearby places, and more. Powered by Siri, Search offers suggestions and updates results as you type. There are two ways to use Search on your iOS device. Quick Search Drag down from the middle of the Home screen and type what you're looking for. Siri Suggestions Drag right from the Home screen to show Search and get Siri Suggestions. Get Siri Suggestions Siri Suggestions include apps and contacts that you might be interested in. You can use Siri Suggestions with iPhone 5 and later, iPad Pro, iPad (4th generation) and later, iPad mini (2nd generation) and later, and iPod touch (6th generation). Change search settings Go to Settings > General > Spotlight Search. From here, you can turn Siri Suggestions on or off and choose which apps to include in your searches. If you don’t want Siri or Spotlight to suggest nearby locations, go to Settings > Privacy > Location Services. Last Modified:
Search Lately, there has been a lot of discussion about the future of our information consumption. Are we going to be using search in a different way or using niche search engines? Are we going to get recommendations from from our social network? AJ Kohn has an excellent example of what Facebook could do. What if Facebook added a simple More Like This link to certain news feed items? The benefit of context within your social network stream could also aid this process. GigaOm thinks that recommendation is still the holy grail for news: What the media industry really needs is some way to filter all of that information in useful ways, and recommend things you might not have read yet…social networks like Twitter and Facebook have proven to be the best way of getting recommended content. In this little quote, they actually mention three different ideas. You will notice that I have mentioned “context” several times. So, is there a holy grail? How does search fit into all of this?
Exploring the Market for Stolen Passwords Not long ago, PCs compromised by malware were put to a limited number of fraudulent uses, including spam, click fraud and denial-of-service attacks. These days, computer crooks are extracting and selling a much broader array of data stolen from hacked systems, including passwords and associated email credentials tied to a variety of online retailers. This shop sells credentials to active accounts at dozens of leading e-retailers. At the forefront of this trend are the botnet creation kits like Citadel, ZeuS and SpyEye, which make it simple for miscreants to assemble collections of compromised machines. Some of the most valuable data extracted from hacked PCs is bank login information. Logins for everything from Amazon.com to Walmart.com often are resold — either in bulk, or separately by retailer name — on underground crime forums. The “Freshotools” service sells a variety of hacked e-retailer credentials.
Top 10 Websites to Back Up Your Tweets As a matter of fact, all your tweets will be stored on Twitter.com, but only those posted in about 10 days are available for search, and it is hard to track the old tweets, so that to back up your tweets will be useful, especially when you are going to review your old tweets. To back up your tweets, you can check out below 10 websites, all of which will let you do that for free. 1. Google Reader Just subscribe to your Twitter RSS Feed with your Google Reader, then you can back up your tweets automatically and you can also search them easily. Go to Google Reader 2. On Twapper Keeper, you can back up any Twitter user’s public tweets just by entering its username, you can sort the results by date or the number of tweets, and you can also download the result tweets. Besides your tweets, you can also back up the tweets with any hashtags or keywords. Go to Twapper Keeper 3. Go to Twistory 4. Just log in with Twitter OAuth, then you can download your tweets as CSV files. Go to Tweetake 5. 6. 7. 8. 9.
Billion laughs In computer security, a billion laughs attack is a type of denial-of-service (DoS) attack which is aimed at parsers of XML documents.[1] It is also referred to as an XML bomb or as an exponential entity expansion attack.[2] Details[edit] While the original form of the attack was aimed specifically at XML parsers, the term may be applicable to similar subjects as well.[1] The problem was first reported as early as 2003, but began to be widely addressed in 2008.[3] Defenses against this kind of attack include capping the memory allocated in an individual parser if loss of the document is acceptable, or treating entities symbolically and expanding them lazily only when (and to the extent) their content is to be used. Code example[edit] <? When an XML parser loads this document, it sees that it includes one root element, "lolz", that contains the text "&lol9;". Variations[edit] The billion laughs attack described above takes an exponential amount of space. See also[edit] References[edit]
People Search - Free People Search Engines & People Finder. Find People Free, Locate People and Search People Free. Google A Person - Google People Finder & Google People Search. Person Search, Person Locator, Person Finder and People Searches Online. How to Launch a 65Gbps DDoS, and How to Stop One Yesterday I posted a post mortem on an outage we had Saturday. The outage was caused when we applied an overly aggressive rate limit to traffic on our network while battling a determined DDoS attacker. In the process of writing it I mentioned that we'd seen a 65Gbps DDoS earlier on Saturday. What Constitutes a Big DDoS? A 65Gbps DDoS is a big attack, easily in the top 5% of the biggest attacks we see. At CloudFlare, an attack needs to get over about 5Gbps to set off alarms with our ops team. So You Want to Launch a DDoS So how does an attacker generate 65Gbps of traffic? Botnet herders will often rent out access to their botnets, often billing in 15 minute increments (just like lawyers). To launch a 65Gbps attack, you'd need a botnet with at least 65,000 compromised machines each capable of sending 1Mbps of upstream data. Amplifying the Attacks Since renting a large botnet can be expensive and unwieldy, attackers typically look for additional ways to amplify the size of their attacks.
Image retrieval The first microcomputer-based image database retrieval system was developed at MIT, in the 1990s, by Banireddy Prasaad, Amar Gupta, Hoo-min Toong, and Stuart Madnick.[1] A 2008 survey article documented progresses after 2007.[2] Search methods[edit] Image search is a specialized data search used to find images. To search for images, a user may provide query terms such as keyword, image file/link, or click on some image, and the system will return images "similar" to the query. The similarity used for search criteria could be meta tags, color distribution in images, region/shape attributes, etc. Image meta search - search of images based on associated metadata such as keywords, text, etc.Content-based image retrieval (CBIR) – the application of computer vision to the image retrieval. Data Scope[edit] It is crucial to understand the scope and nature of image data in order to determine the complexity of image search system design. Evaluations[edit] See also[edit] References[edit]
SQL Injection Knowledge Base Default Databases Testing Injection False means the query is invalid (MySQL errors/missing content on website) True means the query is valid (content is displayed as usual) Given the query SELECT * FROM Table WHERE id = '1'; Examples: SELECT * FROM Articles WHERE id = '1'''; SELECT 1 FROM dual WHERE 1 = '1'''''''''''''UNION SELECT '2'; Notes: You can use as many apostrophes and quotations as you want as long as they pair up. Given the query SELECT * FROM Table WHERE id = 1; Example: SELECT * FROM Users WHERE id = 3-2; true is equal to 1. Given the query SELECT * FROM Table WHERE username = ''; Example: SELECT * FROM Users WHERE username = 'Mike' AND password = '' OR '' = ''; The following can be used to comment out the rest of the query after your injection: Examples: SELECT * FROM Users WHERE username = '' OR 1=1 -- -' AND password = ''; SELECT * FROM Users WHERE id = '' UNION SELECT 1, 2, 3`'; Note: The backtick can only be used to end a query when used as an alias. Testing Version /*!
Qrobe - Search Engine New Hotmail Exploit Can Get any Hotmail Email Account Hacked for just 20$ | Whitec0de.com New Hotmail Exploit Can Get any Hotmail Email Account Hacked for just 20$ A very severe bug in the Hotmail Website came to light recently. A critical vulnerability allowed anyone to remotely change the password of any Hotmail account. The exploit was first discovered by a Hacker from Saudi Arabia who is a member of the popular security forum dev-point.com. The exploit eventually spread like wild fire across the hacking community. The exploit in itself was a very simple one. Microsoft is yet to offer an official declaration of the vulnerability. But the rumour has it that there exit another critical vulnerability but it’s knowledge is limited to only the hackers who frequent the dark web. We have received many queries regarding the new 0 day exploit which is yet to be patched. Even our website came under Ddos attack on 17 april because of leaking the information to the public. Keep checking Whitec0de for more updates.
Koders.com Companies in Social Media Analysis A global reference to the hundreds of companies that offer products and services for listening to what people are saying in social media Navigating the directory The search box (above and at the top right of every entry) is your friend; the directory contains 508 listings. If you prefer to browse the company listings, visit the complete list. Tip: Search operates on the full text of company listings. About the listings Each company in the directory has its own page with the following information: A link to the company's main website The location of the company's main office A link to the company's Twitter account Links to the company's pages on LinkedIn, Facebook, Google+, and SlideShare A description of the company and its social media analysis products and services, provided by the company itself Links to recent news items on Social Media Analysis that mention the company A Twitter widget showing the company's most recent tweets Additions and updates Latest updates:
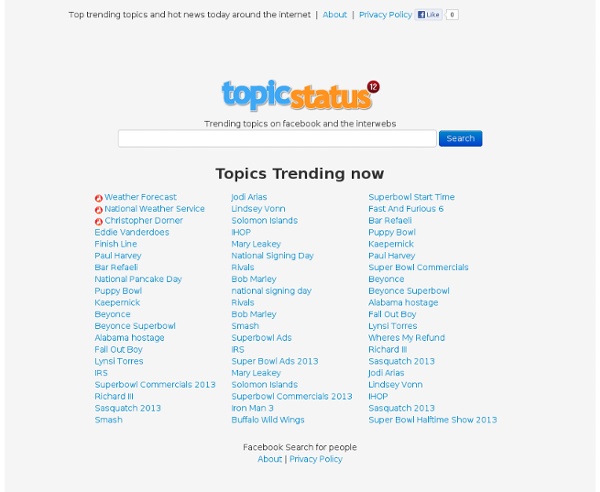
Tagline: "Facebook Search for people ", but you can search for basically any topic. Also has trending topics display. by dutchital Mar 8