NoSQL Data Modeling Techniques « Highly Scalable Blog
https://highlyscalable.wordpress.com/2012/03/01/nosql-data-modeling-techniques/
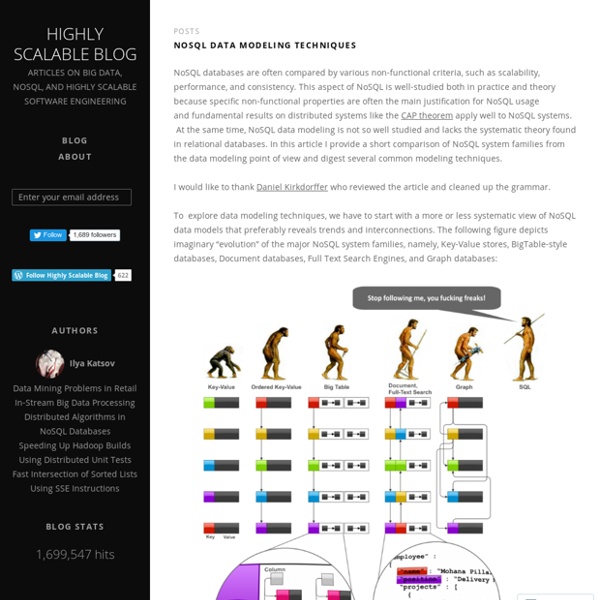
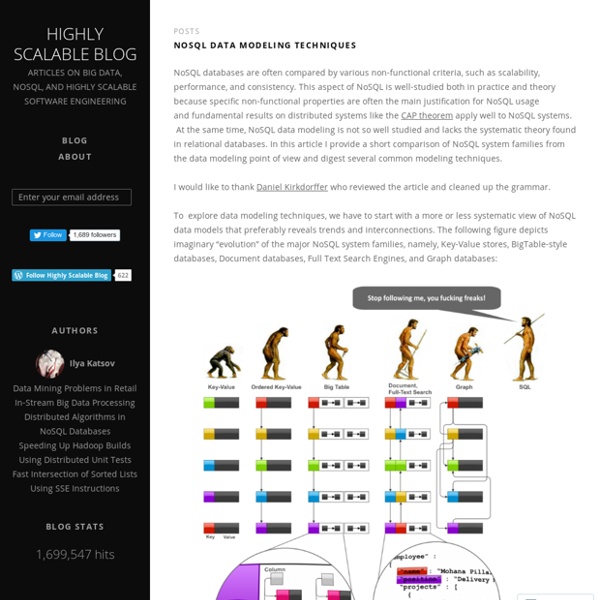
What the heck are you actually using NoSQL for?
It's a truism that we should choose the right tool for the job. Everyone says that. And who can disagree? The problem is this is not helpful advice without being able to answer more specific questions like: What jobs are the tools good at? Will they work on jobs like mine? Is it worth the risk to try something new when all my people know something else and we have a deadline to meet?
Ruby on Rails Tutorial: Learn Rails by Example book and screencasts by Michael Hartl
Michael Hartl Contents Foreword
NoSQL
"Structured storage" redirects here. For the Microsoft technology also known as structured storage, see COM Structured Storage. A NoSQL (often interpreted as Not Only SQL[1][2]) database provides a mechanism for storage and retrieval of data that is modeled in means other than the tabular relations used in relational databases.
Learn jQuery in 30 Days
Reactive programming is a way of coding with asynchronous data streams that makes a lot of problems easier to solve. RxJS is a popular library for reactive...Once in a while, it's important for us as developers to go back to what made us excited about computers in the first place. For Derek Jensen, that is gaming....React is a flexible framework that makes it easy to build single-page web applications. One of its tools is a set of lifecycle methods which you can add to...The PixelSquid plugin for Photoshop is an exciting new technology that provides the benefits of 3D elements without having to understand a 3D program or the...How your app looks is as important as how it works, and animation is an important part of modern user interfaces.
JOINs via denormalization for NoSQL coders, Part 2: Materialized views - Web development blog
Thomas Wanschik on September 27, 2010 In part 1 we discussed a workaround for JOINs on non-relational databases using denormalization in cases for which the denormalized properties of the to-one side don't change. In this post we'll show one way to handle JOINs for mutable properties of the to-one side i.e. properties of users. Let's summarize our current situation: We have users (the to-one side) and their photos (the to-many side)Photos contain their users' gender in order to use it in queries which would need JOINs otherwise
Guidelines for Modeling and Optimizing NoSQL Databases - LaunchAny
eBay Architect Jay Patel recently posted an article about data modeling using the Cassandra data store. In his article, he breaks down how they modeled their data using Cassandra, how they approached the use of Columns and Column Families, and query optimizations. The post is very detailed and a great read. What I enjoyed most from the article was more of the high-level approach that Jay and his team took. Here are my favorite takeaways from their approach to data modeling and query optimization, that I believe can be applied to any NoSQL database, including Cassandra, MongoDB, Redis, and others.
Designing a Secure REST (Web) API without OAuth
Situation You want to develop a RESTful web API for developers that is secure to use, but doesn’t require the complexity of OAuth and takes a simple “pass the credentials in the query” approach… or something equally-as-easy for people to use, but it needs to be secure. You are a smart guy, so you start to think… Problem You realize that literally passing the credentials over HTTP leaves that data open to being sniffed in plain-text; After the Gawker incident, you realize that plain-text or weakly-hashed anything is usually a bad idea. You realize that hashing the password and sending the hash over the wire in lieu of the plain-text password still gives people sniffing at least the username for the account and a hash of the password that could (in a disturbing number of cases) be looked up in a Rainbow Table.
Kyoto Cabinet: a straightforward implementation of DBM
Copyright (C) 2009-2012 FAL Labs Last Update: Fri, 04 Mar 2011 23:07:26 -0800 Overview
BIG Data Analytics Pipeline
"Big Data Analytics" has recently been one of the hottest buzzwords. It is a combination of "Big Data" and "Deep Analysis". The former is a phenomenon of Web2.0 where a lot of transaction and user activity data has been collected which can be mined for extracting useful information. The later is about using advanced mathematical/statistical technique to build models from the data.
Storing Hierarchical Data in a Database Article
Now, let’s have a look at another method for storing trees. Recursion can be slow, so we would rather not use a recursive function. We’d also like to minimize the number of database queries. Preferably, we’d have just one query for each activity. We’ll start by laying out our tree in a horizontal way. Start at the root node (‘Food’), and write a 1 to its left.
Related:
Related: