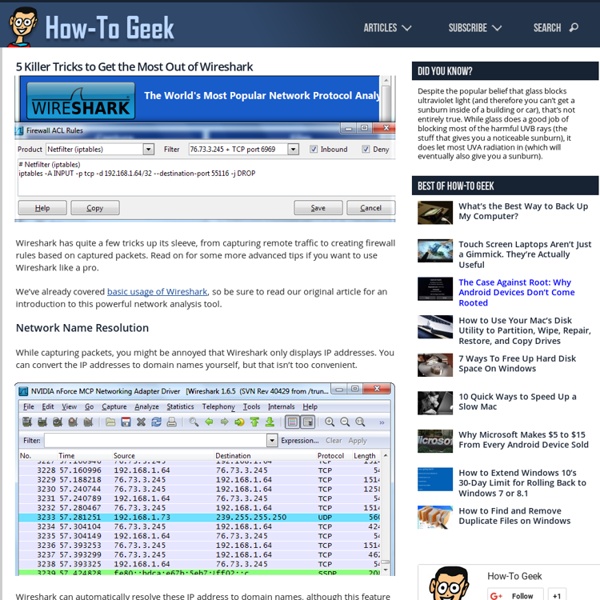
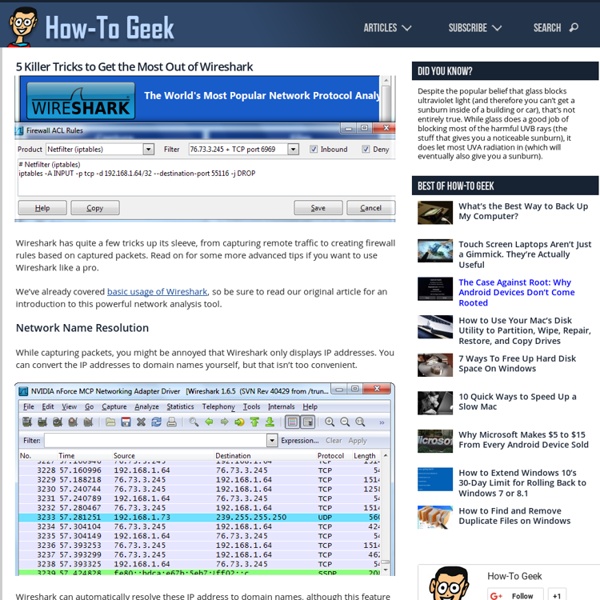
5 Killer Tricks to Get the Most Out of Wireshark
Citrix XenDesktop vs VMWare View - Virtual Desktop Resource
I was recently asked to compare XenDesktop to VMWare View. I'm always happy to handle such a request because I love comparing technology, especially Desktop Virtualization technology. Many of the articles I read online are overly biast, or approach it from one stand point. The way I approach any technology at any customer is pretty basic but a lot of tech people tend to forget this: the "right" technology is whatever technology makes sense for the customers environment. My conclusion (I'll give it to you now while you are only two paragraphs into this article) is that the reason you'll choose one solution over the other is going to come down to two factors, cost and comfort level. So lets get into it. The Hypervisor:Everything is virtualized right. Unfortunately for all of us IT guys, there are applications that we have to manage. So there you have it, those are the components.
Citrix XenDesktop 7.6, Provisioning Services 7.6 and the XenDesktop Setup Wizard with Write Cache and Personal vDisk Drives | Carl Webster
The original articles I wrote for XenDesktop 7.1 and PVS 7.1 and XenDesktop 7.5 and PVS 7.1 have proven to be extremely popular. This article will show the same process as the original articles but use XenDesktop 7.6 and PVS 7.6 and show what differences XenDesktop 7.6 and PVS 7.6 bring to the process. Introduction A while back, I worked on a project where the customer required the use of a Write Cache drive and a Personal vDisk (PvD) drive with XenDesktop 7.1 using Provisioning Services (PVS) 7.1. Getting information on the process to follow was not easy and, as usual, the Citrix documentation was sorely lacking in details. Assumptions: PVS 7.6 is installed, configured and a farm created.XenDesktop 7.6 is installed and a Site created and configured.Hosting resources are configured in Studio.PXE, TFTP and DHCP are configured as needed. This article is not about the pros and cons of PvD. Lab Setup All servers in my lab are running Microsoft Windows Server 2012 R2 fully patched. Figure 1
FREE Computer Training - Computer Repair Classes - Laptop Repair Instruction - Data Recovery Lessons - Web Design Seminars - Computer Security Counseling
Related:
Related: