


The TCP/IP Guide The TCP/IP Guide Welcome to the free online version of The TCP/IP Guide! My name is Charles and I am the author and publisher. I hope you will find the material here useful to you in your studies of computing, networking, and programming. Here are a few tips, links and reminders to help you out: Introduction: Newcomers to The TCP/IP Guide may wish to read the Introduction and Guide to the Guide, which will explain what the Guide is about and provide you with useful information about how to use it. Last but definitely not least: this site is provided as an online reference resource for casual use. If you like The TCP/IP Guide enough to want your own copy in convenient PDF format, please license the full Guide. Thanks again and enjoy the site! Charles Home - Table Of Contents - Contact Us
SELinux Un article de Wikipédia, l'encyclopédie libre. Security-Enhanced Linux, abrégé SELinux, est un Linux security module (LSM), qui permet de définir une politique de contrôle d'accès obligatoire aux éléments d'un système issu de Linux. Son architecture dissocie l'application de la politique d'accès et sa définition. Il permet notamment de classer les applications d'un système en différents groupes, avec des niveaux d'accès plus fins. Il permet aussi d'attribuer un niveau de confidentialité pour l'accès à des objets systèmes, comme des descripteurs de fichiers, selon un modèle de sécurité multiniveau (MLS pour Multi level Security). SELinux utilise le modèle Bell LaPadula complété par le mécanisme Type enforcement de contrôle de l'intégrité, développé par SCC. Historique[modifier | modifier le code] La National Security Agency (ou NSA), service de renseignement des États-Unis, avait besoin de logiciels de Multi-Level Security (MLS) pour conserver ses informations secrètes. ls -Z /etc/passwd
vizualize.me: Visualize your resume in one click. The HTML5 test - How well does your browser support HTML5? v3n0m-Scanner/Linux-v3n0m · GitHub - Vimperator Emdebian -- The Universal Embedded Operating System GuiSysLink UDF Thx ProgAndy. I knew SysLinks controls were native, and found them difficult to handle in automation. Your script not only provides a means to create these controls but may also address Autoit's main purpose, automation, which gives it an additional advantage, not to dismiss the merit of any other alternatives. Taking a closer look at MrCreator's script you are quite right, it's a label with a predefined behavior. As for the rich edit alternative, I never wrote a fully fledged UDF simultation of a SysLink, because my script(s) were basically a sub part (the About) of other scripts, and I never got round to making something of general applicability that may be re-utilized. Anyhow, ThumbsUp for this effort.
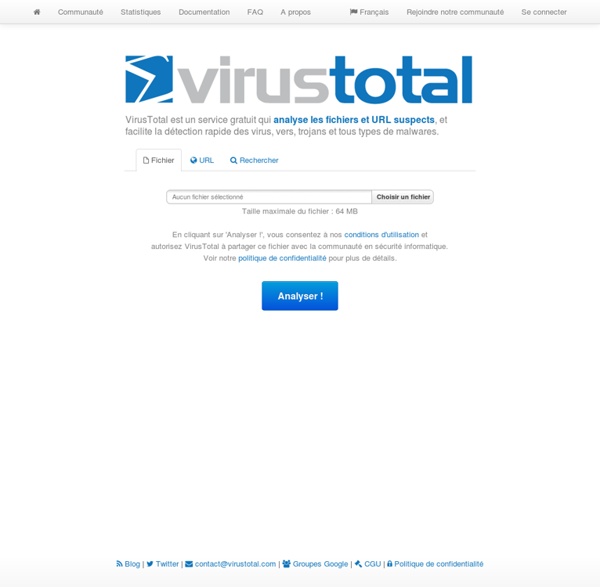
Optimiser et utiliser au mieux son SSD : Optimisations avancées 1/2 Damn Vulnerable Web App Tester la vulnérabilité de son système Secunia Personal Software Inspector (Secunia PSI) Nous venons de voir qu’il était possible de scanner en ligne son PC pour obtenir la liste des programmes non à jour et pouvant mettre en péril la sécurité de son PC. L’éditeur Secunia propose aussi un programme Secunia Personal Software Inspector qui s’installe sur son ordinateur et permet de scanner à tout moment son ordinateur afin de vérifier si les programmes sont bien à jour. Secunia Personal Software Inspector vérifie en temps réel si vos programmes sont bien à jour et peut afficher une alerte lorsqu’un programme comporte une vulnérabilité, ceci permet d’être prévenu à tout moment. Vous pouvez télécharger Secunia Personal Software Inspector depuis ce lien : Il est en anglais mais très simple d’utilisation et peut s’avérer être un outil formidable pour maintenir ses programmes à jour. Le programme se présente avec un tableau de board (DashBoard) récapitulant les informations.