


How to Hack Someones IP Address 2014 - Come to Hack Most of you may be curious to know how to find the IP address of your friend’s computer or to find the IP address of the person with whom you are chatting in Yahoo messenger or Gtalk. Finding out someone's IP address is like finding their phone number, an IP address can be used to find the general location where that person lives. Now while most of the tutorials on the net teach you how to steal an ip address via MSN, or any other chat software, in this post I’ll show you how to find IP address of someones computer using script. Using this method for hacking someones ip adress is very easy and effectively, so just follow the steps bellow. NOTE: This tutorial is for educational purposes only, I am NOT responsible in any way for how this information is used, use it at your own risk. How to Hack Someones IP Address? Alright, I'm gonna give you this script, that you write in the index.php. Here is the sript: 1. 2. 3. 4. Hope you'll find this tutorial useful. Introduction1. 4. Time to start.
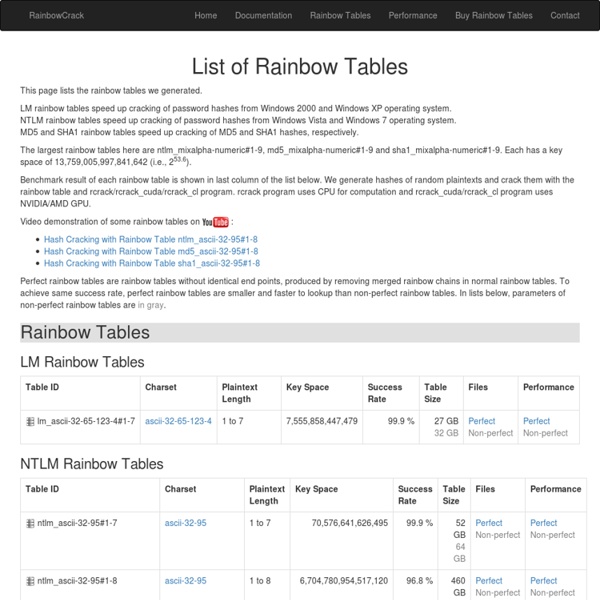
Brute Forcing Passwords and Word List Resources Brute force, even though it's gotten so fast, is still a long way away from cracking long complex passwords. That's were word lists come in handy. It's usually the crackers first go-to solution, slam a word list against the hash, if that doesn't work, try rainbow tables (if they happen to have the tables for that specific hash type), and then the full on brute force. Some would say those first two steps are reversed, and it really is the choice of the the person doing it and the word lists they have to work with. Matt Weir and company created a cool tool that has the best of both worlds, Dictionary based Rainbow Tables with Dr-Crack, which you can find here: But, back to the reason of this post, word lists. I like to keep 3 size word lists: 1. small and fast: usually based on the output of one of the tools i'm about to tell you about 2. medium: this is my custom list that I add passwords I find / crack and generally think are good to add.
The ABCs of Web Development Web development can often be an utterly perplexing affair. Today, aimed at beginners, I'd like to introduce you to twenty six concepts or technologies, each mapping to a letter of the alphabet. Sounds wonky? It probably is! Let's get started after the jump. Republished Tutorial Every few weeks, we revisit some of our reader's favorite posts from throughout the history of the site. AJAX stands for Asynchronous JavaScript And XML and is the main driving force behind all these super smooth web applications you've been using over the past few years. AJAX, as a technology, has been pretty much all pervasive. At the center of everything is the XMLHttpRequest which allows calls to be sent and received, after a page has been fully rendered without touching the rest of the page. Related reading B -- Browser A browser is the understated structure on which you frame your magnificent masterpieces, be it websites or applications. CSS is one prong of the front end development trident. E -- Events
Biometrics.gov - Introduction to Biometrics The NSTC Subcommittee on Biometrics and Identity Management developed this introductory material in order to better communicate both within the government and with other interested parties. Stating facts and discussing related issues in a consistent, understandable manner, will enable smoother integration of privacy-protective biometric solutions. Federal agencies are working to ensure that their outreach activities are consistent with, and occasionally reference, this suite of documents so that the public, press and Congress are able to easily understand their plans and discuss them productively. The Subcommittee encourages other entities to also use and reference this material. The background material here was developed in 2006. Introduction Technologies Cross-Cutting Topics Additional References
Coding An HTML 5 Layout From Scratch Understanding /etc/shadow file byVivek GiteonFebruary 23, 2006 last updated November 20, 2015 inBASH Shell, CentOS, Debian / Ubuntu, FreeBSD, HP-UX Unix, Linux, RedHat and Friends, Solaris-Unix, Suse, Ubuntu Linux, UNIX, User Management Can you explain /etc/shadow file format used under Linux or UNIX-like system? The /etc/shadow file stores actual password in encrypted format for user’s account with additional properties related to user password i.e. it stores secure user account information. All fields are separated by a colon (:) symbol. /etc/shadow file fields (Fig.01: /etc/shadow file fields) Username : It is your login name.Password : It is your encrypted password. The last 6 fields provides password aging and account lockout features. How do I change the password? Use the following syntax to change your own password: $ passwd How do I change the password for other users? You must be root to change the password for all other users: # passwd userNameHere OR $ sudo passwd userNameHere How do I setup password again?
30 Useful Responsive Web Design Tutorials So we’ve reached the end of our “Responsive Web Design week”, tonight’s post will be the last of the series. We are going all out to help you hone your skills in manipulating those codes to respond at will when displayed on different devices. And to do this, we are featuring 30 Responsive Web Design Tutorials found online. This list is not meant to be an exhaustive one but it will get you started on understanding the basics of designing an adaptive website that will cater to all sorts of screen sizes. We’ll start off with introductory tutorials in ‘Breaking the Ice’, something like an RWD: 101 class you should attend to get the hang of the concept before we move on to ‘Start Building’ exercises. Lastly we’ll end with a ‘Do More’ section in which we’ll feature tutorials that play with horizontal layouts, ‘elastic’ videos, drop-down menus and slide-to-top accordion navigations, thumbnails and the sticky issue with tables. But first… Responsive website Navigation Responsive Resume Fluid Grids
How I Cracked your Windows Password (Part 2) If you would like to read the first part in this article series please go to How I Cracked your Windows Password (Part 1). Introduction In the first part of this series we examined password hashes and the mechanisms Windows utilizes to create and store those values. We also touched upon the weaknesses of each method and possible avenues that can be used to crack those passwords. It is always crucial to note that the techniques shown here are strictly for educational purposes and should not be used against systems for which you do not have authorization for. Obtaining Password Hashes In order to crack passwords you must first obtain the hashes stored within the operating system. There are a few different options here depending on the level of access you have to the machine you are auditing. Physical Access If you have physical access, one of the most effective methods is to boot the computer into a different operating system. If you are not quite comfortable doing this, you can use P.
Welcome [Savannah] How I Cracked your Windows Password (Part 1) AdvertisementGFI LanGuard your virtual security consultant. Scan your LAN for any vulnerability and automate patch management for Windows, Mac OS & Linux. Get your FREE trial now! How Windows creates and stores password hashes and how those hashes are cracked. If you would like to read the next part in this article series please go to How I Cracked your Windows Password (Part 2). Introduction Passwords tend to be our main and sometimes only line of defense against intruders. The purpose of this article is to educate you on how Windows creates and stores password hashes, and how those hashes are cracked. How Windows Stores Passwords Windows-based computers utilize two methods for the hashing of user passwords, both having drastically different security implications. LM Password Hashes The LM hash of a password is computed using a six-step process: In practice, the password “PassWord123” would be converted as follows: Figure 1: A password transformed into an LM hash NTLM Password Hashes Conclusion
oxid.it - Home John the Ripper password cracker John the Ripper is free and Open Source software, distributed primarily in source code form. If you would rather use a commercial product tailored for your specific operating system, please consider John the Ripper Pro, which is distributed primarily in the form of "native" packages for the target operating systems and in general is meant to be easier to install and use while delivering optimal performance. This version integrates lots of contributed patches adding GPU support (OpenCL and CUDA), support for a hundred of additional hash and cipher types (including popular ones such as NTLM, raw MD5, etc., and even things such as encrypted OpenSSH private keys, ZIP and RAR archives, PDF files, etc.), as well as some optimizations and features. Unfortunately, its overall quality is lower than the official version's. Requires OpenSSL. To verify authenticity and integrity of your John the Ripper downloads, please use our PGP public key. Contributed resources for John the Ripper: