


John the Ripper password cracker John the Ripper is free and Open Source software, distributed primarily in source code form. If you would rather use a commercial product tailored for your specific operating system, please consider John the Ripper Pro, which is distributed primarily in the form of "native" packages for the target operating systems and in general is meant to be easier to install and use while delivering optimal performance. This version integrates lots of contributed patches adding GPU support (OpenCL and CUDA), support for a hundred of additional hash and cipher types (including popular ones such as NTLM, raw MD5, etc., and even things such as encrypted OpenSSH private keys, ZIP and RAR archives, PDF files, etc.), as well as some optimizations and features. To verify authenticity and integrity of your John the Ripper downloads, please use our PGP public key. You may browse the documentation for John the Ripper online, including a summary of changes between versions.
Open Port Check Tool Nessus From the beginning, we've worked hand-in-hand with the security community. We continuously optimize Nessus based on community feedback to make it the most accurate and comprehensive vulnerability assessment solution in the market. 20 years later and we're still laser focused on community collaboration and product innovation to provide the most accurate and complete vulnerability data - so you don't miss critical issues which could put your organization at risk. Today, Nessus is trusted by more than 27,000 organizations worldwide as one of the most widely deployed security technologies on the planet - and the gold standard for vulnerability assessment. See for yourself - explore the product here. 1 in Accuracy Nessus has the industry's lowest false positive rate with six-sigma accuracy. 1 in Coverage Nessus has the deepest and broadest vulnerability coverage in the industry. 100+ new plugins released weekly 1 in Adoption 1 in Hearts and Minds Don't just take our word for it.
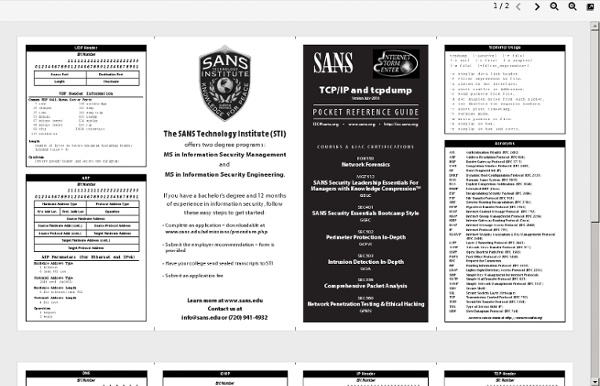
FreeSWITCH | Communication Consolidation Packet Life