


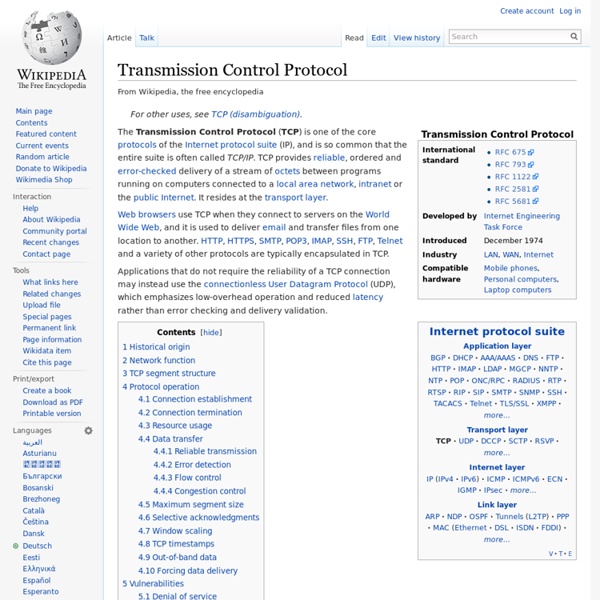
Internet Protocol This article is about the IP network protocol only. For Internet architecture or other protocols, see Internet protocol suite. The Internet Protocol (IP) is the principal communications protocol in the Internet protocol suite for relaying datagrams across network boundaries. Its routing function enables internetworking, and essentially establishes the Internet. Historically, IP was the connectionless datagram service in the original Transmission Control Program introduced by Vint Cerf and Bob Kahn in 1974; the other being the connection-oriented Transmission Control Protocol (TCP). The Internet protocol suite is therefore often referred to as TCP/IP. The first major version of IP, Internet Protocol Version 4 (IPv4), is the dominant protocol of the Internet. Function[edit] The Internet Protocol is responsible for addressing hosts and for routing datagrams (packets) from a source host to a destination host across one or more IP networks. Datagram construction[edit] Reliability[edit]
Daily | Mises Institute Libertarians often cite the internet as a case in point that liberty is the mother of innovation. Opponents quickly counter that the internet was a government program, proving once again that markets must be guided by the steady hand of the state. In one sense the critics are correct, though not in ways they understand. The internet indeed began as a typical government program, the ARPANET, designed to share mainframe computing power and to establish a secure military communications network. Of course the designers could not have foreseen what the (commercial) internet has become. In fact, the role of the government in the creation of the internet is often understated. The internet owes its very existence to the state and to state funding. During the 1960s, the RAND Corporation had begun to think about how to design a military communications network that would be invulnerable to a nuclear attack. By 1972, the number of host computers connected to the ARPANET had increased to 37.
Did Al Gore Claim He Invented the Internet? Claim: Vice-President Al Gore claimed during a news interview that he "invented" the Internet. Origins: Despite the derisive references that continue even today, former Vice-President Al Gore never claimed that he "invented" the Internet, nor did he say anything that could reasonably be interpreted that way. The "Al Gore said he 'invented' the Internet" put-downs were misleading, out-of-context distortions of something he said during an interview with Wolf Blitzer on CNN's "Late Edition" program on 1999. When asked to describe what distinguished him from his challenger for the Democratic presidential nomination, Senator Bill Bradley of New Jersey, Gore replied (in part): During my service in the United States Congress, I took the initiative in creating the Internet. Al Gore was the first political leader to recognize the importance of the Internet and to promote and support its development. No one person or even small group of persons exclusively "invented" the Internet.
How Government Did (and Didn't) Invent the Internet Last night, I happened across an article by Slate technology scribe Farhad Manjoo. He was responding to an opinion piece in the Wall Street Journal by the Journal’s former publisher Gordon Crovitz. And when Manjoo explained just what Crovitz was opining about, I felt my jaw drop to the floor as if I were a character in a 1940s cartoon. Crovitz, apparently riled up over Barack Obama’s “you didn’t build that” kerfuffle, has an example of something that the government is widely misperceived to have built: the Internet. He actually says, “It’s an urban legend that the government launched the Internet.” As Manjoo points out, Crovitz’s argument — which rests largely on his contention that the Internet was really created at Xerox’s legendary PARC lab — is bizarrely, definitively false. Also factual: DARPA was where Robert Kahn and Vint Cerf invented TCP/IP, the plumbing that makes the Internet possible. (Crovitz, incidentally, credits Berners-Lee for the hyperlink.
Microsoft Grabs No-IP Websites Neutralité : le CSA milite pour utilisation préférentielle de la bande passante Le CSA, pour pousser les acteurs de type Netflix à investir en France, compte agiter une carotte de taille : avantager ceux qui se plieront à ses règles. Parmi les avantages, une bande passante plus importante sera notamment proposée. Une mise à mal de la neutralité du Net dont est bien conscient Olivier Schrameck, le président du Conseil Supérieur de l'Audiovisuel. Olivier Schrameck « Mais encore faut-il que le conventionnement soit suffisamment attractif » Lors de son audition devant la Commission des affaires européennes de l’Assemblée nationale la semaine dernière, Olivier Schrameck, président du CSA, a notamment abordé la question polémique de la mise à mal de la neutralité du Net. « Notre idée, c'est qu'un certain nombre d'acteurs, extra-Européens ou même Européens qui ne soient pas Français, sont susceptibles de s'engager dans un mécanisme de conventionnement. « Une utilisation préférentielle d'une partie de la bande passante »
Comment l’État a participé à la création de l’internet Par Steve Fritzinger, depuis les États-Unis. Dans son désormais célèbre discours « You didn’t build that » [Vous n’avez pas construit ça, NDT], le président Obama a dit : « L’internet n’a pas été inventé tout seul. La recherche d’État a créé l’internet pour que toutes les entreprises puissent gagner de l’argent avec l’internet ». L’affirmation d’Obama correspond à l’histoire conventionnelle de l’internet. Comme tout bon mythe fondateur, cette histoire contient une part de vérité. L’idée d’une interconnexion de réseaux [internetworking, NDT] a été proposée pour la première fois au début des années 60 par le chercheur en informatique J. Dans une publication scientifique datée de 1962, Licklider a décrit un « réseau de réseaux » qu’il a appelé « réseau intergalactique d’ordinateurs ». Licklider a amené avec lui l’idée d’une interconnexion de réseaux lorsqu’il a rejoint l’ARPA en 1962. En 1968, l’ARPA a financé le premier réseau à paquets commutés à quatre nœuds. I, Internet
40 maps that explain the internet The internet increasingly pervades our lives, delivering information to us no matter where we are. It takes a complex system of cables, servers, towers, and other infrastructure, developed over decades, to allow us to stay in touch with our friends and family so effortlessly. Here are 40 maps that will help you better understand the internet — where it came from, how it works, and how it's used by people around the world. How the internet was created Before the internet, there was the ARPANET Before the internet, there was the ARPANETARPANET, the precursor to the modern internet, was an academic research project funded by the Advanced Research Projects Agency, a branch of the military known for funding ambitious research projects without immediate commercial or military applications. Initially, the network only connected the University of Utah with three research centers in California. The internet around the world Threats to the internet The geography of online services Twerking vs.
Quand l’État vous disait qu’Internet n’avait aucun avenir Mon attention a été attirée sur le rapport Thery de 1994. Intitulé « Les autoroutes de l’information », il fut écrit par Gérard Théry, Alain Bonnafé, Michel Guieysse et adressé au Premier ministre de l’époque, Édouard Balladur. La lecture de ce rapport, presque 20 ans après, est fort instructive Elle révèle comment trois technocrates français parmi les plus compétents (Théry est polytechnicien et ingénieur des télécoms) voyaient l’avenir des autoroutes de l’information et le rôle que l’internet allait y jouer. En substance, l’existence de ce dernier est reconnue, mais il est rapidement écarté. On lit en effet : « Son mode de fonctionnement coopératif n’est pas conçu pour offrir des services commerciaux. Sans rire. La question qu’il faut se poser est donc celle de savoir pourquoi des gens intelligents commettent de pareilles bévues. Mais dans ce cas, il eût mieux valu se taire. 1ère erreur : l’extrapolation Ne riez pas : les prédicateurs font cela tous les jours. —Sur le web
Qui a vraiment créé Internet ? Par le Minarchiste, depuis Montréal, Québec. Le gouvernement est-il responsable de la création d’Internet ? Pour plusieurs, sans interventionnisme gouvernemental, l’internet n’aurait pas vu le jour. « During my service in the United States Congress, I took the initiative in creating the Internet. », Al Gore, 1999 (voir ceci). En fait, comme plusieurs autres technologies, Internet a d’abord été un projet du département de la défense et son objectif n’était pas commercial, ni social. « A network of such [computers], connected to one another by wide-band communication lines [which provided] the functions of present-day libraries together with anticipated advances in information storage and retrieval and [other] symbiotic functions. » Ce rapport contenait tous les éléments composant l’internet moderne. En 1989, ARPANET fut mis hors service, car il était devenu inutile. Conclusion : Lectures complémentaires : —Sur le web