


Nétiquette | ARTV Les plateformes sociales d’ICI ARTV ne sont pas anonymes. Les utilisateurs sont tenus, à l'inscription, d'indiquer leurs prénom et nom. Les propos diffamatoires, haineux, racistes, xénophobes, homophobes, sexistes ou disgracieux ne seront pas publiés. Les plateformes sociales d’ICI ARTV sont ouvertes aux personnes de tous âges, races, religions, sexes, origines ethniques et orientations sexuelles. Les échanges se déroulent en français. Les majuscules équivalent aux cris et peuvent être interprétées comme de l'agressivité. Le langage vulgaire, obscène ou malveillant est interdit. Le respect mutuel est de mise entre les utilisateurs. Les messages sans rapport avec le sujet ne seront pas publiés. Les échanges ne doivent pas prendre la forme d'une discussion privée entre deux participants sans égard aux autres. L'inclusion d'hyperliens vers d'autres sites est permise, s'ils respectent la nétiquette. L'usurpation de l'identité d'autrui est une infraction grave qui ne sera pas tolérée.
Netiquette.fr - Les règles de la Netiquette Nétiquette sur Internet / Web Charte ou règlements du forum Lis la charte (règlements) du forum ou de la liste de diffusion pour savoir ce qui est permis et interdit. Sont interdits dans les forums, les listes de diffusion (cette liste n'est pas exhaustive) : les messages publicitaires ou commerciaux; les messages à caractère politique ou religieux (sauf dans les sites portant sur ces thèmes); la reproduction ou rediffusion d'une oeuvre soumises aux droits d'auteur; les messages portant atteinte à la vie privée d'une personne ou d'un groupe de personnes; les messages dénonçant les pratiques d'une entreprise ou d'un organisme en indiquant son nom; les messages injurieux, diffamatoires, menaçants; les messages à caractère raciste ou homophobe; les photos à caractère dégradant ajoutés à un message; les messages répétitifs (flooding) visant à encombrer un site.
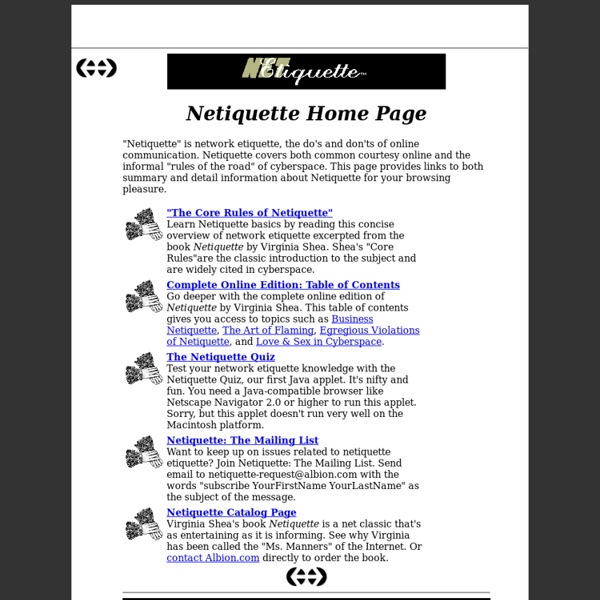
Nétiquette La nétiquette est un ensemble de dispositions informelles, souvent regroupées en charte, qui définit les règles de conduite et de politesse recommandées sur les premiers médias de communication mis à disposition par Internet. Il s'agit de tentatives de formalisation d'un certain contrat social pour Internet. Le principe de la nétiquette pourrait être résumé ainsi : « Ce que vous ne feriez pas lors d’une conversation réelle face à votre correspondant, ne prenez pas l'Internet comme bouclier pour le faire ». À ces notions de courtoisie et de respect, s'ajoutent des règles supplémentaires relatives aux spécificités de plusieurs médias. Histoire[modifier | modifier le code] Le premier document définissant les règles de la nétiquette est la RFC 1855[1], rédigée par Sally Hambridge, une employée d'Intel, pour l'Internet Engineering Task Force, et diffusée en octobre 1995. Principes généraux[modifier | modifier le code] Courtoisie[modifier | modifier le code] Signature[modifier | modifier le code]