

Tech-r03-sdn-security-v3. SDN Security Attack Vectors and SDN Hardening. As enterprises look to adopt Software Defined Networking (SDN), the top of mind issue is the concern for security.
Enterprises want to know how SDN products will assure them that their applications, data and infrastructure will not be vulnerable. With the introduction of SDN, new strategies for securing the control plane traffic are needed. This article will review the attack vectors of SDN systems and share ways to secure the SDN-enabled virtualized network infrastructure. This article will then discuss the methods currently being considered to secure SDN deployments. 1. Securing The Software-Defined Network. SDNs offer the ability to centralize and automate network security functions, but only if security requirements are implemented correctly from the ground up.

Learn how to secure the many components of the SDN. With the emergence of software-defined networks (SDNs), security must become a core component of the network. Network security can no longer be an afterthought, or added with the assumption that it will "just work" on top of an existing network. With SDN, security services are pre-planned and become the foundation for connectivity. The benefits are centralized policy management, automated provisioning, and real-time mitigation. The problem is the security perks you get from SDN are only as good as what you build into the system from the start. Integrating Security And SDN Regardless of the architectural model or the controller-agent communication protocol you choose, SDNs provide perimeter security to an organization.
Is SDN your next security nightmare? San Francisco -- The big buzzword in networking these days is Software-Defined Networking (SDN), a de-coupling of the data plane and the control plane that allows you to manage physical devices via a software-based controller sitting on a general purpose server.

There are numerous benefits associated with SDN. Instead of having to touch every switch and router, the controller enforces policies by using the OpenFlow standard to talk to the physical networking devices. Also, customers can theoretically use any OpenFlow enabled hardware, meaning you no longer have to buy all of your networking gear from the same vendor. But before you jump into SDN, be aware that there might be some security risks. That’s the view of Robert Hinden, an industry veteran and Check Point Fellow, who spoke this week at the RSA Conference. + ALSO ON NETWORK WORLD Hot, new products at RSA | A running list of stories from RSA + Also, what happens when outages or bugs occur in the network? Beware SDN Security Risks, Experts Warn. Software-defined networking is taking the industry by storm, but presents new security challenges, according to security specialists.

Though it remains in early stages in terms of adoption, software-defined networking (SDN) dominates conversations in the networking industry. But one subject missing from much of the talk is security. "There's a lot of hype, and I think that some of the issues...like security are not as well-cooked as other things," Robert Hinden, a Check Point Fellow at Check Point Software Technologies, told Network Computing.
Hinden, who's giving a presentation on SDN security at the upcoming RSA Conference in San Francisco, said that while there are a number of benefits to software-defined networking, there are also several issues that need to be solved. The whole notion of a central controller requires that IT trusts what the controller is doing and pays close attention to whether it can be compromised, he said. Are SDN Controllers a Security Risk ? Le marché du SDN estimé à 3,52 milliards dollars en 2018. Virtualisation du réseau : l'adoption du SDN prendra du temps. Les grands du réseau – Brocade, Cisco, Dell, HP, Juniper, VMware… – s’y sont mis, après avoir laissé le terrain aux rares start-up qui s’y risquent (Nicira, acquise par VMware, Adara, Embrane, etc.) et semblent vouloir avancer à grands pas.

Après le serveur et le stockage, le réseau est la prochaine cible de la virtualisation du datacenter. Sb-security-data-center.pdf. Dossier SDN : la virtualisation réseau pour les datacenters. Les Guides Essentiels Ce Guide Essentiel est un ensemble d’articles, vidéos et autres documents sélectionnés par nos rédacteurs pour vous donner une perspective complète de ce sujet.

Gartner : le SDN est un paradis pour hackers. Jérémy D'Hoinne, Gartner : « sur le SDN, la sécurité n’est pas prête » An introduction to Zero Trust virtualization-centric security. This post will be the first in a series that examine what I think are some of the powerful security capabilities of the VMware NSX platform and the implications to the data center network architecture.
In this post we’ll look at the concepts of Zero Trust (as opposed to Trust Zones), and virtualization-centric grouping (as opposed to network-centric grouping). Note: Zero Trust as a guiding principle to enterprise wide security is inspired by Forrester’s “Zero Trust Network Architecture“. What are we trying to accomplish? We want to be able to secure all traffic in the data center without compromise to performance (user experience) or introducing unmanageable complexity. Trust Zones of Insecurity Until now, it hasn’t been possible (much less economically feasible or even practical) to directly connect every virtual machine to its own port on a firewall. Under the Hood: Network Virtualization with OpenStack Neutron and VMware NSX. The Cisco Application Policy Infrastructure Controller. Introduction: What Is the Cisco Application Policy Infrastructure Controller?
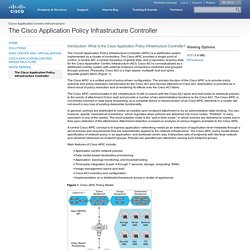
The Cisco® Application Policy Infrastructure Controller (APIC) is a distributed system implemented as a cluster of controllers. The Cisco APIC provides a single point of control, a central API, a central repository of global data, and a repository of policy data for the Cisco Application Centric Infrastructure (ACI). Cisco ACI is conceptualized as a distributed overlay system with external endpoint connections controlled and grouped through policies. Physically, Cisco ACI is a high-speed, multipath leaf and spine (bipartite graph) fabric (Figure 1).
The Cisco APIC is a unified point of policy-driven configuration. The Cisco APIC communicates in the infrastructure VLAN (in-band) with the Cisco ACI spine and leaf nodes to distribute policies to the points of attachment (Cisco leaf) and provide a number of key administrative functions to the Cisco ACI. Next Generation Networking Panel With Brad Hedlund – Cisco ACI vs. VMware NSX — Define The Cloud. Define The Cloud Cloud Computing and Data Center Technology You are here: Home / Uncategorized / Next Generation Networking Panel With Brad Hedlund – Cisco ACI vs.

VMware NSX. Et si les réseaux virtualisés (SDN/NFV) étaient la meilleure réponse aux problématiques de sécurité. Avec des attaques de plus en plus difficilement détectables avec les attaques à signature faible et l'émergence de failles généralisées comme « Heartbleed » ou les révélations de Snowden, la sécurité doit être repensée.

Software-Defined Data Center : votre infrastructure est-elle prête ? Dossier : comprendre le SDN, ou l'art de virtualiser le réseau. Depuis 2010, le Cloud change de visage avec l'arrivée de mécanismes d'automatisation de gestion des serveurs et du stockage, ainsi que de l'autoconfiguration du réseau. Dans les grands clouds publics, privés ou hybrides, ces tâches deviennent impossibles manuellement, surtout dans un contexte de concurrence où l'adaptation instantanée aux besoins des clients devient primordiale. A l'origine, les deux initiatives n'avaient rien en commun. D'un côté, le projet OpenStack, lancé en 2010, par la fondation Openstack, pour créer et offrir des services dynamiques dans le monde du Cloud Computing. NSX, la virtualisation du réseau pèse 100 millions de dollars. Software-Defined Networking (SDN) & Network Virtualization. As with server virtualization before it, network virtualization is a transformative architecture from VMware that overcomes previous limitations to deliver unprecedented performance, flexibility and economics.
In contrast to software-defined networking (SDN), in which hardware remains the driving force, VMware technology truly decouples network resources from underlying hardware. Virtualization principles are applied to physical network infrastructure, abstracting network services to create a flexible pool of transport capacity that can be allocated, utilized and repurposed on demand. In a close analogy to the virtual machine, a virtual network is a software container that presents logical network components—logical switches, routers, firewalls, load balancers, VPNs and more—to connected workloads. These virtual networks are programmatically created, provisioned and managed, with the underlying physical network serving as a simple packet-forwarding backplane. Le SDN, c'est quoi ? SDN : La révolution réseau est en marche ! Qu'est-ce que la virtualisation réseau dans l'IaaS ? Destiny To The Cloud: Is VMware's NSX a SDN, NFV or NV? Next week is VMworld 2014.
Two weeks ago, there was already a lot of traffic on the internet about this event. People are waiting to see what new product VMware is going to introduce and how these product can help solve their business or technical problem at work. NSX Compendium - Network Inferno. By Anthony Burke – VMware NSBU System Engineer. Disclaimer: This is not an official reference and should be treated as such. Any mistakes on this page are a reflection on my writing and knowledge not the product itself. I endeavour for technical accuracy but we are only human! These are to serve as a formalisation of my own notes about NSX for vSphere. Everything discussed on this page is currently shipping within the NSX product. Introduction This page serves to be a resource for the components and deployment of VMware’s NSX for vSphere . VMware NSX delivers a software based solution that solves many of the challenges faced in the data centre today.