

How the U.S. Government Hacks the World. Obscured by trees and grassy berms, the campus of the National Security Agency sits 15 miles north of Washington’s traffic-clogged Beltway, its 6 million square feet of blast-resistant buildings punctuated by clusters of satellite dishes.
Created in 1952 to intercept radio and other electronic transmissions—known as signals intelligence—the NSA now focuses much of its espionage resources on stealing what spies euphemistically call “electronic data at rest.” These are the secrets that lay inside the computer networks and hard drives of terrorists, rogue nations, and even nominally friendly governments. When President Obama receives his daily intelligence briefing, most of the information comes from government cyberspies, says Mike McConnell, director of national intelligence under President George W. Bush. Obama signs secret directive to help thwart cyberattacks.
The new directive is the most extensive White House effort to date to wrestle with what constitutes an “offensive” and a “defensive” action in the rapidly evolving world of cyberwar and cyberterrorism, where an attack can be launched in milliseconds by unknown assailants utilizing a circuitous route.

For the first time, the directive explicitly makes a distinction between network defense and cyber-operations to guide officials charged with making often-rapid decisions when confronted with threats. The policy also lays out a process to vet any operations outside government and defense networks and ensure that U.S. citizens’ and foreign allies’ data and privacy are protected and international laws of war are followed. 10K Reasons to Worry About Critical Infrastructure. Screenshot showing an industrial control system in Idaho that's connected to the internet.
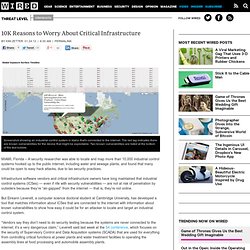
The red tag indicates there are known vulnerabilities for the device that might be exploitable. Two known vulnerabilities are listed at the bottom of the text bubble. MIAMI, Florida – A security researcher was able to locate and map more than 10,000 industrial control systems hooked up to the public internet, including water and sewage plants, and found that many could be open to easy hack attacks, due to lax security practices. Infrastructure software vendors and critical infrastructure owners have long maintained that industrial control systems (ICSes) — even if rife with security vulnerabilities — are not at risk of penetration by outsiders because they’re “air-gapped” from the internet — that is, they’re not online.
“Vendors expect systems to be on segregated networks — they comfort themselves with this. ManTech Awarded $9.2 Million Contract to Provide Cyber Security Services to the Federal Bureau of Investigation. Fuck FBI Friday III: ManTech. University projects to secure cyberspace could soon bear fruit. University projects to secure cyberspace could soon bear fruit Five-year program funded by Northrop Grumman researching new technologies By William JacksonJun 01, 2011 A number of university cybersecurity research programs funded by Northrop Grumman are expected to begin paying off in new technologies soon, researchers said June 1.

NSA is looking for a few good hackers. For that reason an alphabet soup of federal agencies — DOD, DHS, NASA, NSA — are descending on Las Vegas this week for Defcon, an annual hacker convention where the $150 entrance fee is cash only — no registration, no credit cards, no names taken.

Attendance is expected to top 10,000. The NSA is among the keen suitors. The spy agency plays offense and defense in the cyberwars. It conducts electronic eavesdropping on adversaries, and it protects U.S. computer networks that hold super-secret material — a prime target for America’s enemies. Fake femme fatale shows social network risks. News July 22, 2010 06:00 AM ET Computerworld - Hundreds of people in the information security, military and intelligence fields recently found themselves with egg on their faces after sharing personal information with a fictitious Navy cyberthreat analyst named "Robin Sage," whose profile on prominent social networking sites was created by a security researcher to illustrate the risks of social networking.

In a conversation with Computerworld, Thomas Ryan, co-founder of Provide Security, said he used a few photos to portray the fictional Sage on Facebook, LinkedIn and Twitter as an attractive, somewhat flirty cybergeek, with degrees from MIT and a prestigious prep school in New Hampshire. Then he established connections with some 300 men and women from the U.S. military, intelligence agencies, information security companies and government contractors.
Pentagon, LulzSec, News of The World ... we live in interesting times for hacking. The hacking stories just keep on coming.

Of course, The News of the World is the big one at the moment, matched, for the moment at least, by the hacking of The Sun’s website by celebrity – and proficient – hacking group LulzSec. Other interesting stories on hacking exploits keep cropping up, but are perhaps not getting the same high-profile coverage. One well worth having a look at is the fact a Pentagon supplier recently lost 24,000 files to a foreign intelligence service. Cyber war focus drives attacks on privacy and funding of contractors. When it comes to cyber defence, assessing the risk of online warfare, or even of a “cyber Pearl Harbor”, as opposed to common-or-garden crime or espionage, is made more difficult by the lack of detail around cyber attacks and the conflation of unrelated attacks.

The revelations this week about “Operation Shady RAT”, the multi-year Chinese effort to spy on a host of foreign governments and corporations, plainly related to regulated security and commercial espionage. That is, it was a continuation of ordinary spying activities — particularly by China, where impressive levels of education don’t seem to have yet produced a strong culture of technological innovation — online, rather than a peculiarly online form of attack, and certainly not any “cyber war”.
Pentagon wants to change strategy for dealing with cyber-attacks. The Comprehensive National Cybersecurity Initiative. President Obama has identified cybersecurity as one of the most serious economic and national security challenges we face as a nation, but one that we as a government or as a country are not adequately prepared to counter.

Shortly after taking office, the President therefore ordered a thorough review of federal efforts to defend the U.S. information and communications infrastructure and the development of a comprehensive approach to securing America’s digital infrastructure. In May 2009, the President accepted the recommendations of the resulting Cyberspace Policy Review, including the selection of an Executive Branch Cybersecurity Coordinator who will have regular access to the President. The activities under way to implement the recommendations of the Cyberspace Policy Review build on the Comprehensive National Cybersecurity Initiative (CNCI) launched by President George W.
CNCI Initiative Details Initiative #1. Initiative #2. Pentagon doesn't rule out military force against cyberattacks. The Pentagon's cyber attack policy "All appropriate options would be on the table"Identifying attacker can be hard, take a long time2008 incident was wake-up call.

Pentagon: Online Cyber Attacks Can Count as Acts of War. The last line of cyber defense. According to the Wall Street Journal, DoD’s first formal cyber strategy is based on the doctrine that a cyber attack on US critical infrastructure can be retaliated by a conventional military strike. The article is decorated with macho statements from unidentified military officials, such as “if you shut down our power grid, maybe we will put a missile down one of your smokestacks.” The military person who said that may have had full confidence in how deterring and frightening his or her line would be to wannabe attackers, and yet could not be more off the mark. Here is what everybody can read from DoD’s cyber strategy, given that the WSJ’s report is authentic (which I don’t call in question):
Cyberwar heats up with Pentagon's virtual firing range. The National Cyber Range marks a rise in the temperature of the online battlefield. Commentary: The Patriot Act, cyber-edition - Sacramento Living - Sacramento Food and Wine, Home, Health. Cyberwar Doomsayer Lands $34 Million in Government Cyberwar Contracts. Last month, the former Director of National Intelligence Michael McConnell boldly took to the Senate floor and the Washington Post‘s editorial page to declare “The United States is fighting a cyber-war today, and we are losing.” Thankfully for the American people, his company — the giant defense contractor Booz Allen Hamilton — has now landed the contract to build the Pentagon’s cyberwar control center. White House Cyber Czar: ‘There Is No Cyberwar’ Howard Schmidt, the new cybersecurity czar for the Obama administration, has a short answer for the drumbeat of rhetoric claiming the United States is caught up in a cyberwar that it is losing.
“There is no cyberwar,” Schmidt told Wired.com in a sit-down interview Wednesday at the RSA Security Conference in San Francisco. “I think that is a terrible metaphor and I think that is a terrible concept,” Schmidt said. “There are no winners in that environment.” Instead, Schmidt said the government needs to focus its cybersecurity efforts to fight online crime and espionage. Mike McConnell on how to win the cyber-war we're losing - washingtonpost.com. The United States is fighting a cyber-war today, and we are losing. Pentagon wastes time defining cyberwar rather than trying to fight the one it's already in.
August 15, 2011, 3:49 PM — The U.S. military command has decided the online world is the fifth domain in which to conduct warfare – in addition to land, sea air, land and space. U.S. Cyber Command: 404 Error, Mission Not (Yet) Found. Earlier this week, Defense Secretary Robert Gates ordered the military to start setting up a new “U.S. Ex-U.S. general urges frank talk on cyber weapons. WASHINGTON (Reuters) - The United States should be more open about its development of offensive cyber weapons and spell out when it will use them as it grapples with an increasing barrage of attacks by foreign hackers, the former No. 2 uniformed officer in the U.S. military said. Cyber ShockWave Shows U.S. Unprepared For Cyber Threats. Washington, D.C. - The Bipartisan Policy Center (BPC) hosted Cyber ShockWave, a simulated cyber attack on the United States, yesterday in Washington D.C. providing an unprecedented look at how the government would develop a real-time response to a large-scale cyber crisis affecting much of the nation.
CNN will air the event exclusively as “We Were Warned: Cyber Shockwave” on Saturday, February 20 and Sunday, February 21 at 8:00pm, 11:00pm and 2:00am ET each night. Cyber ShockWave highlighted the immediate, real dangers of cyber-terrorism by bringing together a bipartisan group of former senior administration and national security officials playing the roles of Cabinet members. Kissinger, Huntsman: U.S., China need cyber detente.
Special report: Government in cyber fight but can't keep up. Cyber threats to spur defense innovation: Huntsman. Analysis: Could a cyber war turn into a real one for U.S.? Revealed: Air Force ordered software to manage army of fake virtual people. FinFisher - IT Intrusion lets Government Agents Steal ALL your info - Lawmen. Exclusive: Military’s ‘persona’ software cost millions, used for ‘classified social media activities’ Metaphor is the new weapon in the 'war' on terror. So, Why Does the Air Force Want Hundreds of Fake Online Identities on Social Media? [Update] Last Updated Feb 19, 2011 8:05 AM EST. Preparing for cyber warfare: US Air Force floats botnet plan. US Paid Millions For Bogus (Patented) Intelligence Software; Now Trying To Cover It Up Claiming 'National Security'
Pentagon to Help Internet Providers Get Military Cyber Tools. Information Warfare Monitor. HBGary E-mails: DuPont, Other Firms Hit In Aurora Attack. Black ops: how HBGary wrote backdoors for the government. US cyber war defences 'very thin', Pentagon warns. Cyberguerre : un général veut un deuxième Internet aux Etats-Unis. Obama needs to address our cyber-warfare gap with China. A Declaration of Cyber-War. Premier test grandeur nature d'une cyber-attaque aux Etats-Unis - Monde. CBS 60 Minutes: Cyber War: Sabotaging the System 1/2. New recovery system restores virus-infected computers, could be used by agencies. Pentagon: Online Cyber Attacks Can Count as Acts of War. Taliban mobile phones and website 'hacked' Net neutrality rules declared illegal by US court.