

Jeremy Hammond. Matt DeHart claims he’s wanted for working with Anonymous. MILTON, ONT., APRIL 2014 Guards at the Maplehurst Correctional Complex, a maximum-security jail near Toronto known to inmates as the Milton Hilton, came to rouse their newest prisoner from a concrete bed in the intake holding cells.
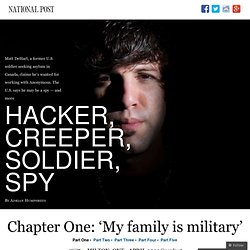
Pulling back the hoodie covering his face, they found his T-shirt had been yanked up and twisted around his throat as a ligature. The distraught prisoner was Matt DeHart, a 29-year-old American who had been brought to jail days earlier by a Canada Border Services Agency official and five police officers, who arrested him at the apartment he shares with his parents while fighting for refugee protection here. Pulled from the cell and taken to hospital, he appeared to suffer no serious physical injury but underwent a mental health assessment. Amazing Pop Culture Recreations (PICS. 23Jul These images were gathered from all over the internets but it has come to our attention that a few of them can be purchased as shirts from various sites.
If you’re looking to find some terrific t-shirts (beyond just what you may see here as well) visit Threadless, Shirt Woot! @nonymous. Leader of Anonymous Steubenville Op on Being Raided by the FBI. Deric Lostutter, the hacker formerly known as KYAnonymous In April, the FBI quietly raided the home of the hacker known as KYAnonymous in connection with his role in the Steubenville rape case.

Today he spoke out for the first time about the raid, his true identity, and his motivations for pursuing the Steubenville rapists, in an extensive interview with Mother Jones. "The goal of the media interviews is to get the entire nation to say 'fuck you' to these guys," said KYAnonymous, whose real name is Deric Lostutter. He was referring to the federal agents who raided his home in Winchester, Kentucky, and carted off his computers and XBox. Lostutter may deserve more credit than anyone for turning Steubenville into a national outrage. Anonymous Wants to Teach Rape Prevention in Schools. Ollyy/Shutterstock In late December, Anonymous hacked the Steubenville, Ohio, high school football team's fan website in retaliation for its players' involvement in the gang rape of a 16-year-old girl.

The hackers threatened to post students' and teachers' Social Security numbers unless the girl received an apology; someone else sent the school a bomb threat. “The cutting edge of cybercrime”—Lulzsec hackers get up to 32 months in jail. LONDON, UK—The four British Lulzsec hackers—Mustafa "tflow" al-Bassam, Ryan "kayla" Ackroyd, Jake "topiary" Davis, and Ryan "ViraL" Cleary—were sentenced today to between 20 and 32 months in jail for crimes committed during Lulzsec's 50 day hacking spree in 2011.

Prosecutors described the men as being at the "cutting edge of contemporary and emerging criminal offending known as cybercrime" and as "latter-day pirates. " At previous hearings, al-Bassam, 18, of Peckham, London, and Davis, 20, of the Shetland Islands, entered guilty pleas to charges of conspiracy to commit DDoS attacks against targets including Westboro Baptist Church, Sony, Bethesda, and EVE Online. They also pled to conspiracy to hack targets including Nintendo, Sony (again), PBS, and HBGary. Ackroyd, 26, of Yorkshire, pled guilty only to the hacking charge. For these crimes, al-Bassam was sentenced to 20 months, suspended for two years and received 300 hours of community service. A history of lulz Caught Difficult childhoods. Statement on Wikileaks. Supporter response to @AnonymousIRC's Statement on WikiLeaks. Exclusive: FBI Escalates War On Anonymous. How one man tracked down Anonymous. Aaron Barr believed he had penetrated Anonymous.

The loose hacker collective had been responsible for everything from anti-Scientology protests to pro-Wikileaks attacks on MasterCard and Visa, and the FBI was now after them. But matching their online identities to real-world names and locations proved daunting. Anonymous' Stratfor hack outs intelligence officials across the world. Stratfor. Hassan Chakrani, Yazan al-Saadi In his most recent op-ed in the New York Times, Nicholas D.

Kristof called talk about a military strike on Iran a consensus rather than a debate,... Read more | An Israeli intelligence agent said that contrary to common belief, Israel's renowned secret service, Mossad, was "not assassinating people that easy... Read more | US government officials requested that an American private security firm contact Syrian opposition figures in Turkey to see “how they can help in... Read more | Stratfor emails which are part of the Global Intelligence Files release by WikiLeaks imply that the Israeli intelligence agency Mossad has... Read more. Anonymous speaks: the inside story of the HBGary hack. It has been an embarrassing week for security firm HBGary and its HBGary Federal offshoot.

Mossad Doing Business with Saudi Arabia: Stratfor Source. The emails, dated 2 May 2007, show discussions between Fred Burton, Stratfor’s vice-president of counter-terrorism, and analysts in regards to the alleged secret Saudi-Israeli intelligence alliance.

The email exchange also shows that Stratfor execs considered pursuing their own business relationship with the Saudi monarchy or, as Burton called them, “sleezy arsehole ragheads.” Burton forwarded a short message to the general analyst email list which recounted HUMINT (human intelligence) on the alleged secret deal. Indian hacker group kicked-out by Facebook. The Indian arm of a hacker group 'Anonymous' - called Anonymous Operation India - has been removed from Facebook and Twitter.

Both the 'Operation India' Facebook page and '@operationindia' Twitter handle are no more accessible.'Anonymous' is a 'hacktivist' group that has been linked to the recent attack on Sony as well as against the governments of Iran, Spain, New Zealand and Colombia. Their operations started in India recently and came into the limelight when they claimed to have hacked the National Informatics Centre website and the Indian Army website last week . The NIC site on the URL was defaced with graffiti that said: "We exist without nationality. We exist with humanity. 'I'm Not Scared of Jail': My Phone Call With Sabu, the FBI's Anonymous Informant. Root is a snitch. Hackers 'steal US data in Christmas-inspired assault' Infamous international hacking group LulzSec brought down by own leader. Inside the hacking of Stratfor: the FBI's case against Antisec member Anarchaos. Stratfor: Inside the World of a Private CIA.
The leak of over five million emails from the US-based intelligence firm Stratfor, including information about credit card details, passwords, and the identities of sources, sheds new light on the rapidly changing world of intelligence gathering and exposes those behind it. Al-Akhbar gained access to the data obtained and published by WikiLeaks, including sensitive material pertaining to the Middle East. ◙ Browse through emails referenced in this article The Strategic Forecasting Inc., commonly known as Stratfor, is a private firm dealing in the lucrative business of intelligence gathering and assessment. Founded in 1996, the company gained global prominence during the NATO bombing of Kosovo in 1999 when its seemingly cutting-edge analysis was publicized by various news agencies. Doxed: how Sabu was outed by former Anons long before his arrest. When the FBI arrested LulzSec leader Hector "Sabu" Monsegur, they did so in a hurry—hours before the arrest, Sabu was doxed, his identity posted to the Internet.
With his name public, federal agents feared that he would start destroying evidence to protect himself, so they ended their covert surveillance and moved in, according to Fox News. Efforts to name and shame the LulzSec crew during its 50-day rampage were common. Many of these doxings were inaccurate, a result of faulty inferences or deliberate attempts to mislead on the part of the LulzSec hackers. But not all were wrong. In fact, the game of doxing Sabu was over before it had even started.
This first doxing happened after a group of former Anonymous members, displeased at the moralizing direction that Anonymous had taken and at Sabu's leadership role, decided to take action. Hacker Family Tree Charts Hacker Group Origins And Relations. Exclusive: British Police Duped by LulzSec Into Arresting the Wrong Guy. It appears UK police have been deceived by LulzSec. (Source: Warner Brothers) The man they believed to be a member of LulzSec was reportedly a famous internet troll, whom a LulzSec member "stole" the name of.
This could prove the latest embarasment for UK police. (Source: Gaming Union) Everything Anonymous. Open Letter to Al Jazeera. To whom it may concern I took the red pill I took it when I joined some IR. In ‘Anonymous’ Raids, Feds Work From List of Top 1,000 Protesters. It turns out there’s a method behind the FBI’s raids of suspected Anonymous members around the country. The bureau is working from a list, provided by PayPal, of the 1,000 internet IP addresses responsible for the most protest traffic during Anonymous’ DDoS attacks against PayPal last December. FBI agents served 40 search warrants in January on people suspected of hosing down PayPal during ”Operation Payback” — Anonymous’ retaliatory attack against companies who blacklisted WikiLeaks. Anonymous and LulzSec's Existence Scares ISP into Halting Web Censorship. LulzSec hacking suspect ‘Topiary’ arrested in the Shetland Islands.
An 18-year old man has been arrested by British police in Shetland, UK, under suspicion of launching hacking attacks against a number of websites. Officers from the Metropolitan Police Service's Police Central e-Crime Unit (PCeU) arrested the man as part of an international investigation into the activities of the Anonymous and LulzSec hacktivist groups. Anonymous & Lulz Security Statement.