

Breaking out of a chroot() padded cell. This page details how the chroot() system call can be used to provide an additional layer of security when running untrusted programs.
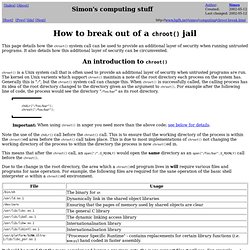
It also details how this additional layer of security can be circumvented. chroot() is a Unix system call that is often used to provide an additional layer of security when untrusted programs are run. The kernel on Unix varients which support chroot() maintain a note of the root directory each process on the system has. Generally this is "/", but the chroot() system call can change this. When chroot() is successfully called, the calling process has its idea of the root directory changed to the directory given as the argument to chroot(). Chdir("/foo/bar"); chroot("/foo/bar"); Note the use of the chdir() call before the chroot() call. This means that after the chroot() call, an open("/",O_RDONLY) would open the same directory as an open("/foo/bar",O_RDONLY) call before the chroot().
Whilst chroot() is reasonably secure, a program can escape from its trap. Creating chroot sftp Jails with Jailkit. One of the things I both love and hate about my job is getting assigned new projects.

They can be about anything and everything. A few months back I was given an assignment to create some chroot jails for a group of customers so that they could securely upload files with sftp. The requirement was that the customers needed to be able to upload file, but in a secure and private way. Customer One should not be able to see Customer Two's files, for example. And neither customer should be able to browse the filesystem of the server. I've used the chroot command many times, it's a very handy way of fixing servers that can't otherwise be fixed --- like when no one can remember the root password on some box that no one has touched for years. Chroot /mnt/hda1 Suddenly it's like you are root on the local filesystem and not on the live CD.
You can do a lot more with chroot than simply use it as part of your system recovery toolkit though. Daniel@bart:~$ mkdir /opt/jail 1. So what did I do? 1. Chrooted SSH/SFTP On Fedora 7. Version 1.0 Author: Oliver Meyer <o [dot] meyer [at] projektfarm [dot] de> Last edited 10/08/2007 This document describes how to set up a chrooted SSH/SFTP environment on Fedora 7.

The chrooted users will be jailed in a specific directory where they can't break out. They will be able to access their jail via SSH and SFTP. This howto is meant as a practical guide; it does not cover the theoretical backgrounds. They are treated in a lot of other documents in the web. This document comes without warranty of any kind! 1 First Method (By Hand) 1.1 Install The Chrooted OpenSSH First we have to install some needed packages: yum install openssl-devel pam-devel yum groupinstall 'Development Tools' Afterwards we have to customize the ssh/sshd-configuration: vi /etc/ssh/sshd_config change GSSAPIAuthentication yes GSSAPICleanupCredentials yes to #GSSAPIAuthentication yes #GSSAPICleanupCredentials yes vi /etc/ssh/ssh_config GSSAPIAuthentication yes #GSSAPIAuthentication yes 1.2 Create The Chroot Environment #!
E.g.