

16 Things You Can Do Today to Get Your Artwork Noticed. Note: Once you’ve finished here, why not checkout the follow-up post on my art blog – 10 More Things You Can Do to Get Your Artwork Noticed.
Whether you’re a hobbyist sculptor, a part-time photographer, or a full-time artist, if you’re proud of what you create, I bet you’d like as many people to see it as possible, right? I hear a lot of artists saying they just don’t know how to get their artwork noticed. So here are 16 actions that you can actually put into practice today, that will help increase your artwork’s exposure: Tech Firm Ubiquiti Suffers $46M Cyberheist. Networking firm Ubiquiti Networks Inc. disclosed this week that cyber thieves recently stole $46.7 million using an increasingly common scam in which crooks spoof communications from executives at the victim firm in a bid to initiate unauthorized international wire transfers.
Ubiquiti, a San Jose based maker of networking technology for service providers and enterprises, disclosed the attack in a quarterly financial report filed this week with the U.S. Securities and Exchange Commission (SEC). The company said it discovered the fraud on June 5, 2015, and that the incident involved employee impersonation and fraudulent requests from an outside entity targeting the company’s finance department. RHEL 6 Installation Guide - Chapter 36. Basic System Recovery. 36.1.2.

Booting into Rescue Mode Rescue mode provides the ability to boot a small Red Hat Enterprise Linux environment entirely from CD-ROM, or some other boot method, instead of the system's hard drive. As the name implies, rescue mode is provided to rescue you from something. During normal operation, your Red Hat Enterprise Linux system uses files located on your system's hard drive to do everything — run programs, store your files, and more. However, there may be times when you are unable to get Red Hat Enterprise Linux running completely enough to access files on your system's hard drive. To boot into rescue mode, you must be able to boot the system using one of the following methods[]: By booting the system from a boot CD-ROM or DVD.By booting the system from other installation boot media, such as USB flash devices.By booting the system from the Red Hat Enterprise Linux installation DVD. linux rescue. Internet Census 2012. All data collected during the Internet Census 2012 is available for download via BitTorrent.
Labs Archives. Get cutting-edge security as it happens.
Read our experts’ tips and techniques to help you avoid and defeat the latest malware trends, and view portions of their actual research to stay even more informed. Money acts as one of the key drivers for cybercrime. Add to this cybercrime’s lower risk than traditional crime, and there is little wonder that we are witnessing the evolution of crime to the digital sphere.
In previous research papers, we focused on the service-based nature of cybercrime, in which anybody can be a cybercriminal […] Mobile banking Trojans have usually pretended to be security applications (for example, Zitmo) or legitimate banking apps (FakeToken or FkSite a.k.a. Use These Secret NSA Google Search Tips to Become Your Own Spy Agency. There’s so much data available on the internet that even government cyberspies need a little help now and then to sift through it all.
So to assist them, the National Security Agency produced a book to help its spies uncover intelligence hiding on the web. The 643-page tome, called Untangling the Web: A Guide to Internet Research (.pdf), was just released by the NSA following a FOIA request filed in April by MuckRock, a site that charges fees to process public records for activists and others. The book was published by the Center for Digital Content of the National Security Agency, and is filled with advice for using search engines, the Internet Archive and other online tools. But the most interesting is the chapter titled “Google Hacking.”
Weblog : News from the Lab. Whether he's the guy or not… it fits the typical profile.
A young person with good SEO skills pushing a rather useless app. Lame "SEO apps" are prevalent on Google Play. They're easy to find if you look. For example: • Best Antivirus Lite • SAFE antivirus Limited • Skulls Antivirus • Shnarped Hockey antivirus lite Best and SAFE link to one "developer" — while Skulls and Shnarped Hockey link to another. Though there are two different developers… the apps are identical apart from their name. Android apps: no developer skills required. SEC Consult - Advisories. Ethical Hacking-Your Way To The World Of IT Security: Metasploit Tutorials. SQLMAP Basic Introduction and Tutorial. Employees Sample Database. The Employees database is available from Employees DB on Launchpad.

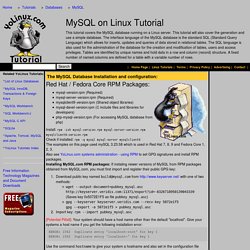
You can download a prepackaged archive of the data, or access the information through Bazaar. To use the archive package, download the archive and unpack it: shell> tar -xjf $HOME/Downloads/employees_db-full-1.0.6.tar.bz2 shell> cd employees_db/ The Employees database is compatible with several different storage engines, with the InnoDB engine enabled by default. MySQL Tutorial - Learn MySQL Fast, Easy and Fun. Login - how do I see which user I am logged in as in MySQL? MySQL database on Linux Tutorial. The MySQL Database Installation and configuration:
Ultimate Web Guide to SQL Database Language. General Information SQL stands for Structured Query Language and is a computer language that is used to interact with and manage a database.

It is the most widely used language used to manage databases. One thing that is important to note is that SQL is not a specific database system, there are many database systems that use SQL. The most commonly used is MySQL, however there are dozens of different systems, including Microsoft SQL, and Oracle as well as many lesser known systems. SQL tutorial from W3Schools SQL tutorials with a lot of help with query commands SQL tutorials from 1keydata SQL Course Installing SQL When installing SQL, it is important to first decide which database system you want to install. XAMPP for Windows/Linux/Mac WAMP for Windows How to build a LAMP server How to install LAMP on Ubuntu. Web Clipper.