

TrueCrypt - Free Open-Source On-The-Fly Disk Encryption Software for Windows 7/Vista/XP, Mac OS X and Linux. Ritter's Crypto Glossary and Dictionary of Technical Cryptography. Copyright 1995 to 2007 Terry Ritter.
All Rights Reserved. Or use the browser facility "Edit / Find on this page" to search for particular terms. This Glossary started as a way to explain the terms on my cryptography web pages describing my: The value of a definition is insight. But: Consider the idea that cryptography is used to keep secrets: We expect a cipher to win each and every contest brought by anyone who wishes to expose secrets. Even though the entire reason for using cryptography is to protect secret information, it is by definition impossible to know whether a cipher can do that. Consider the cryptographer who says: "My cipher is strong," and the cryptanalyst who says: "I think your cipher is weak.
" The situation is inherently unbalanced, with a bias against the cryptographer's detailed and thought-out claims, and for mere handwave first-thoughts from anyone who deigns to comment. Learning About Cryptography. A Ciphers By Ritter Page Terry Ritter 2006 January 20 For some reason, good cryptography is just much harder than it looks.
This field seems to have a continuous flow of experts from other fields who offer cryptographic variations of ideas which are common in their other field. Now, there is nothing wrong with new ideas. You may wish to help support this work by patronizing Ritter's Crypto Bookshop. VPN remote access server, connection and software set up. How to set up a VPN. If you work on the go fairly often, you've probably hopped on a public wireless network at least once or twice.
You should have also figured out how to keep your data safe when you're on such a network, by taking precautions such as using your company's virtual private network, if available, or an encrypted web tunnel such as Hotspot Shield. If you don't have a company VPN and you don't want to deal with Hotspot Shield's banner ads, however, you can still secure your wireless traffic without breaking the bank by setting up your own VPN and gaining a private, encrypted Internet connection free from eavesdroppers. Tunneling Your Traffic Whether the public wireless network you use is password-protected or pay-per-minute, anyone who connects to the network could spy on your HTTP traffic, restaurant patrons, other people in your airport concourse, or other paying subscribers of a commercial hotspot provider.
Easy, Cheap Security via SSH. Step-by-Step Guide for Setting Up VPN-based Remote Access in a Test Lab. This guide provides detailed information about how you can use five computers to create a test lab with which to configure and test virtual private network (VPN) remote access with the Microsoft® Windows® XP Professional operating system with Service Pack 2 (SP2) and the 32-bit versions of the Microsoft Windows Server™ 2003 operating system with Service Pack 1 (SP1).
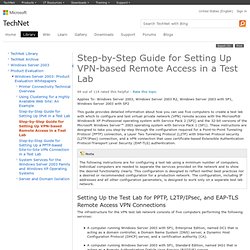
These instructions are designed to take you step-by-step through the configuration required for a Point-to-Point Tunneling Protocol (PPTP) connection, a Layer Two Tunneling Protocol (L2TP) with Internet Protocol security (L2TP/IPsec) connection, and a VPN connection that uses certificate-based Extensible Authentication Protocol-Transport Level Security (EAP-TLS) authentication. Setting Up the Test Lab for PPTP, L2TP/IPsec, and EAP-TLS Remote Access VPN Connections The infrastructure for the VPN test lab network consists of five computers performing the following services: IIS1 obtains its IP address configuration using DHCP.
VPN Router tutorial with IPSec Client software. VPN Setup for Routers - Getting it to work with an IPSec Client Configuration Challenge Level: Meduim Technical Summary: This article will show how to setup a Broadband Router that has IPSec VPN capabilities for secure remote access to your home network from anywhere on the Internet. Detailed configuration will be shown for multiple brands of routers. VPN Setup - How to Set Up a VPN. Virtual Private Networks (VPNs) are a more advanced form of computer networking, but setting up a VPN is not necessarily difficult.

A VPN setup involves both server and client configuration. Some details depend on the type of VPN and other network technologies involved. VyprVPN for Giganews Diamond Customers. New Hacking Tools Pose Bigger Threats to Wi-Fi Users. Strong Password Generator. Virtual Networking with LogMeIn Hamachi² Centralized Software Deployment Save yourself onsite visits.

Quickly and easily dispatch virtual network client software to new computers remotely. Simply send end users a link to download and install the client to participate in a specific virtual network. Manage and Restore Networks Handle your virtual networks virtually. Manage and restore virtual networks for end-users with the click of a mouse, from anywhere via the web. Client Configuration Management Configure settings for individual networks and clients. Set default settings for individual networks and clients, with support for full, restricted and minimal client interface modes. Up to 256 clients per LogMeIn ID. Centralized Access Controls All network access and usage controls, in one place. Control network access and usage, including password management, network authentication, network locking, and ongoing network membership.