

Jnicklas/capybara. Home - Arachni - Web Application Security Scanner Framework. Pry - an IRB alternative and runtime developer console. CasperJS, a navigation scripting and testing utility for PhantomJS and SlimerJS. PhantomJS. Simhash - Create a "hash" function which hashes similar files to similar keys. SimHash - Home. Ocramius/ProxyManager.
Cheapest CAPTCHA bypass service — Death By Captcha. Alsmola/nopassword. Chartkick. Rubyvis: Ruby version of Protovis. Protocol misidentification made easy. Obfsproxy. Obfsproxy obfsproxy is a tool that attempts to circumvent censorship, by transforming the Tor traffic between the client and the bridge.

This way, censors, who usually monitor traffic between the client and the bridge, will see innocent-looking transformed traffic instead of the actual Tor traffic. obfsproxy supports multiple protocols, called pluggable transports, which specify how the traffic is transformed. For example, there might be a HTTP transport which transforms Tor traffic to look like regular HTTP traffic. See the pluggable transports page for more information. Even though obfsproxy is a separate application, completely independent from tor, it speaks to tor using an internal protocol to minimize necessary end-user configuration.
Please open a ticket on our bug tracker for any bugs you find or features you would like to see added in future releases. Looking for obfsproxy bridges? You can use BridgeDB to get obfsproxy bridges. Download the Pluggable Transports Tor Browser Bundle. Iodine (IP-over-DNS, IPv4 over DNS tunnel) Iodine Latest (from 2014-06-16): 0.7.0 Download source / binaries: win32/64, android Older downloads available below. iodine lets you tunnel IPv4 data through a DNS server.
This can be usable in different situations where internet access is firewalled, but DNS queries are allowed. It runs on Linux, Mac OS X, FreeBSD, NetBSD, OpenBSD and Windows and needs a TUN/TAP device. The bandwidth is asymmetrical with limited upstream and up to 1 Mbit/s downstream. Compared to other DNS tunnel implementations, iodine offers: Higher performance iodine uses the NULL type that allows the downstream data to be sent without encoding. PTPd - Precision Time Protocol daemon - Vimperator. Socat - Vimperator. Dest-unreach / socat Abstract what: "netcat++" (extended design, new implementation) OS: AIX, BSD, HP-UX, Linux, Solaris e.a.
(UNIX) lic: GPL2 inst: tar x...; . SecTools.Org Top Network Security Tools - Vimperator. Gnuplot tips (not so Frequently Asked Questions) - Vimperator. New Linux Distro for Mobile Security, Malware Analysis, and Forensics - Vimperator. Yes, you read the title right and I hope I just grabbed your attention!

A new GNU/Linux distribution or distro designed for helping you in every aspect of your mobile forensics, mobile malware analysis, reverse engineering and security testing needs and experience has just been unleashed and its alpha version is now available for download for you to try out. Guys, meet the new Santoku Linux! Santoku is a general purpose kitchen knife which originated from Japan. Santoku means “three virtues” or “three uses” (Wikipedia). This distribution is not from Japan, butthe name was suggested by Thomas Cannon of viaForensics (who happens to be the project leader of Santoku Linux) because the distribution was crafted specifically for Mobile Forensics, Mobile Malware Analysis, and Mobile Security Testing. The Three Virtues or Three Uses Mobile Forensics: Mobile Malware Analysis Mobile Security Testing Want to learn more??
List of Tools for the Alpha Release. Smartphone Pentest Framework v.0.1 - Vimperator. Remastersys - Vimperator. Fierce Domain Scan - Vimperator. Written by RSnake with input from id, Vacuum and Robert E Lee.

A special thanks to IceShaman to porting it to use multi-threading. Fierce domain scan was born out of personal frustration after performing a web application security audit. It is traditionally very difficult to discover large swaths of a corporate network that is non-contiguous. It's terribly easy to run a scanner against an IP range, but if the IP ranges are nowhere near one another you can miss huge chunks of networks. First what Fierce is not. First it queries your DNS for the DNS servers of the target. Next, if it finds anything on any IP address it will scan up and down a set amount (default 5 but you can expand it with -traverse or increase it to the entire subnet with -wide) looking for anything else with the same domain name in it using reverse lookups.
I also added a random call to something that should fail to test for wildcard DNS. Perl fierce.pl -dns widget.com -search widgetcompany,nutsandbolts Not convinced? Project Objectives - Vimperator. Vimperator. BBQSQL - Blind SQL Injection Exploitation Tool - Vimperator. Lab of a Penetration Tester - Vimperator. NetWire first Multi-platform RAT - Vimperator. NetWire claim to be the first Multi-platform RAT, it can generate output for Windows, Linux, Solaris and Mac OS X.
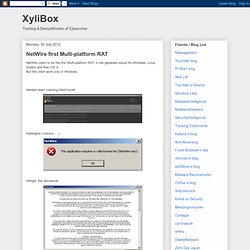
But the client work only in Windows. Netwire team clashing DarkComet: Safengine Licensor... :) Allright, the disclaimer: Main interface Password generator feature: Application proxifier: