

Free NetFlix Movies Premium Account Login Username and Password. Monsanto Now Owns Blackwater (Xe) A report by Jeremy Scahill in The Nation (Blackwater’s Black Ops, 9/15/2010) revealed that the largest mercenary army in the world, Blackwater (now called Xe Services) clandestine intelligence services was sold to the multinational Monsanto.

Blackwater was renamed in 2009 after becoming famous in the world with numerous reports of abuses in Iraq, including massacres of civilians. It remains the largest private contractor of the U.S. Department of State “security services,” that practices state terrorism by giving the government the opportunity to deny it. Many military and former CIA officers work for Blackwater or related companies created to divert attention from their bad reputation and make more profit selling their nefarious services-ranging from information and intelligence to infiltration, political lobbying and paramilitary training – for other governments, banks and multinational corporations. How to stop your phone from being tracked. New Bill Known As Enemy Expatriation Act Would Allow Government To Strip Citizenship Without Conviction.
First, Congress considered the National Defense Authorization Act, sections of which gave the President the authority to use the military to arrest and indefinitely detain Americans without trial or charge.
The language was revised because of strong condemnation from the American people. But now a new bill has emerged that poses yet another threat to the American citizenry. Congress is considering HR 3166 and S. 1698 also known as the Enemy Expatriation Act, sponsored by Joe Lieberman (I-CT) and Charles Dent (R-PA). This bill would give the US government the power to strip Americans of their citizenship without being convicted of being “hostile” against the United States.
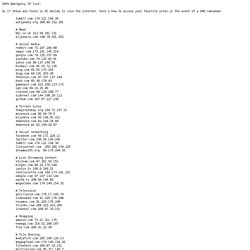
In other words, you can be stripped of your nationality for “engaging in, or purposefully and materially supporting, hostilities against the United States.” #3038363. SOPA Emergency IP list: So if these ass-fucks in DC decide to ruin the internet, here’s how to access your favorite sites in the event of a DNS takedown.
7 Lessons: Surviving A Zero-Day Attack - Security - Attacks/breaches. Pacific Northwest National Laboratory CIO Jerry Johnson takes you inside the cyber attack that he faced down--and shares his security lessons learned.

When Pacific Northwest National Laboratory detected a cyber attack--actually two of them--against its tech infrastructure in July, the lab acted quickly to root out the exploits and secure its network. 10 programming languages that could shake up IT. Do we really need another programming language?

There is certainly no shortage of choices already. Between imperative languages, functional languages, object-oriented languages, dynamic languages, compiled languages, interpreted languages, and scripting languages, no developer could ever learn all of the options available today. And yet, new languages emerge with surprising frequency. Some are designed by students or hobbyists as personal projects. Others are the products of large IT vendors. Anonymous leaks 10,000 ‘top secret’ Iranian gov’t emails. Free File Downloads and Software Discussion. How to Open God Mode on Windows 8, 7 & Vista. ANONYMOUS MESSAGE: TO AUSTRALIA & ITS GOVERNMENT:MISSING:Human Rights.wmv.
CIA installed nuclear surveillance device atop Himalayas mountains. CIA, Mossad made up fairytale al-Qaeda. CIA, Mossad made up fairytale al-Qaeda Wayne Madsen An American investigative journalist says the al-Qaeda is a fairytale terrorist group made up by the Central Intelligence Agency (CIA) and the Israeli spy agency, Mossad.

"In the US, the Zionist propagandists are spinning the fanciful tale that Iran was involved with "al-Qaeda," the fairy tale organization concocted by Mossad and the CIA, in carrying out the 9/11 attacks," Wayne Madsen wrote in an article published in Global Research. Madsen was referring to the latest US allegation that Iran was involved in the September 11, 2001 attacks on New York and Washington. On December 22, a US federal judge in Manhattan alleged that Iran, together with the Taliban and al-Qaeda, had been involved in the 9/11 attacks. The Decline of the American Empire. Hackers plan space satellites to combat censorship. 4 January 2012Last updated at 06:52 ET By David Meyer Technology reporter 50 years after Russia's first piloted mission, hackers plan to send their own people beyond orbit Computer hackers plan to take the internet beyond the reach of censors by putting their own communication satellites into orbit.

10 Search Engines to Explore the Invisible Web. Not everything on the web will show up in a list of search results on Google or Bing; there are lots of places that their web crawlers cannot access. To explore the invisible web, you need to use specialist search engines. Here are our top 12 services to perform a deep internet search. Julian Assange Explains Who The Bastards Are. Wikipedia Leaves GoDaddy Over Stop Online Piracy Act (SOPA) Top Secret Alan Watt: The World Has been Planned out.. And we are to be removed, HAARP YELLOWSTONE. Meet Telecomix, The Hackers Bent On Exposing Those Who Censor And Surveil The Internet. The 101 Most Useful Websites on the Internet. Here are the most useful websites on the Internet that will make you smarter, increase productivity and help you learn new skills.
These incredibly useful websites solve at least one problem really well. Anonymous attacks security firm Stratfor, $1M stolen/donated. 'Anonymous' hackers hit US security firm Stratfor. 26 December 2011Last updated at 00:14 Stratfor urged its members to notify authorities about any suspicious credit card activities The activist hacker group Anonymous says it has stolen thousands of emails, passwords and credit card details from a US-based security think tank.

The hackers claim they were able to obtain the information because the company, Stratfor, did not encrypt it. They say Stratfor's clients include the US defence department, law enforcement agencies and media organisations. The 1 Percenters Who Act Like Scrooge...and the Ones Who Don't. December 22, 2011 | Like this article?

Join our email list: Stay up to date with the latest headlines via email. This Dynamic Planet. Facebook. Can Anonymous Cripple Critical U.S. Infrastructure? - Security - Vulnerabilities and threats. Homeland Security says Anonymous can cause DDoS attacks, but says chance of attack on scale of Stuxnet is slim. 10 Companies Driving Mobile Security (click image for larger view and for slideshow) Does the hacktivist collective known as Anonymous pose a threat to the nation's critical infrastructure security?

According to a recent government report, the group may well be able to launch a distributed denial of service attack against critical infrastructure. The CIA in Australia: AMERICA’S FOREIGN WATERGATE. The CIA in Australia: “The CIA’s aim in Australia was to get rid of a government they did not like and that was not co-operative… it’s a Chile, but in a much more sophisticated and subtle form.” Virginia Tech's Wu Feng unveils HokieSpeed, a new powerful supercomputer for the masses. Public release date: 21-Dec-2011 [ Print | E-mail Share ] [ Close Window ] Contact: Steven Mackaysmackay@vt.edu 540-231-4787Virginia Tech Virginia Tech crashed the supercomputing arena in 2003 with System X, a machine that placed the university among the world's top computational research facilities.
Now comes HokieSpeed, a new supercomputer that is up to 22 times faster and yet a quarter of the size of X, boasting a single-precision peak of 455 teraflops, or 455 trillion operations per second, and a double-precision peak of 240 teraflops, or 240 trillion operations per second. Police Device Used To Steal Your Cell Phone Data During Traffic Stop. You may have heard about the Cellebrite cell phone extraction device (UFED) in the news lately. It gives law enforcement officials the ability to access all the information on your cell phone within a few short minutes. When it became known that Michigan State Police had been using the tool to access cell phones during traffic stops, it raised concern with the ACLU. Now, everyone is wondering if cops will be using devices like this elsewhere. Will this new law enforcement tool be abused, or will it be used responsibly in the pursuit of justice?
Call us paranoid, but we obtained a law-enforcement-grade software extraction tool for the iPhone to see exactly what data is up for grabs. Click the gallery below to find out... RAP NEWS X - #Occupy2012. Photos of Occupy Wall Street. Russian Intelligence Calls Facebook Information Warfare Weapon. Are We Living in a Super-Computer Simulation with Aliens Beings? Steve Antonoff - Weighing the Risks of Solid-State Drives. Islamic extremists call for death of lesbian author / DIVA Magazine Lesbian News. Obama: I can’t comment on Wall Street prosecutions. (updated below) President Obama was interviewed by 60 Minutes‘ Steve Kroft last night. Kroft mentioned a new poll showing that 42% of Americans believe Obama’s policies most favor Wall Street rather than average Americans (only 35% believe the opposite). Future Riot Shields Will Suffocate Protestors with Low Frequency Speakers.
Rock fans have heads shaved and get 'cleansed' in river in Islamic law crackdown. 65 youths have been sent to a police school in Indonesia's Aceh province to receive mental and spiritual guidance for ten daysOnly then are they are allowed to return home By Graham Smith Updated: 11:46 GMT, 15 December 2011. FEMA Imprisonment - Obama Announces Proplonged Detention ( 14 December 2011 Speech ) TrendLabs - by Trend Micro.
FileHippo.com - Download Free Software. Panoramas archive. Free Video Converter. History. MajorGeeks.com - Download Freeware and Shareware Computer Utilities. Pentagon Partners With NATO To Create Global Cyber Warfare System. Stop NATO October 8, 2010 Pentagon Partners With NATO To Create Global Cyber Warfare System Rick Rozoff. Downloadable Computer Repair CDs. Wikileak: This is How the Government Tracks You. Your Likes.