

Intellectual Property Rights policy and IPR online database. ETSI definition of Intellectual Property Right (IPR) within the ETSI IPR Policy: “IPR shall mean any intellectual property right conferred by statute law including applications therefor other than trademarks.
For the avoidance of doubt rights relating to get-up, confidential information, trade secrets or the like are excluded from the definition of IPR”. Standards rely on technical contributions from various sources. These contributions may contain patented technologies which are commonly known as Standard Essential Patents (SEP). Cellular Algorithm Licences – Algorithms for GSM and GPRS. Confidentiality & integrity algorithms for GSM and GPRS The A5/4 and A5/3 encryption algorithms for GSM™ and EDGE, the GEA5, GEA4, GEA3 and GEA2 encryption algorithms for the General Packet Radio Service (GPRS), and the GIA5 and GIA4 integrity algorithms for GPRS may be used only for the development and operation of GSM, EDGE and GPRS mobile communications and services.

Every Beneficiary intending to implement and/or use the algorithms must sign a Restricted Usage Undertaking with a Custodian and demonstrate that he/she fulfils the approval criteria specified in that undertaking. The A5/4 and A5/3 and GEA4 and GEA3 algorithms are based on the Third Generation Partnership Project (3GPP™) ciphering algorithm, UEA1, for which the Mitsubishi Electric Corporation holds essential patents.
For the purposes of implementing these algorithms, Mitsubishi has agreed to grant licences on a royalty free basis. Licensing procedure within ETSI. Billy Riggs Billy Riggs, Master DIS-illusionist! Watch more videos of Billy by clicking “TOPICS” on the Nav Bar above!
Billy Riggs is one of the Top Business and Motivational Corporate Speakers in America! With more than 35 years as a public speaker, his style is dynamic and gripping. ETSI NFV announces new features to its architecture to support 5G. Sophia Antipolis, 1 July 2019 ETSI NFV has enhanced the system as well as designed new features to support 5G networks. Specifically, 5G resource management and orchestration aspects were added on top of the NFV Release 2 architecture framework. New NFV Release 3 features that closely relate to 5G include: “Support for network slicing in NFV”, “Management over multi-administrative domains”, and “Multi-site network connectivity”.
These features are essential to address the variety of applications expected to run on top of a 5G system, whether using distributed resources over multiple sites, centralized or a combination of both. Since early 2012, ETSI has made significant progress on specification work for Network Functions Virtualization (NFV) through its NFV Industry Specification Group. Cyber Security Technology. Introduction The world has never been more connected than it is today.

The Internet has become critical to our everyday lives, for businesses and individuals, and so too has its security. With our growing dependence on networked digital systems comes an increase in the variety and scale of threats and cyber attacks. A variety in the protective methods used by countries or organizations can make it difficult to assess risk systematically and to ensure consistent, adequate security.
ICT White Papers. Quantum Key Distribution. Extra_toc Introduction Based on the outcome of the EC FP6-project SECOQC (Secure Communication based on Quantum Cryptography), an Industry Specification Group (ISG) of the European Telecommunications Standards Institute (ETSI) shall bring together the important European actors from science, industry, and commence to address standardisation issues in quantum cryptography, and quantum technology in general.
During recent years quantum cryptography has been the object of a vivid activity and rapid progress, and it is now extending into a competitive industry with commercial products. Quantum Key Distribution is a cryptographic primitive. Analysing the cryptographic implications of Quantum Key Distribution is a very complex task. Many countries outside Europe have already made efforts to kick-off national standardisation for quantum technologies.
ETSI issues report on IoT devices for emergency communications. Sophia Antipolis, 1st of August 2019 Since the Internet has matured, society has become more interconnected, as have the devices used to enhance everyday lives.

Since the Internet has matured, society has become more interconnected, as have the devices used to enhance everyday lives. This has led to the emergence of the so-called "Internet of Things" (IoT), in which autonomous devices as well as people are now interconnected in and across private, public, and industrial spaces. IoT technologies are invading all application domains including services relevant to emergency situations with a scope wider than IoT connectivity and communication systems. ETSI TR 103 582 also helps prepare the potential standardization requirements enabling a safe operation of these communications. List of Private Hospitals in Abu Dhabi, UAE.
Additional Information The content and information available on enritsch.com, including without limitation, such as text, graphics, images, audio, videos and other material contained on the Enritsch Site ("Content") are for informational purposes only.
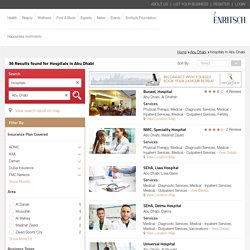
The Content is not intended to be a substitute for professional medical advice, diagnosis, or treatment. Always seek the advice of your physician or other qualified health provider with any questions you may have regarding a medical condition. Never disregard professional medical advice or delay in seeking it because of something you have read on the Enritsch site! If you think you may have a medical emergency, call your doctor or ambulance (998 in UAE) immediately. The Site may contain health- or medical-related materials that are sexually explicit. ETSI Security week 2019 - debating different aspects of cybersecurity.
ETSI - Smart Appliances. Extra_toc Introduction Currently, household appliances are responsible for about two thirds of the energy consumed by buildings.
Industrial appliances are also major energy users. In the future, domestic and industrial appliances will be intelligent, networked smart devices, forming complete energy consuming, producing and managing systems, based on the integration of products from different vendors and vertical industrial sectors. The need for all these connected appliances to be able to communicate among themselves and with the service platforms needs to be addressed. ETSI - Mobile Communications Technologies - GPRS, GSMA & UMTS. Extra_toc Introduction User demand is driving the mobile communication industry to develop faster, more efficient and more comprehensive mobile services.
User expectations and use cases continue to grow and ETSI, a founding partner of the 3rd Generation Partnership Project (3GPP), aims to remain very much part of this evolution of mobile communication systems. ETSI is proud to have a leading role in the development of mobile communication technologies. ETSI - Smart Cities - Smart City Applications. Introduction Today more than half of the world’s population lives in urban areas, and this figure is expected to rise significantly in coming years.
This places new demands on key city services and infrastructure such as transport, energy, health care, water and waste management. Information and Communications Technologies (ICT) play an important role in connecting these resources, securely managing the massive amounts of data generated, and providing the relevant services that are required. A ‘smart city’ uses digital technologies to: ETSI - Internet of Things - IoT Standards. Extra_toc Introduction It’s estimated that the number of connected devices in the Internet of Things (IoT) already exceeds the world’s population.
And with this figure anticipated to outstrip 20 billion by 2020, the IoT is having a transformative influence on the way we live and work in domains including: Technology blogs, NFV, MEC, NGP, ZSM, ENI - Pushing forward in the ETSI ZSM#7 meeting. The ZSM#7 meeting was hosted by Intel on 17-21 June, 2019, at their headquarters in the sunny city of Santa Clara, California. ETSI - ETSI specifications on licensed shared spectrum successfully implemented in the Netherlands for the entertainment industry. ETSI - SIM. In terms of 'sales' the (Subscriber Identity Module) SIM must rank as ETSI's most successful standard.
There are four billion SIM cards in the world and no sign of a slowdown in the demand for them. Now the SIM Card is set to develop in to the 'Smart Card' with a growing variety of applications and features. The SIM used in Digital Cellular Telecommunications Systems like 3G or GSM is the entity that contains the identity of the subscriber. When the SIM is placed in a terminal or handset, users can register onto a network. The primary function of the SIM is to authenticate the validity of a terminal when accessing the network. The ETSI work on Smart Cards now looks to evolve the SIM card, towards allowing contact-less data flow for Identity, Security and Payment applications. SIM standardization is concentrated in two committees: ETSI - Internet of Things - IoT Standards. ETSI - ETSI NFV announces new features to its architecture to support 5G.
ETSI - ETSI releases 3 new ontology specifications for Smart Cities, Industry 4.0 and Smart Agriculture. ETSI - ETSI OSM Release SIX enhances Edge support and lets your Network Service fly. Sophia Antipolis, 20 June 2019 ETSI OSM Release SIX is now available! The new Release brings a huge new set of capabilities to provide end-to-end orchestration across heterogeneous networks and cloud technologies. ETSI - ETSI hosts another successful Security Week. Sophia Antipolis, 21 June 2019 ETSI Security Week 2019 (17-21 June) attracted over 300 attendees to ETSI’s headquarters to listen to presentations and engage in panel discussions and networking with leading experts in cybersecurity from industry, universities, governmental bodies and national security agencies.
As networked computing technology spreads into almost every aspect of our daily lives Internet security is becoming one of the first items addressed in any new ICT implementation. ETSI - Custodian, Security algorithms, codes, licences. Introduction An encryption algorithm is a mathematical procedure used to encrypt data. Through the use of an algorithm and a key, information is encoded into cipher text and requires the use of a 'key' to transform the data back into its original form.
Algorithms are an essential part of a technology to ensure effective and secure authentication, as well as to provide integrity and encryption. Buy Electronic & Digital Signature. Extra_toc.