

CyberWar - Book Store. All companies.
SimonSinek 2009X 480p en. Música. Kong - Open-Source API Management and Microservice Management. NodeSchool. Functional Javascript Learn fundamental functional programming features of JavaScript in vanilla ES5.
CEACCU - Organización de Consumidores. Seeketing - Home. Offline & Online intelligence We assign the same ID for each visitor, both when they visit your physical venue/store or when they use your Apps, or visit your web or e-commerce site.

A true omnichannel solution, capable of optimizing marketing campaigns both online and offline. Key features and benefits through the organization Gain a unified view of store performance that integrates staffing, sales, store layout, and foot traffic.
Testing. Bruselas con Ñ » Sábado de doce a dos de la tarde en Radio Alma 101.9 FM Bruselas. Charte « Blogs Radio Alma 101.9FM Bruxelles. IoT. Dr. Eduardo Anitua. Home Red Seguridad. Revista especializada en Seguridad TIC. Éstas son, en esencia: la interactividad, la conectividad, la ubicuidad, el dinamismo, la abolición de espacios geográficos y temporales, la superación del perímetro de seguridad corporativa.

Ese camino que implica transitar de la realidad física a la virtual, mientras conviven, plantea a las empresas retos de tipo organizativo, tecnológico, legal, probatorio, cultural, de seguridad, etc.
RadioHacking. ElevenPaths Talks. Descubre la Programación. Free Courses. VR. Vincent´s coding classes. The xonsh shell — xonsh 0.3.4 documentation. Sobre el hackeo al sindicato de los Mossos y la filtración de información policial. Networking & Security Cours. Bobby Rogers – Principal Information Assurance Analyst. Bobby Rogers Bobby Rogers is a Principal Information Assurance Analyst currently working as a contractor for Department of Defense systems.
His primary duties include information system security engineering and penetration testing. He served for 21 years in the United States Air Force as a network security engineer and instructor. He has secured networks all over the world! Bobby has a Master’s degree in Information Assurance and his many certifications include the CISSP-ISSEP, CEH, CPTS, and MCSE: Security. Video Tutorial, Funcionamiento de la Plataforma Educativa DragonJAR.
The Complete Mobile Game Development Course – Platinum Edition. Product Description Funded through Kickstarter by 550+ people.
Our Kickstarter-funded courses 1) JavaScript Programming, Learn by Making a Mobile Game (included in all packages of The Complete Mobile Game Development Course) NewMOOVE con Pentium, i5 e i7 de 6ª generación - VANT VANT.
Emisoras de radio españolas, radios online de España, escuchar radio. Canciones. Libros gratis. Hacking & Digital Forensics & Autopsy - Stay Anonymous. The Course has been updated on January 2016 with technology advancement today.

Are you staying on anonymous? Whether you have a secret or does not, I am sure you wouldn't want your movement or action to be known to some outsider Staying anonymous is a art, if you know how the ISP trace and gather information on you, you can use that knowledge to better protect yourself, a few tools will be needed.
9 canales de YouTube y otras herramientas para aprender a programar con Node.js. Nacido en 2009 de la mano de Ryan Dahl, Node.js es un entorno JavaScript del lado del servidor basado en eventos (asíncrona) que ejecuta JavaScript a velocidades increíbles utilizando el motor V8, creado por Google para Chrome.

¿Su objetivo? Brindar una opción más sencilla para construir programas de red escalables. Fabien Benetou's PIM. Hasta siempre, Navaja Negra - cr0hn.com. s4ur0n. Running the Gauntlet. The Practical Malware Analysis labs can be downloaded using the link below.
WARNING The lab binaries contain malicious code and you should not install or run these programs without first setting up a safe environment. Compatibility The labs are targeted for the Microsoft Windows XP operating system. Many of the labs work on newer versions of Windows, but some of them will not. The labs are designed to mimic realistic malware.
Some of them are well-written code that runs reliable and some of them (just like real malware) are poorly written code that may crash, contain memory leaks, or otherwise behave unexpectedly. ¿Qué certificaciones de ciberseguridad me interesa escoger? National Initiative for Cybersecurity Careers and Studies (NICCS) Explore the NICCS guide to Cybersecurity Certifications Certifications are industry-recognized demonstrations of having a specific skill, or experience in a particular subject area.
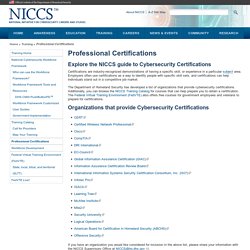
Employers often use certifications as a way to identify people with specific skill sets, and certifications can help individuals stand out in a competitive job market. The Department of Homeland Security has developed a list of organizations that provide cybersecurity certifications. Additionally, you can browse the NICCS Training Catalog for courses that can help prepare you to obtain a certification. The Federal Virtual Training Environment (FedVTE) also offers free courses for government employees and veterans to prepare for certifications.
305 cursos universitarios, online y gratuitos que comienzan en junio. Free Online Social Engineering and Manpulation Training Class from Cybrary. In our free online Social Engineering and Manipulation course, you will learn how to defend against social engineering tactics used by criminal hackers.

By studying how these hackers operate, you can prevent such attacks against your company. Social Engineering and Manipulation – Exploitation of the Human Element. Los hombres que susurran a las máquinas: Anonymous: Verdades y Mentiras. Calendario Laboral Madrid 2016.
VPN. ISO 27000. Join the Alliance. Exams : C)ISSO - Certification Exam. Mile2®'s C)ISSO certification exam is comprised of 100 Questions derived from a larger pool of questions. Also Covers ISC2 CISSP (R) Exam objectives. Description. Free Course Catalog - IT, Cyber Security and Project Management Online Certification Training. Lifehacker - Tips and downloads for getting things done. Comunicado de La PaRTS ante la inminencia de #JuicioAnon y la falta de ética periodística. Game of Hacks. Game of Hacks- Amit Ashbel ON-DEMAND. We created “Game of Hacks”– a viral web app marketed as a tool to train developers on secure coding.
Game of Hacks, built using the node.js framework, displays a range of vulnerable code snippets challenging the player to locate the vulnerability. A multiplayer option makes the challenge even more attractive and the leaderboard spices up things when players compete for a seat on the iron throne. Within 24 hours we had 35K players test their hacking skills...we weren't surprised when users started breaking the rules. Watch the webinar on-demand to: Understand how vulnerabilities were planted within Game of Hacks.See real attack techniques (some caught us off guard) and how we handled them.Learn how to avoid vulnerabilities in your code and how to go about designing a secure application.Hear what to watch out for on the ultra-popular node.js framework.
p3trc.emv2. View in your browser Careers for the inquisitive mind at the Huawei Cyber Security Evaluation Centre. To find out more or to apply, please progress through the SecurityClearedJobs.com website or directly via email to cyber@hcsec.co.uk. Send the answer along with your CV for immediate consideration. Hint:The answer is four bytes long and looks like a word...
Peritus. Periodosmo de datos. Free website evaluation. Unisys. Wemanity - Agile. Network Vulnerability Assessment Training, 4th Batch. Grukul - Launching soon! About CAS. The Jasig Central Authentication Service was originally developed by Yale University. It has since become an Apereo project. Since the availability of the Central Authentication Service server implementation and protocol, there have been many client programs developed for "CASifying" applications such that they can use CAS for user authentication.
Login.
Misc. Tiempo Libre Bruselas. Empleo. Twitter. Pendiente de ver. Liderazgo. News. Cursos online. Get Untangle. Get NG Firewall up and running in no time with these four simple steps. Our base platform is completely free to use, for as long as you need. Download the NG Firewall. Dreamspark. GFCE. Music. Jokes. Misc Online tools. Hobbies. Night Skies – Collections – Google+ Global Forum on Cyber Expertise.
Development. Hacklabs. Dojos. Security. Productivity.