

How Does Google Work? Inside Search – Google. Les 200 paramètres de l’algorithme de Google. Suite à un article très complet de la charmante Ann Smarty, spécialiste du référencement naturel sur le site searchenginejournal.com, qui présente les 200 paramètres de l’algorithme de Google, je sous présente ici une traduction en Français pour que le SEO n’ai plus aucun secret pour vous ! Le domaine… - l’age du domaine - la durée d’enregistrement du domaine - la mise à disposition des information sur l’enregistrement du domaine (nom, adresse, etc.) - l’extension du domaine (extension locale : .fr ou générique : .com) - l’utilisation de sous-domaines - derniers enregistrements du domaine (fréquence de changement de l’ip associée) - derniers propriétaires du domaine (fréquence de changement du propriétaire) - mots clefs dans le nom de domaine.
Interactive online Google tutorial and references. gSeek, search google easier with a simplifed interface. Google Tutor: Tutorials and Tips for Google Users. Google Hacking Database, GHDB, Google Dorks. GHH - The "Google Hack" Honeypot. 100+ Google Tricks That Will Save You Time in School – Eternal Code.
[via onlinecolleges.net] With classes, homework, and projects–not to mention your social life–time is truly at a premium for you, so why not latch onto the wide world that Google has to offer?

7 Clever Google Tricks Worth Knowing. Email Below I have compiled a list of 7 clever Google tricks that I believe everyone should be aware of.
Together I think they represent the apex of the grand possibilities associated with Google search manipulation tricks and hacks. Although there are many others out there, these 7 tricks are my all-time favorite. Enjoy yourself. 1. 2. 40 Google+ Tips and Tricks for Power Users. July 27, 2011, 8:24 AM — Google+ is all the rage right now.

Even under its limited-invite "field trial" phase, the social sharing service is growing in leaps and bounds, with oodles of new users joining every day and even more champing at the bit to get in. Most of us, however, are only beginning to scratch the surface of what Google+ can do; like many Google products, G+ is brimming with advanced features and untapped tweaks. Give me back my GOOGLE™ Fun stuff for Google Earth. How to use Google for Hacking. Google serves almost 80 percent of all search queries on the Internet, proving itself as the most popular search engine.

However Google makes it possible to reach not only the publicly available information resources, but also gives access to some of the most confidential information that should never have been revealed. UPDATED – Using Googles Full Capabilities « XBOX, XBOX 360, PS2, PS3, PSP, & MORE! – Your source for the latest in console modding. Here is an updated version of the ‘Using Google’s Full Capabilities’.
This is basically a master list found on a Russian hacking website. To save you the dangers of going there, we’ve compiled it here. Enjoy. Dorks & hacks Big list. Google Dorks. Cache: If you include other words in the query, Google will highlight those words within the cached document.

For instance, [cache:www.google.com web] will show the cached content with the word “web” highlighted. Google hacking. Basics[edit] The following search query will locate all websites that have the words "admbook" and "version" in the title of the website.
It also checks to ensure that the web page being accessed is a PHP file. intitle:admbook intitle:version filetype:php One can even retrieve the username and password list from Microsoft FrontPage servers by inputting the given microscript in Google search field: "#-Frontpage-" inurl:administrators.pwd Devices connected to the Internet can be found. Another useful search is following intitle:index.of[1] followed by whatever you want to search. Google bomb. A Google bomb on March 31st, 2013.

Despite Google's intervention, some of the first search results still refer to Bush. The terms Google bomb and Googlewashing refer to the practice of causing a web page to rank highly in search engine results for unrelated or off-topic search terms by linking heavily. In contrast, search engine optimization (SEO) is the practice of improving the search engine listings of web pages for relevant search terms. Add-ons Firefox for Google. Things, not strings. Cross-posted on the Inside Search Blog Search is a lot about discovery—the basic human need to learn and broaden your horizons.

But searching still requires a lot of hard work by you, the user. So today I’m really excited to launch the Knowledge Graph, which will help you discover new information quickly and easily. Take a query like [taj mahal]. For more than four decades, search has essentially been about matching keywords to queries. To a search engine the words [taj mahal] have been just that—two words. But we all know that [taj mahal] has a much richer meaning. The Knowledge Graph enables you to search for things, people or places that Google knows about—landmarks, celebrities, cities, sports teams, buildings, geographical features, movies, celestial objects, works of art and more—and instantly get information that’s relevant to your query.
Google’s Knowledge Graph isn’t just rooted in public sources such as Freebase, Wikipedia and the CIA World Factbook. 1. 2. Google hacking master list. This master list of Google Hacking command sets has show up on a forum in Russia, as well as on Scribd.
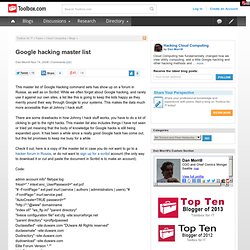
While we often forget about Google hacking, and rarely use it against our own sites, a list like this is going to keep the kids happy as they merrily pound their way through Google to your systems. This makes the data much more accessible than at Johnny I hack stuff. There are some drawbacks in how Johnny I hack stuff works, you have to do a lot of clicking to get to the right hacks. Google HTML/CSS Style Guide. Strictly keep structure (markup), presentation (styling), and behavior (scripting) apart, and try to keep the interaction between the three to an absolute minimum. That is, make sure documents and templates contain only HTML and HTML that is solely serving structural purposes. Move everything presentational into style sheets, and everything behavioral into scripts.
In addition, keep the contact area as small as possible by linking as few style sheets and scripts as possible from documents and templates. Separating structure from presentation from behavior is important for maintenance reasons. It is always more expensive to change HTML documents and templates than it is to update style sheets and scripts. Recherche personnalisée Google - Google Site Search et plus. Centre d'aide Recherche sur le Web. Open directory zoeker.